The main contributor was Nvidia’s data center revenue, which more than quintupled in the first quarter from the same period last year, growing 427 percent year-over-year to $22.5 billion. Nvidia once again reported triple-digit growth in revenue and profit in the latest quarter from the same period last year, a sign that demand for the…
Read MoreA data breach involving the Dutch city of Eindhoven left the personal information related to almost all of its citizens exposed. As Eindhovens Dagblad reports, two files containing the personal data of 221,511 inhabitants of Eindhoven were accessible to unauthorised parties for a period of time last year. Everyone who lives in the Netherlands has…
Read MoreCybersecurity Snapshot: EPA Urges Water Plants To Boost Cybersecurity, as OpenSSF Launches Threat Intel Platform for Open Source Software
by nlqip
Check out the EPA’s call for water plants to beef up their cyber defenses. Plus, open source developers have a new platform to share threat intelligence. Moreover, business email compromise attacks prompt alert from U.K.’s cyber agency. And CISA tackles DNS encryption best practices. And much more! Dive into six things that are top of…
Read MoreMay 24, 2024The Hacker NewsCybersecurity Webinar Don’t be fooled into thinking that cyber threats are only a problem for large organizations. The truth is that cybercriminals are increasingly targeting smaller businesses, and they’re getting smarter every day. Join our FREE webinar “Navigating the SMB Threat Landscape: Key Insights from Huntress’ Threat Report,” in which Jamie…
Read MoreJustin Lam, senior research analyst covering information security at S&P Global Market Intelligence, said that tackling security and privacy risks is common practice for businesses and shouldn’t necessarily preclude the use of tools shown to provide benefits to users and businesses. “Enterprises face challenges to balance user privacy, user productivity, internal risk management, surveillance, and compliance,” he…
Read MoreOn the Zero-Day Market New paper: “Zero Progress on Zero Days: How the Last Ten Years Created the Modern Spyware Market“: Abstract: Spyware makes surveillance simple. The last ten years have seen a global market emerge for ready-made software that lets governments surveil their citizens and foreign adversaries alike and to do so more easily…
Read MoreMay 24, 2024NewsroomVulnerability / Browser Security Google on Thursday rolled out fixes to address a high-severity security flaw in its Chrome browser that it said has been exploited in the wild. Assigned the CVE identifier CVE-2024-5274, the vulnerability relates to a type confusion bug in the V8 JavaScript and WebAssembly engine. It was reported by…
Read MoreIntroduction The infamous Colonial pipeline ransomware attack (2021) and SolarWinds supply chain attack (2020) were more than data leaks; they were seismic shifts in cybersecurity. These attacks exposed a critical challenge for Chief Information Security Officers (CISOs): holding their ground while maintaining control over cloud security in the accelerating world of DevOps. The problem was…
Read MoreSpear phishing, as the name implies, involves attempting to catch a specific fish. A spear phishing email includes information specific to the recipient to convince them to take the action the attacker wants them to take. This starts with the recipient’s name and may include information about their job or personal life that the attackers…
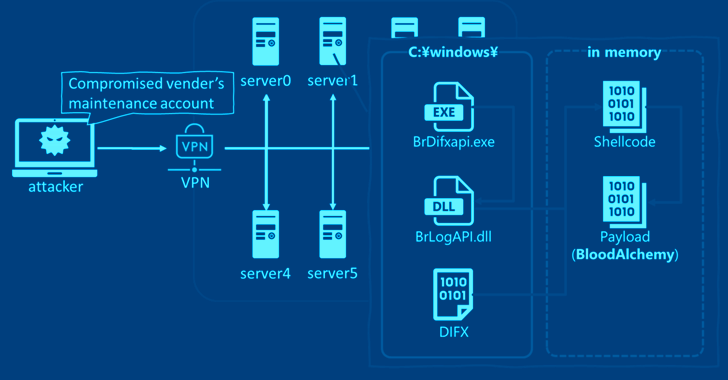
Read MoreMay 24, 2024NewsroomAPT Malware / Cyber Espionage Cybersecurity researchers have discovered that the malware known as BLOODALCHEMY used in attacks targeting government organizations in Southern and Southeastern Asia is in fact an updated version of Deed RAT, which is believed to be a successor to ShadowPad. “The origin of BLOODALCHEMY and Deed RAT is ShadowPad…
Read MoreRecent Posts
- NSO Group used another WhatsApp zero-day after being sued, court docs say
- Ingram Micro’s Sahoo: ‘Don’t React To AI.’ Act On AI’
- Botnet exploits GeoVision zero-day to install Mirai malware
- FTC reports 50% drop in unwanted call complaints since 2021
- Bitfinex hacker gets 5 years in prison for 120,000 bitcoin heist