Using Legitimate GitHub URLs for Malware Interesting social-engineering attack vector: McAfee released a report on a new LUA malware loader distributed through what appeared to be a legitimate Microsoft GitHub repository for the “C++ Library Manager for Windows, Linux, and MacOS,” known as vcpkg. The attacker is exploiting a property of GitHub: comments to a…
Read MoreConclusions This month we were able to add seven newly observed CVEs to our list of confirmed exploited vulnerabilities: CVE-2012-4940, a directory traversal vulnerability in the Axigen Free Mail Server. CVE-2016-4945, a cross-site scripting flaw in Citrix Netscaler Gateway CVE-2017-11511 and CVE-2017-11512, arbitrary file download flaws at different URIs in the Zoho ManageEngine ServiceDesk tool…
Read MoreTo find the correct password, attackers must check word after word until they find one which outputs the same hash value as the one they have stolen. While this sounds tedious, password cracking tool, such as Hashcat, are capable of calculating billions of hashes per second on a single computer. Renting cloud computing services allows…
Read MoreThe Chrome search contest 2020 scam is a browser based advertisement that states pretends to be from Google and states that you made the 5-billionth search. Due to this, you won rewards such as an Apple Watch, a $1,000 gift certificate to Amazon, or a $1,000 gift certificate to Apple. This is a scam that…
Read MorePowerHouse Data Centers launched in 2022. It is owned by American Real Estate Partners. Its two newest projects in Reno and Viriginia are supported by $1 billion investment from Harrison Street JV. PowerHouse Data Centers has two massive projects underway to begin the new year, with a three-building site under development in Reno, Nevada, as…
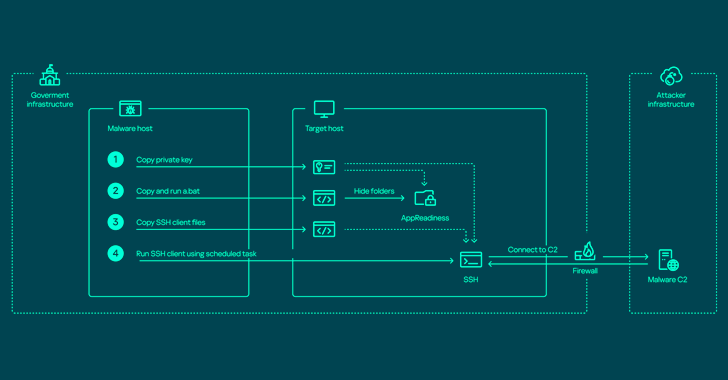
Read MoreApr 22, 2024NewsroomNetwork Security / Endpoint Security The threat actor known as ToddyCat has been observed using a wide range of tools to retain access to compromised environments and steal valuable data. Russian cybersecurity firm Kaspersky characterized the adversary as relying on various programs to harvest data on an “industrial scale” from primarily governmental organizations,…
Read MoreBroadcom’s board called CEO Hock Tan the company’s ‘driving force,’ while three other executives won praise for their work moving the company’s $69 billion deal to buy VMware through regulators around the world. Compensation for these executives increased 211 percent year over year, from $77 million in 2022 to $242 million in 2023. Broadcom CEO…
Read MoreThe 2021 Application Protection report notes that ransomware was a factor in roughly 30 percent of U.S. breaches in 2020. Looking at the breach analyses, we found some of the most important controls were user account management, network segmentation, and data backup. We realize that implementing these controls can be difficult, so this article goes…
Read MoreCybersecurity Trends For 2019: The Year of the Intelligent Security The rise of cyberattacks in recent years has transformed cybersecurity into a top priority for businesses. Furthermore, these attacks have been targeting indiscriminately not only small businesses and users, but large firms and national institutions. The need for cybersecurity solutions has transformed the sector into a…
Read MoreTABLACUSAPP.EXE Information This is an undesirable program. This file has been identified as a program that is undesirable to have running on your computer. This consists of programs that are misleading, harmful, or undesirable. If the description states that it is a piece of malware, you should immediately run an antivirus and antispyware program. If…
Read MoreRecent Posts
- Arm To Seek Retrial In Qualcomm Case After Mixed Verdict
- Jury Sides With Qualcomm Over Arm In Case Related To Snapdragon X PC Chips
- Equinix Makes Dell AI Factory With Nvidia Available Through Partners
- AMD’s EPYC CPU Boss Seeks To Push Into SMB, Midmarket With Partners
- Fortinet Releases Security Updates for FortiManager | CISA