From publicly taking shots at Microsoft to being AWS’ first-ever product manager for Amazon EC2, here are six big things partners and customers need to know about AWS’ new CEO Matt Garman. From being Amazon EC2’s first-ever product manager and helping roll out Amazon Web Services’ first service level agreements, to why Amazon CEO Andy…
Read MoreSecurity researchers discovered two previously unseen backdoors dubbed LunarWeb and LunarMail that were used to compromise a European government’s diplomatic institutions abroad. The pieces of malware have been used to breach the Ministry of Foreign Affairs of a European country with diplomatic missions in the Middle East and have been active since at least 2020. Researchers at cybersecurity…
Read MoreTry Tenable Web App Scanning Enjoy full access to our latest web application scanning offering designed for modern applications as part of the Tenable One Exposure Management platform. Safely scan your entire online portfolio for vulnerabilities with a high degree of accuracy without heavy manual effort or disruption to critical web applications. Sign up now.…
Read MoreThe move is still good news for CSOs looking to better manage application security, she stressed, just not necessarily industry-moving. “They are absolutely solving a problem but I don’t think the marketplace aspect of it is that interesting. I think they wanted to highlight 100 integrations out of the box. That is solid and it…
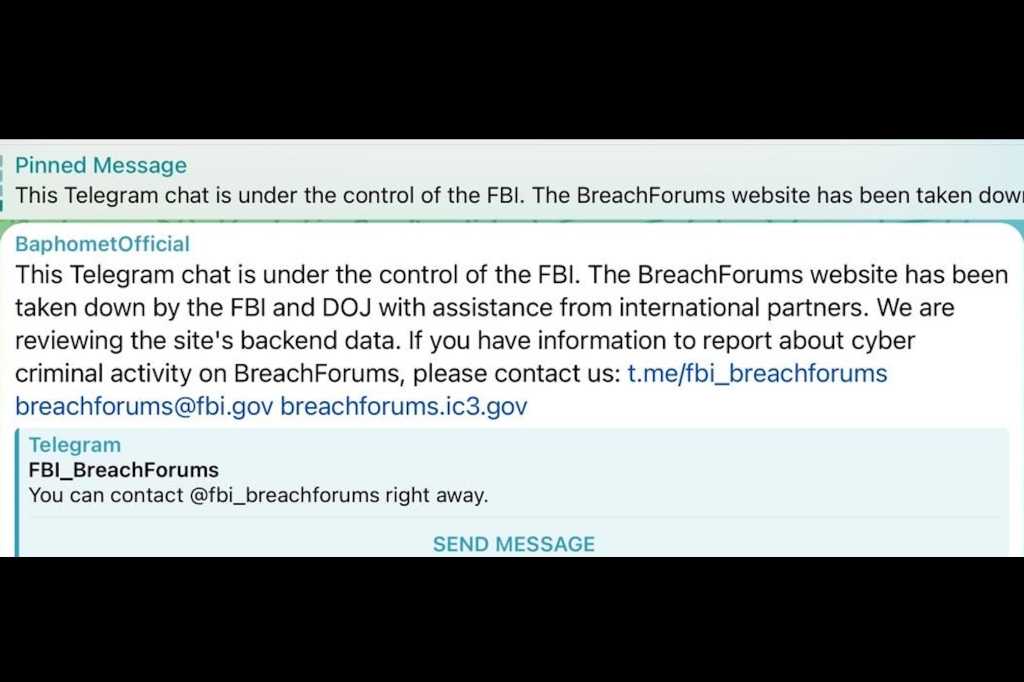
Read MoreBreachForums seized! One of the world’s largest hacking forums is taken down by the FBI… again
by nlqip
Law enforcement agencies worldwide have coordinated to take down one of the world’s largest hacker forums, scoring a victory against cybercrime. BreachForums, a notorious marketplace for stolen data, was seized by the authorities on Wednesday, according to a message on its website. BREACHFORUMS IS UNDER THE CONTROL OF THE FBIThis website has been taken…
Read MoreCisco has released security updates to address vulnerabilities in Cisco software. A cyber threat actor could exploit some of these vulnerabilities to take control of an affected system. Users and administrators are encouraged to review the following advisories and apply necessary updates:• Cisco Crosswork Network Services Orchestrator• Cisco Crosswork Network Services Orchestrator Privilege Escalation• ConfD…
Read MoreMicrosoft has acknowledged a new known issue causing this month’s KB5037765 security update for Windows Server 2019 to fail to install with 0x800f0982 errors. “Windows servers attempting to install the May 2024 security update (KB5037765), released May 14, 2024, might face issues during the installation process,” Microsoft explains on the Windows health dashboard. “The installation…
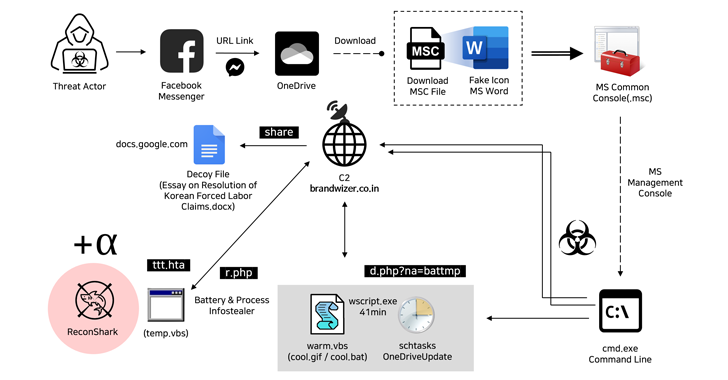
Read MoreMay 16, 2024NewsroomMalware / Cyber Espionage The North Korea-linked Kimsuky hacking group has been attributed to a new social engineering attack that employs fictitious Facebook accounts to targets via Messenger and ultimately delivers malware. “The threat actor created a Facebook account with a fake identity disguised as a public official working in the North Korean…
Read MoreThe seizure comes two days after IntelBroker, a prominent hacker on BreachForums, put up for sale some classified data stolen from one of Europol’s websites. The FBI’s claim that it is reviewing the hacking forum’s backend data is raising speculation regarding its possession of forum members’ email addresses, IP addresses, and private messages. “While details…
Read MoreThe North Korean hacker group Kimsuki has been using a new Linux malware called Gomir that is a version of the GoBear backdoor delivered via trojanized software installers. Kimsuky is a state-sponsored threat actor linked to North Korea’s military intelligence, the Reconnaissance General Bureau (RGB). In early February 2024, researchers at the SW2 threat intelligence company…
Read MoreRecent Posts
- Safeguarding Healthcare Organizations from IoMT Risks
- Broadcom’s VMware Issues ‘Top of Mind’ For Partners, Nutanix Channel Chief Says
- Microsoft just killed the Windows 10 Beta Channel again
- Fraud network uses 4,700 fake shopping sites to steal credit cards
- CISA warns of more Palo Alto Networks bugs exploited in attacks