The semiconductor giant confirmed to CRN last week that it initiated a new round of layoffs in the Sales and Marketing Group, which is led by Christoph Schell, as part of a reorganization. Intel’s recent round of layoffs in the Sales and Marketing Group will impact roughly 62 positions at the company’s headquarters in Santa…
Read MoreHerve Tardy, who has spent more than half of his 30 years in the data center power management industry leading the channel charge at Eaton, has departed the company, leaving behind a legacy of strong channel advocacy. Long-time Eaton channel chief Hervé Tardy Monday spent his last day at the power management company, according to…
Read MoreAs part of CRN’s 2024 Internet Of Things 50 list, here are the 10 coolest IoT networking connectivity companies that are offering innovative connectivity options to help devices connect to networks, communicate, and share their valuable data to various business systems. Global IoT spending is expected to continue growing for the years to come, and…
Read More‘We will do another 20 or 25 roll-ups this year. This latest acquisition makes 29 acquisitions for us. And so thinking about 25 acquisitions in 2024 is not crazy. Realistically, if we take out the last two months where we didn’t make an acquisition, we did those 29 in like 14 months. We’re gluttons for…
Read More‘The facts that our investigation uncovered were egregious. We look forward to presenting our evidence and proving our claims in the litigation,’ Tyler Wall, Nutanix’s chief legal officer, said in a statement. Three former Nutanix employees who developed its Era database management product left the company and, opened a competitor 18 months later that sold…
Read MoreFrom 66degrees and Quantiphi to World Wide Technology and Deloitte, here are 11 top Google partners that won Google Cloud’s 2024 Partner of the Year Award in areas like sales, services and expansion. Although there are thousands of Google Cloud channel partners in North America, only a select few won the cloud company’s prestigious Partner…
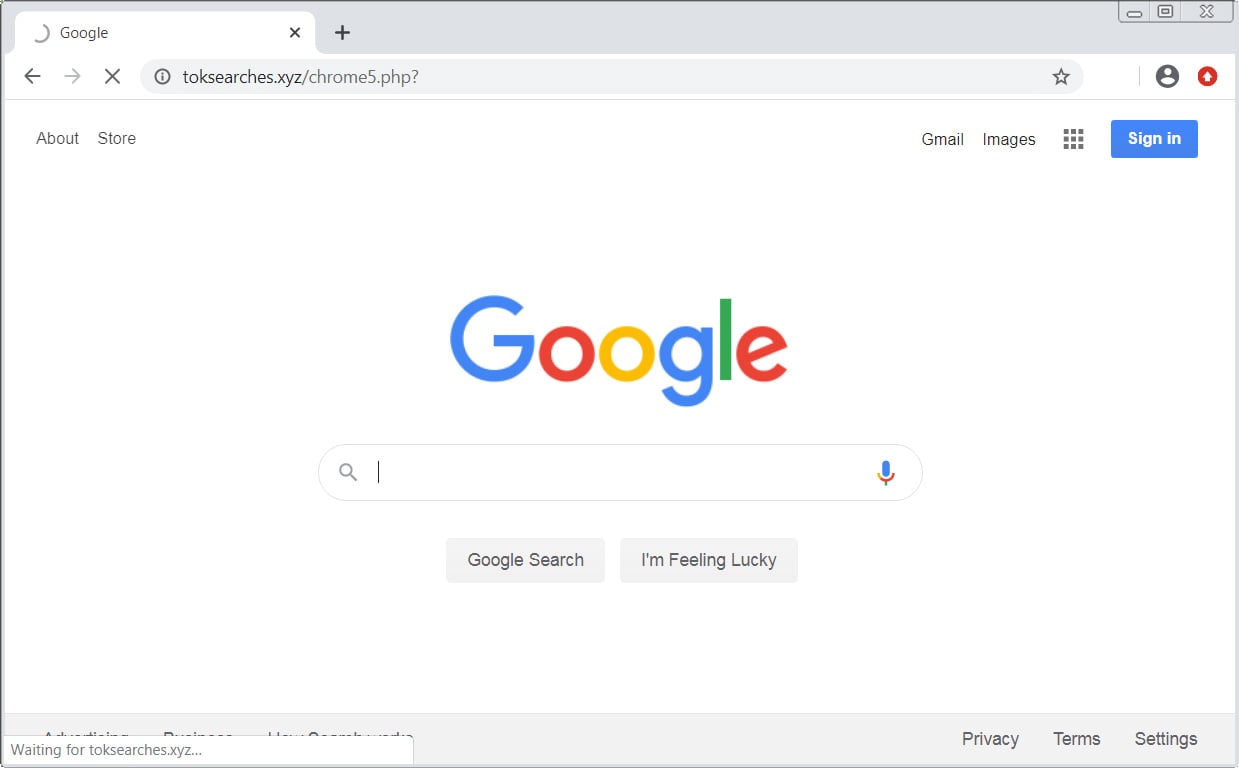
Read MoreIn order to remove Toksearches.xyz completely you will need to reset Chrome back to its initial settings. Doing these steps will erase all configuration information from Chrome such as your home page, tab settings, saved form information, browsing history, and cookies. This process will also disable any installed extensions. All of your bookmarks, though, will…
Read MoreDisclaimer It is assumed that users are familiar with the operating system they are using and comfortable with making the suggested changes. BleepingComputer.com will not be held responsible if changes you make cause a system failure. This is NOT a list of tasks/processes taken from Task Manager or the Close Program window (CTRL+ALT+DEL) but a…
Read MoreGartner recognizes 10 security service edge (SSE) vendors in its latest Magic Quadrant ranking for the cybersecurity category. Netskope, Palo Alto Networks and Zscaler once again appeared in the sought-after “Leaders” quadrant in the 2024 Gartner Magic Quadrant for security service edge (SSE) vendors, according to the report released Thursday. The three vendors in the…
Read More‘When you look at the whole class of ecosystem that’ll be built around AI, it’ll be one of the most exciting ecosystem shuffles in adding value that we’ve seen,’ Red Hat CEO Matt Hicks tells CRN. Red Hat CEO Matt Hicks told CRN that channel partners have an immense opportunity to add value and drive…
Read MoreRecent Posts
- Arm To Seek Retrial In Qualcomm Case After Mixed Verdict
- Jury Sides With Qualcomm Over Arm In Case Related To Snapdragon X PC Chips
- Equinix Makes Dell AI Factory With Nvidia Available Through Partners
- AMD’s EPYC CPU Boss Seeks To Push Into SMB, Midmarket With Partners
- Fortinet Releases Security Updates for FortiManager | CISA