Critical Infrastructure In this high-stakes year for democracy, the importance of robust election safeguards and national cybersecurity strategies cannot be understated 09 Aug 2024 • , 3 min. read The mention of election security, especially in a year where the majority of the world is destined to vote, brings to mind images of a voting…
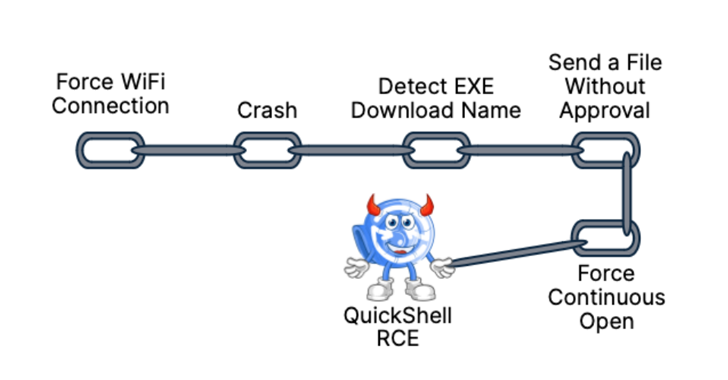
Read MoreAug 10, 2024Ravie LakshmananVulnerability / Mobile Security As many as 10 security flaws have been uncovered in Google’s Quick Share data transfer utility for Android and Windows that could be assembled to trigger remote code execution (RCE) chain on systems that have the software installed. “The Quick Share application implements its own specific application-layer communication…
Read MoreVideo Unsurprisingly, many discussions focused on the implications of the recent CrowdStrike outage, including the lessons it may have offered for bad actors 09 Aug 2024 This week was that time of the year when thousands of cybersecurity experts descended on Las Vegas to attend Black Hat USA, one of the world’s top cybersecurity conferences.…
Read MoreUpdate with further information from Microsoft. Microsoft has disclosed a high-severity vulnerability affecting Office 2016 that could expose NTLM hashes to a remote attacker. Tracked as CVE-2024-38200, this security flaw is caused by an information disclosure weakness that enables unauthorized actors to access protected information. The zero-day impacts multiple 32-bit and 64-bit Office versions, including Office…
Read MoreU.S. law enforcement has arrested two suspected admins of the WWH-Club stolen credit card marketplace after they went on a cash spending spree in Florida. The suspects are Russian national Pavel Kublitskii and Kazakhstan native Alexandr Khodyrev, who were arrested for their roles as administrators and moderators of the cybercrime platform WWH-Club. The two men have…
Read MoreMicrosoft has reminded customers that multiple editions of Windows 11 21H2 and 22H2 will reach the end of servicing in 60 days, on October 8, 2024. The announcement applies to Windows 11 22H2 Home, Pro, Pro Education, Pro for Workstations, and SE editions released on September 20, 2022. On the same day, Windows 11 21H2…
Read MoreAug 10, 2024Ravie LakshmananBrowser Security / Online Fraud An ongoing, widespread malware campaign has been observed installing rogue Google Chrome and Microsoft Edge extensions via a trojan distributed via fake websites masquerading as popular software. “The trojan malware contains different deliverables ranging from simple adware extensions that hijack searches to more sophisticated malicious scripts that…
Read MoreAug 10, 2024Ravie LakshmananVulnerability / Enterprise Security Microsoft has disclosed an unpatched zero-day in Office that, if successfully exploited, could result in unauthorized disclosure of sensitive information to malicious actors. The vulnerability, tracked as CVE-2024-38200 (CVSS score: 7.5), has been described as a spoofing flaw that affects the following versions of Office – Microsoft Office…
Read MoreDeploying low-level malware implants Once an attacker manages to execute malicious code inside the SMM they could potentially inject a persistent malware implant inside the UEFI, but this depends on the platform’s configuration, as UEFI can have additional protections such as AMD’s ROM Armor, which controls access to the SPI flash memory where UEFI is…
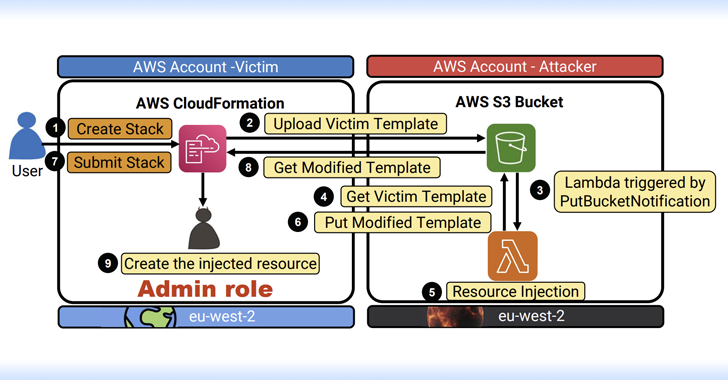
Read MoreAug 09, 2024Ravie LakshmananCloud Security / Data Protection Cybersecurity researchers have discovered multiple critical flaws in Amazon Web Services (AWS) offerings that, if successfully exploited, could result in serious consequences. “The impact of these vulnerabilities range between remote code execution (RCE), full-service user takeover (which might provide powerful administrative access), manipulation of AI modules, exposing…
Read MoreRecent Posts
- Fake AI video generators infect Windows, macOS with infostealers
- T-Mobile confirms it was hacked in recent wave of telecom breaches
- GitHub projects targeted with malicious commits to frame researcher
- NSO Group used another WhatsApp zero-day after being sued, court docs say
- Ingram Micro’s Sahoo: ‘Don’t React To AI.’ Act On AI’