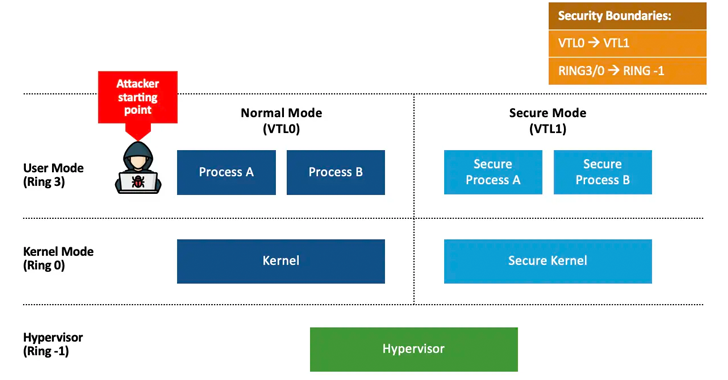
Aug 08, 2024Ravie LakshmananWindows Security / Vulnerability Microsoft said it is developing security updates to address two loopholes that it said could be abused to stage downgrade attacks against the Windows update architecture and replace current versions of the Windows files with older versions. The vulnerabilities are listed below – CVE-2024-38202 (CVSS score: 7.3) –…
Read MoreUnlock the Future of Cybersecurity: Exclusive, Next Era AI Insights and Cutting-Edge Training at SANS Network Security 2024
by nlqip
Aug 08, 2024The Hacker NewsArtificial Intelligence / Network Security The Immersive Experience Happening This September in Las Vegas! In an era of relentless cybersecurity threats and rapid technological advancement, staying ahead of the curve is not just a necessity, but critical. SANS Institute, the premier global authority in cybersecurity training, is thrilled to announce Network…
Read MoreAug 08, 2024Ravie LakshmananVulnerability / Network Security A critical security flaw impacting Progress Software WhatsUp Gold is seeing active exploitation attempts, making it essential that users move quickly to apply the latest. The vulnerability in question is CVE-2024-4885 (CVSS score: 9.8), an unauthenticated remote code execution bug impacting versions of the network monitoring application released…
Read MoreAug 08, 2024Ravie LakshmananCritical Infrastructure / Malware The ransomware strain known as BlackSuit has demanded as much as $500 million in ransoms to date, with one individual ransom demand hitting $60 million. That’s according to an updated advisory from the U.S. Cybersecurity and Infrastructure Security Agency (CISA) and the Federal Bureau of Investigation (FBI). “BlackSuit…
Read MoreAnton Konopliov, founder and CEO of Palma Violets Loans, however, warns that while the proposed rules are beneficial for reducing risk they could “cause chaos” for many firms both on the customer and vendor side around budgets and contractual obligations. “Financial firms will also no longer have the freedom to curate their own contractual terms…
Read More4 Types of Ransomware: Recognizing and Understanding the Threat Last year, ransomware cost firms over $1.1 billion in direct payments. This makes it one of the biggest cybersecurity threats facing businesses of all sizes, and in 2024, this threat has shown no signs of slowing down. Although almost half of recorded incidents in 2023 were…
Read MoreBusiness Security Having knowledgeable leaders at the helm is crucial for protecting the organization and securing the best possible cyber insurance coverage 07 Aug 2024 • , 4 min. read The board does not understand cybersecurity – that’s not so anymore. Prior to the pandemic, the CISO and cybersecurity team were seen as the geeks…
Read MoreGambling blockchain Ronin Network suffered a security incident yesterday when white hat hackers exploited an undocumented vulnerability on the Ronin bridge to withdraw 4,000 ETH and 2 million USDC, totaling $12 million. This figure corresponds to the maximum amount of ETH and USDC that can be withdrawn from the bridge via a single transaction, so…
Read MoreThe SEC has concluded its investigation into Progress Software’s handling of the widespread exploitation of a MOVEit Transfer zero-day flaw that exposed data of over 95 million people. In a new FORM 8-K filing with the SEC, Progress Software says that the SEC’s Division of Enforcement will not recommend any enforcement action regarding the security incident.…
Read MoreIn addition to major product launches, cybersecurity vendors also announced fundings, acquisitions and key hires this week in Las Vegas. Big Moves At Black Hat Along with an abundance of product launches this week in Las Vegas, numerous cybersecurity vendors have announced other major moves in connection with the Black Hat 2024 conference. Security giant…
Read MoreRecent Posts
- Fake AI video generators infect Windows, macOS with infostealers
- T-Mobile confirms it was hacked in recent wave of telecom breaches
- GitHub projects targeted with malicious commits to frame researcher
- NSO Group used another WhatsApp zero-day after being sued, court docs say
- Ingram Micro’s Sahoo: ‘Don’t React To AI.’ Act On AI’