Netrio And Success Computer Consulting Buy New York MSP As Part of ‘Aggressive’ Acquisition Strategy
by nlqip
‘I see us continuing to grow, both organically and through M&A. We’ll expand our service offerings, particularly in AI and automation, which will be key to our long-term strategy,’ says Mark Clayman, CEO of Netrio and Success Computer Consulting. As Netrio and Success Computer Consulting combine their strengths to create a cybersecurity and AI powerhouse,…
Read MoreEvgenii Ptitsyn, a Russian national and suspected administrator of the Phobos ransomware operation, was extradited from South Korea and is facing cybercrime charges in the United States. Phobos is a long-running ransomware-as-a-service (RaaS) operation (derived from the Crysis ransomware family) widely distributed through many affiliates. In 2023, it accounted for roughly 4% of all submissions…
Read MoreCVE-2024-0012, CVE-2024-9474: Zero-Day Vulnerabilities in Palo Alto PAN-OS Exploited In The Wild
by nlqip
Palo Alto Networks confirmed two zero-day vulnerabilities were exploited as part of attacks in the wild against PAN-OS devices, with one being attributed to Operation Lunar Peek. Background On November 18, Palo Alto Networks updated its advisory (PAN-SA-2024-0015) for a critical flaw in its PAN-OS software to include a CVE identifier: CVE Description CVSS CVE-2024-0012…
Read MoreBroadcom warned today that attackers are now exploiting two VMware vCenter Server vulnerabilities, one of which is a critical remote code execution flaw. TZL security researchers reported the RCE vulnerability (CVE-2024-38812) during China’s 2024 Matrix Cup hacking contest. It is caused by a heap overflow weakness in the vCenter’s DCE/RPC protocol implementation and affects products…
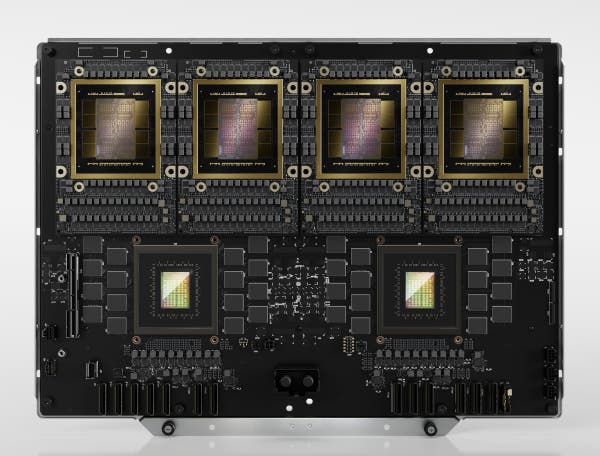
Read MoreAt Supercomputing 2024, the AI computing giant shows off what is likely its biggest AI ‘chip’ yet—the four-GPU Grace Blackwell GB200 NVL4 Superchip—while it announces the general availability of its H200 NVL PCIe module for enterprise servers running AI workloads. Nvidia is revealing what is likely its biggest AI “chip” yet—the four-GPU Grace Blackwell GB200…
Read MoreAWS has released an important new feature that allows you to apply permission boundaries around resources at scale called Resource Control Policies (RCPs). Read on to learn what RCPs are all about and how to use them, as well as how Tenable Cloud Security already factors them into its analysis. AWS just launched Resource Control…
Read MoreFake Bitwarden password manager advertisements on Facebook are pushing a malicious Google Chrome extension that collects and steals sensitive user data from the browser. Bitwarden is a popular password manager app with a “free” tier featuring end-to-end encryption, cross-platform support, MFA integration, and a user-friendly interface. Its user base has been growing steadily in the…
Read More‘We are not going to be successful driving adoption, sales of any of these things without our ecosystem of partners—the service partners, the MSPs, pretty much the entire constituency,’ says Bargav Balakrishnan, IBM vice president of product management for Power. IBM will incorporate its Spyre Accelerator in future Power products—including its Power11 system releasing next…
Read MoreThe Dark Side of Domain-Specific Languages: Uncovering New Attack Techniques in OPA and Terraform
by nlqip
Check out our deep dive into both new and known techniques for abusing infrastructure-as-code and policy-as-code tools. You’ll also learn how to defend against them in this blog post which expands on the attack techniques presented at our fwd:cloudsec Europe 2024 talk “Who Watches the Watchmen? Stealing Credentials from Policy-as-Code Engines (and beyond).” Infrastructure-as-code (IaC)…
Read MoreThe Microsoft 365 Admin Portal is being abused to send sextortion emails, making the messages appear trustworthy and bypassing email security platforms. Sextortion emails are scams claiming that your computer or mobile device was hacked to steal images or videos of you performing sexual acts. The scammers then demand from you a payment of $500…
Read MoreRecent Posts
- CISA Releases the Cybersecurity Performance Goals Adoption Report | CISA
- Multiple vulnerabilities in SonicWall SonicOS could allow a remote attacker to bypass authentication.
- Dell Sales Leader, Former Channel Chief John Byrne Steps Down
- The Dangers of DNS Hijacking
- CES 2025: 15 PC Chips Announced By Intel, Nvidia, AMD And Qualcomm