May 24, 2024NewsroomSupply Chain Attack / Malware Malicious actors have backdoored the installer associated with courtroom video recording software developed by Justice AV Solutions (JAVS) to deliver malware that’s associated with a known backdoor called RustDoor. The software supply chain attack, tracked as CVE-2024-4978, impacts JAVS Viewer v8.3.7, a component of the JAVS Suite 8…
Read MoreGoogle has released a new emergency security update to address the eighth zero-day vulnerability in Chrome browser confirmed to be actively exploited in the wild. The security issue was discovered internally by Google’s Clément Lecigne and is tracked as CVE-2024-5274. It is a high-severity ‘type confusion’ in V8, Chrome’s JavaScript engine responsible for executing JS…
Read MoreBut incidents such as these quickly lead to a loss of trust in the cybercriminal world and partners will quickly move on to the next program. This effect has been visible in LockBit’s recent activity. According to GuidePoint’s statistics, LockBit still accounted for 60% of ransomware incidents in March, but its market share dropped to…
Read MoreLogRhythm and Exabeam announce plan to merge May 15: Security intelligence and analytics firm LogRhythm, owned by private equity investment firm Thoma Bravo, will merge with competitor Exabeam, a provider of AI-driven security operations. “The combined company will leverage the complementary strengths from each organization to take AI-driven security operations to new heights,” Thoma Bravo…
Read MoreESET Research Available as both an IDA plugin and a Python script, Nimfilt helps to reverse engineer binaries compiled with the Nim programming language compiler by demangling package and function names, and applying structs to strings 23 May 2024 • , 5 min. read The Nim programming language has become increasingly attractive to malware developers…
Read MoreMicrosoft has released an emergency out-of-band (OOB) update for Windows Server 2019 that fixes a bug causing 0x800f0982 errors when attempting to install the May 2024 Patch Tuesday security updates. As reported by BleepingComputer last week, many system administrators have reported that they could not install this month’s Patch Tuesday security updates, receiving a 0x800f0982 when attempting to do so. “Yep, 6…
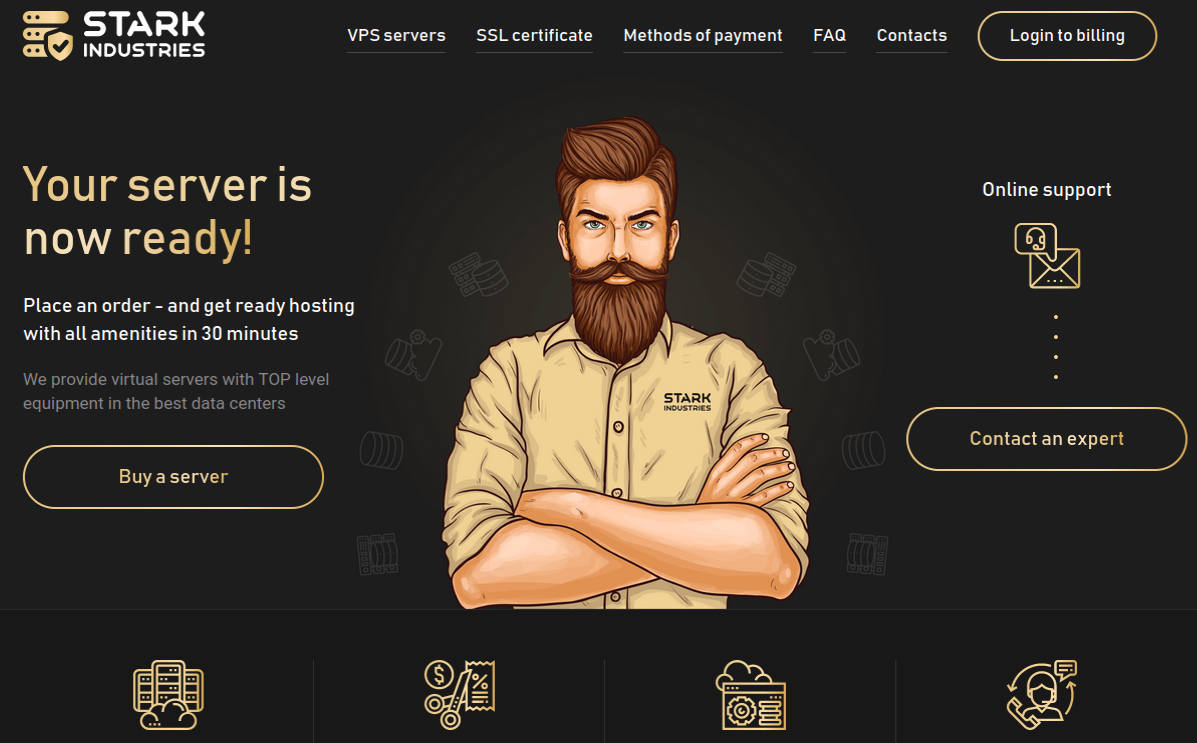
Read MoreThe homepage of Stark Industries Solutions. Two weeks before Russia invaded Ukraine in February 2022, a large, mysterious new Internet hosting firm called Stark Industries Solutions materialized and quickly became the epicenter of massive distributed denial-of-service (DDoS) attacks on government and commercial targets in Ukraine and Europe. An investigation into Stark Industries reveals it is…
Read MoreThe British Government is proposing sweeping change in its approach to ransomware attacks, proposing mandatory reporting by victims and licensing regime for all payments. Read more in my article on the Exponential-e blog. Source link lol
Read MoreMS-ISAC ADVISORY NUMBER: 2024-060 DATE(S) ISSUED: 05/23/2024 OVERVIEW: A vulnerability has been discovered in GitHub Enterprise Server (GHES), which could allow for authentication bypass. GHES is a popular platform for software developers. Organizations can build and store software applications using Git version control and automate deployment pipelines. Successful exploitation of this vulnerability could allow for…
Read MoreArtificial intelligence (AI) holds significant promise to increase productivity across business functions, and cybersecurity is no exception. Arguably no area of the security operation is more poised to benefit from AI than the security operations center (SOC). Today’s SOC teams manage a constant onslaught of attacks while navigating a complex and fragmented tooling landscape, an…
Read MoreRecent Posts
- NSO Group used another WhatsApp zero-day after being sued, court docs say
- Ingram Micro’s Sahoo: ‘Don’t React To AI.’ Act On AI’
- Botnet exploits GeoVision zero-day to install Mirai malware
- FTC reports 50% drop in unwanted call complaints since 2021
- Bitfinex hacker gets 5 years in prison for 120,000 bitcoin heist