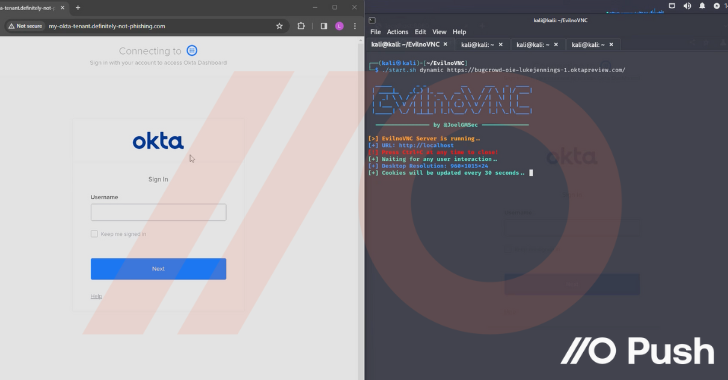
Attackers are increasingly making use of “networkless” attack techniques targeting cloud apps and identities. Here’s how attackers can (and are) compromising organizations – without ever needing to touch the endpoint or conventional networked systems and services. Before getting into the details of the attack techniques being used, let’s discuss why these attacks are becoming more…
Read MoreUS-based human plasma collector, tester, and supplier Octapharma Plasma may have been experiencing a ransomware attack pushing the company into operational shutdown, according to a report by The Register. An unnamed source familiar with the situation reportedly said that Octapharma Plasma fell victim to a BlackSuit ransomware infection on Monday, disrupting operations for its US-based…
Read MoreApr 19, 2024NewsroomCyber Espionage / Threat Intelligence Government entities in the Middle East have been targeted as part of a previously undocumented campaign to deliver a new backdoor dubbed CR4T. Russian cybersecurity company Kaspersky said it discovered the activity in February 2024, with evidence suggesting that it may have been active since at least a…
Read MoreThe vulnerability impacts the Cisco 5000 Series Enterprise Network Compute Systems (ENCS), Catalyst 8300 Series Edge uCPE, UCS C-Series Rack Servers in standalone mode and UCS E-Series Servers in default configurations. Many other products and appliances that are based on UCS C-Series servers are also affected if the IMC CLI was explicitly configured to be…
Read MoreToday, CISA, the Federal Bureau of Investigation (FBI), Europol’s European Cybercrime Centre (EC3), and the Netherlands’ National Cyber Security Centre (NCSC-NL) released a joint Cybersecurity Advisory (CSA), #StopRansomware: Akira Ransomware, to disseminate known Akira ransomware tactics, techniques, and procedures (TTPs) and indicators of compromise (IOCs) identified through FBI investigations as recently as February 2024. Evolving…
Read MoreThreat Actors Exploit Multiple Vulnerabilities in Ivanti Connect Secure and Policy Secure Gateways | CISA
by nlqip
SUMMARY The Cybersecurity and Infrastructure Security Agency (CISA) and the following partners (hereafter referred to as the authoring organizations) are releasing this joint Cybersecurity Advisory to warn that cyber threat actors are exploiting previously identified vulnerabilities in Ivanti Connect Secure and Ivanti Policy Secure gateways. CISA and authoring organizations appreciate the cooperation of Volexity, Ivanti,…
Read MoreSUMMARY Note: This joint Cybersecurity Advisory (CSA) is part of an ongoing #StopRansomware effort to publish advisories for network defenders that detail various ransomware variants and ransomware threat actors. These #StopRansomware advisories include recently and historically observed tactics, techniques, and procedures (TTPs) and indicators of compromise (IOCs) to help organizations protect against ransomware. Visit stopransomware.gov to…
Read MorePolice have successfully infiltrated and disrupted the fraud platform “LabHost”, used by more than 2,000 criminals to defraud victims worldwide. A major international operation, led by the UK’s Metropolitan Police, has seized control of LabHost, which has been helping cybercriminals create phishing websites since 2021 to steal sensitive information like passwords, email addresses, and bank…
Read MoreCISA released three Industrial Control Systems (ICS) advisories on April 18, 2024. These advisories provide timely information about current security issues, vulnerabilities, and exploits surrounding ICS. CISA encourages users and administrators to review the newly released ICS advisories for technical details and mitigations. Source link wse3 wse3 wse3 wse3 wse3 wse3 wse3 wse3 wse3 wse3…
Read MoreThe international hotel chain Omni Hotels & Resorts has confirmed that a cyberattack last month saw it shut down its systems, with hackers stealing personal information about its customers. In the aftermath of the attack, hotel guests reported that they had been forced to check in on paper, that room keys didn’t work, and all…
Read MoreRecent Posts
- Arm To Seek Retrial In Qualcomm Case After Mixed Verdict
- Jury Sides With Qualcomm Over Arm In Case Related To Snapdragon X PC Chips
- Equinix Makes Dell AI Factory With Nvidia Available Through Partners
- AMD’s EPYC CPU Boss Seeks To Push Into SMB, Midmarket With Partners
- Fortinet Releases Security Updates for FortiManager | CISA