Prioritizing vulnerabilities with context has always been a challenge for vulnerability management teams – and this task isn’t getting easier as published CVEs continue to grow. To remedy this, many enterprises are forced to invest in products and services to protect their environments with various intelligence data and tools. In this blog, we explain how…
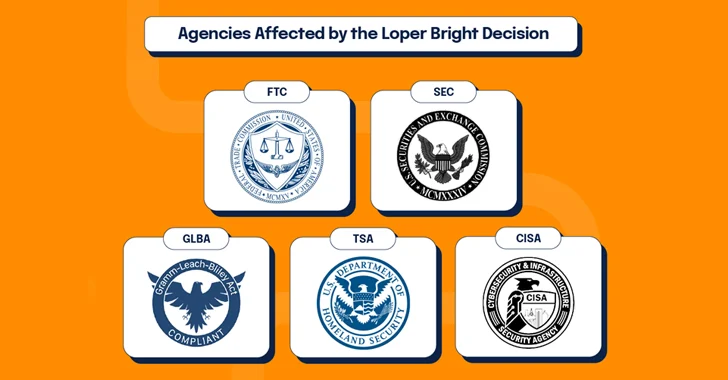
Read MoreAug 05, 2024The Hacker NewsCybersecurity Law / Data Privacy The Loper Bright decision has yielded impactful results: the Supreme Court has overturned forty years of administrative law, leading to potential litigation over the interpretation of ambiguous laws previously decided by federal agencies. This article explores key questions for cybersecurity professionals and leaders as we enter…
Read More“I found a collection of different documents, including voting records, ballot templates, and voter registrations, all from a single county in Illinois,” Fowler said in the report. “Further investigation revealed a total of 13 open databases and 15 others that exist but are not publicly accessible.” The exposed 13 non-password-protected databases contained lists of active…
Read MoreNew Patent Application for Car-to-Car Surveillance Ford has a new patent application for a system where cars monitor each other’s speeds, and then report then to some central authority. Slashdot thread. Tags: cars, patents, police Posted on August 5, 2024 at 7:07 AM • 0 Comments Sidebar photo of Bruce Schneier by Joe MacInnis. Source…
Read MoreIncident response is a structured approach to managing and addressing security breaches or cyber-attacks. Security teams must overcome challenges such as timely detection, comprehensive data collection, and coordinated actions to enhance readiness. Improving these areas ensures a swift and effective response, minimizing damage and restoring normal operations quickly. Challenges in incident response Incident response presents…
Read More“I believe the fix, sorry, I mean workaround for this is to use the Secret Key from the Identity Provider and manually type this into the Authenticator app during setup,” the user wrote. “Unfortunately, this is not very helpful in an enterprise environment, especially when the average end user rarely knows anything about the inner…
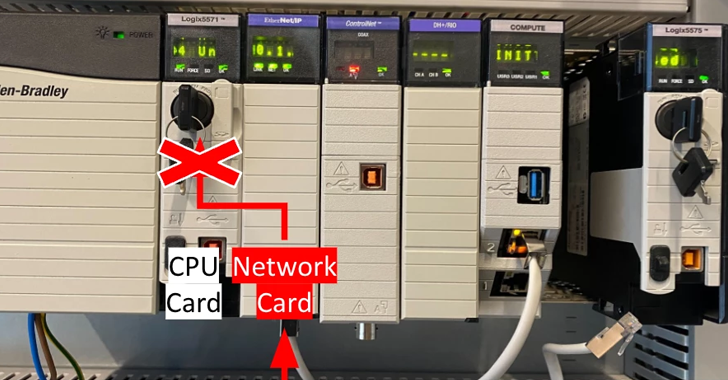
Read MoreAug 05, 2024Ravie LakshmananNetwork Security / Vulnerability A high-severity security bypass vulnerability has been disclosed in Rockwell Automation ControlLogix 1756 devices that could be exploited to execute common industrial protocol (CIP) programming and configuration commands. The flaw, which is assigned the CVE identifier CVE-2024-6242, carries a CVSS v3.1 score of 8.4. “A vulnerability exists in…
Read MoreAs organizations increasingly seek to support and secure more remote network connections, many are rethinking the traditional VPN. Many VPN alternatives exist to help secure remote access — mesh VPNs chief among them. Mesh virtual private networks (VPNs) use a peer-to-peer architecture that can theoretically be less expensive than traditional VPN approaches. VPNs, which are estimated…
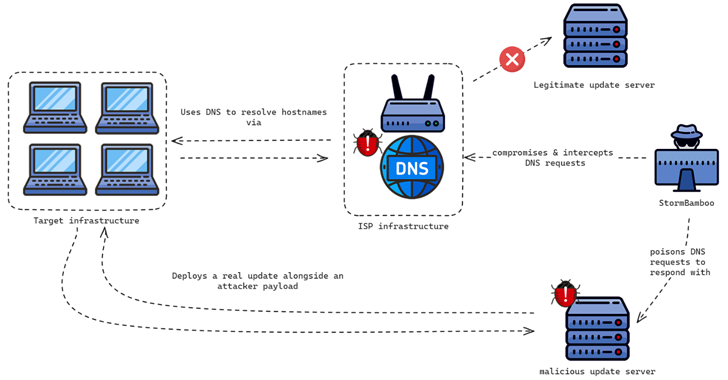
Read MoreAug 05, 2024Ravie LakshmananBrowser Security / Windows Security The China-linked threat actor known as Evasive Panda compromised an unnamed internet service provider (ISP) to push malicious software updates to target companies in mid-2023, highlighting a new level of sophistication associated with the group. Evasive Panda, also known by the names Bronze Highland, Daggerfly, and StormBamboo,…
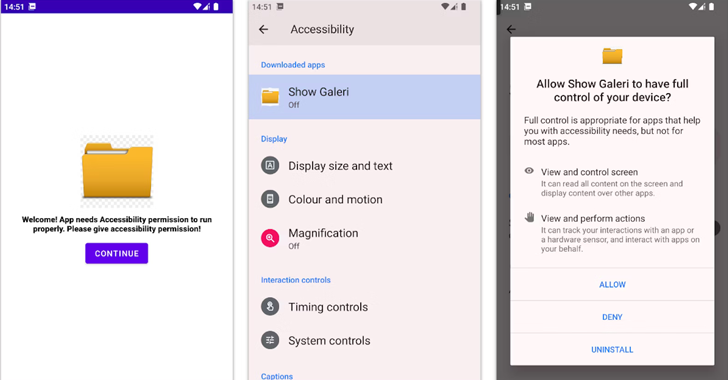
Read MoreAug 05, 2024Ravie LakshmananMobile Security / Financial Security Cybersecurity researchers have discovered a new Android banking trojan called BlankBot targeting Turkish users with an aim to steal financial information. “BlankBot features a range of malicious capabilities, which include customer injections, keylogging, screen recording and it communicates with a control server over a WebSocket connection,” Intel…
Read MoreRecent Posts
- Security plugin flaw in millions of WordPress sites gives admin access
- Phishing emails increasingly use SVG attachments to evade detection
- Fake AI video generators infect Windows, macOS with infostealers
- T-Mobile confirms it was hacked in recent wave of telecom breaches
- GitHub projects targeted with malicious commits to frame researcher