Developers, engineers, and end users across the organization and broader ecosystem often create NHIs and grant them access without a deep understanding of the implications of these long-lived credentials, their level of access, and their potential exploitation by malicious actors — without the governance or involvement of security teams. The implications of this is manifesting…
Read MoreWhat Cisco Talos researches found was that the most frequently imitated brand worldwide by cybercriminals was by far Microsoft, followed by DocuSign and Amazon in second and third place. PayPal, Adobe, and Instagram also rank in the top 10, along with Nortonlifelock, Chase, Geek Squad, and Home Depot, according to Cisco Talos. The illegal use…
Read MoreFake web browser updates are being used to deliver remote access trojans (RATs) and information stealer malware such as BitRAT and Lumma Stealer (aka LummaC2). “Fake browser updates have been responsible for numerous malware infections, including those of the well-known SocGholish malware,” cybersecurity firm eSentire said in a new report. “In April 2024, we observed…
Read MoreSnowflake: ‘No Evidence’ Linking Product To Ticketmaster Breach, But Signs Former Employee Account Accessed
by nlqip
“We have no evidence suggesting this activity was caused by any vulnerability, misconfiguration, or breach of Snowflake’s product,” according to the vendor. Snowflake has responded to reports that Ticketmaster and Santander Bank were breached through the data cloud vendor, saying in a Friday blog post, “We have no evidence suggesting this activity was caused by…
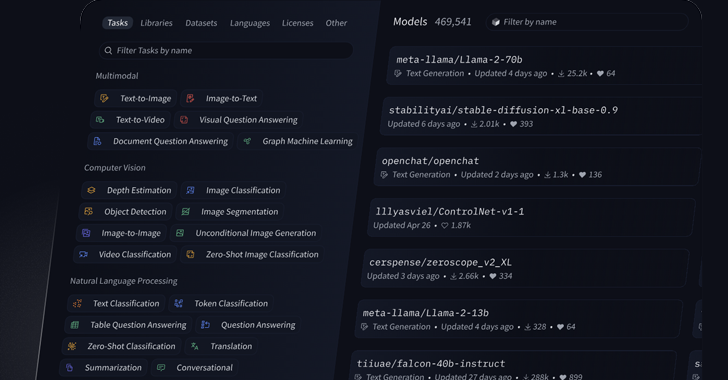
Read MoreAI platform Hugging Face says that its Spaces platform was breached, allowing hackers to access authentication secrets for its members. Hugging Face Spaces is a repository of AI apps created and submitted by the community’s users, allowing other members to demo them. “Earlier this week our team detected unauthorized access to our Spaces platform, specifically…
Read MoreSpanish police have dismantled a network of illegal media content distribution that, since the start of its operations in 2015, has made over $5,700,000. The investigation began in November 2022 following a complaint submitted by the Alliance for Creativity and Entertainment (ACE), which reported two web pages for violations of intellectual property rights. Those sites hosted…
Read MoreGoogle is continuing with its plan to phase out Manifest V2 extensions in Chrome starting in early June 2024, weakening the abilities of ad blockers. Google says this decision was made based on the community’s progress and feedback, which were deemed satisfactory to continue without further delays. Starting June 3, 2024, with Chrome version 127,…
Read MoreKaspersky has released a new virus removal tool named KVRT for the Linux platform, allowing users to scan their systems and remove malware and other known threats for free. The security firm notes that despite the common misconception that Linux systems are intrinsically secure from threats, there has been a constant supply of “in the wild” examples…
Read MoreJun 01, 2024NewsroomAI-as-a-Service / Data Breach Artificial Intelligence (AI) company Hugging Face on Friday disclosed that it detected unauthorized access to its Spaces platform earlier this week. “We have suspicions that a subset of Spaces’ secrets could have been accessed without authorization,” it said in an advisory. Spaces offers a way for users to create,…
Read MoreVideo A woman in London has been misidentified as a shoplifter by a facial recognition system amid fresh concerns over the technology’s accuracy and reliability 31 May 2024 A woman from London has been wrongly accused of being a shoplifter after being flagged by a facial-recognition system, the BBC reports. The tech, called Facewatch, is…
Read MoreRecent Posts
- Fake AI video generators infect Windows, macOS with infostealers
- T-Mobile confirms it was hacked in recent wave of telecom breaches
- GitHub projects targeted with malicious commits to frame researcher
- NSO Group used another WhatsApp zero-day after being sued, court docs say
- Ingram Micro’s Sahoo: ‘Don’t React To AI.’ Act On AI’