Trickbot, the latest arrival to the banking malware scene and successor to the infamous Dyre botnet, is in constant flux, and its authors are continually adding new targets and functionality. F5 malware researchers have been monitoring Trickbot and have uncovered a new variant that substantially increases the number of German banks being targeted. Trickbot was…
Read MoreI’ve mentioned before how important strong risk management is to a CISO1. When it comes to risk, the applications our users depend on are a big concern. In a 2016 security survey2 conducted by Ponemon Institute on behalf of F5, a majority of respondents cited security around applications as an area of great concern. It makes…
Read MoreSo far, we’ve seen IoT Distributed Denial-of-Service (DDoS) attacks on a Death Star scale. Even if your organization wasn’t a direct target of these giant barrages, many others were caught up as collateral damage because they had services adjacent or dependent on the direct target. Because of this, many organizations are preparing or strengthening their…
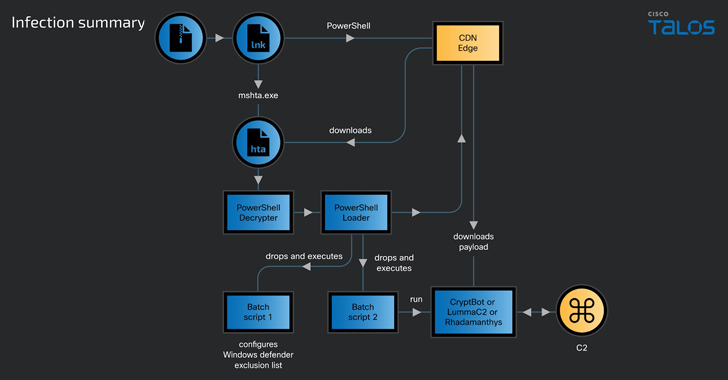
Read MoreApr 24, 2024NewsroomMalware / Data Security A new ongoing malware campaign has been observed distributing three different stealers, such as CryptBot, LummaC2, and Rhadamanthys hosted on Content Delivery Network (CDN) cache domains since at least February 2024. Cisco Talos has attributed the activity with moderate confidence to a threat actor tracked as CoralRaider, a suspected…
Read MoreHi. I’m Mike Convertino, CISO of F5 Networks, and I want to welcome you to an experiment we’re conducting here at F5. We’ve laid the foundation of this CISO to CISO portal on an idea that has traditionally been somewhat controversial in the security community: openness. As you may or may not know, I spent…
Read MoreAutomation Risks There are a number of container and automation frameworks out there that seek to make scale as effortless as the click of a mouse. Some of them are rising quickly due to the excitement over containers, like Mesos and Kubernetes. Others have been around for a while—think Puppet, Chef, VMware, Cisco, and OpenStack.…
Read MoreIn just four short years, a healthy dose of paranoia about individual privacy as well as emerging support for encryption by browsers, social media sites, webmail, and SaaS applications have pushed encryption estimates from almost non-existent (in the low single digits before 2013) to just over 50% by the end of 2016. That’s quite a…
Read MoreCyber security has evolved in ways we never could have imagined. We have more specialized and powerful tools and services today than ever before, security budgets are slowly inching upward, and there are even glimmers of support from management. Yet, with the pace of technological change, the growing “professionalization” of cyber crime, and ever…
Read MoreWhen someone from the IT group gets promoted into security management, a common first lesson is that “geek culture” is ineffective in the boardroom. Just watch one episode of The Big Bang Theory and you’ll recognize the classic nerd character types. Those who behave in that manner tend to get marginalized by executives. We’ve all probably seen…
Read MoreFigure 2: Top domains in a Shodan search for CVE-2014-0160 on January 22, 2017 That’s disconcerting because there is a tendency to “fire and forget” in the public cloud, and concerns over understanding the shared responsibility model of public cloud have been previously voiced. This remains my favorite quote, from AWS head of global…
Read MoreRecent Posts
- False claims of hacked voter data – Week in security with Tony Anscombe
- Versa Networks Releases Advisory for a Vulnerability in Versa Director, CVE-2024-45229 | CISA
- Qualcomm Reportedly Approached Intel About Takeover Deal
- Dell Investigating Hacker Claims: What To Know
- Microsoft ends development of Windows Server Update Services (WSUS)