If a company decides that it will not report certain information at this time, the company should do an exercise where it makes the assumption that the unannounced items do get announced. This exercise means that unannounced scenarios can’t be ignored. They must be seriously considered, if for no other reason than to improve the…
Read MoreIn today’s world, where information spreads at lightning speed, it’s easy to fall into the trap of misinformation. Amidst the noise, Google Fact Checking Tools aim to empower you with the ability to distinguish reliable sources from those perpetuating false claims. What are Google Fact Checking Tools? Google offers a suite of tools designed to…
Read MoreArtificial intelligence (AI) is rapidly transforming various industries, and the world of literature is no exception. AI-powered writing assistants are becoming increasingly sophisticated, blurring the lines between human and machine-generated content. This begs the question: can AI write a book in its entirety, and if so, what are the implications for the future of authorship?…
Read More10web — form_maker_by_10web_-_mobile-friendly_drag_&_drop_contact_form_builder The Form Maker by 10Web – Mobile-Friendly Drag & Drop Contact Form Builder plugin for WordPress is vulnerable to Sensitive Information Exposure in all versions up to, and including, 1.15.22 via the signature functionality. This makes it possible for unauthenticated attackers to extract sensitive data including user signatures. 2024-04-09 5.9 CVE-2024-2112security@wordfence.comsecurity@wordfence.com adobe…
Read MoreThe evolution of ransomware attacks continues to pose a significant threat to businesses worldwide as they are becoming increasingly sophisticated. Protecting against ransomware requires robust strategies, including immutable storage targets, encrypted backups, routine backup verification, access limits, proactive monitoring, and comprehensive data recovery planning. These measures are essential for minimizing damage and ensuring quick recovery…
Read MorePalo Alto Networks has released workaround guidance for a command injection vulnerability (CVE-2024-3400) affecting PAN-OS versions 10.2, 11.0, and 11.1. Palo Alto Networks has reported active exploitation of this vulnerability in the wild. CISA encourages users and administrators to review the Palo Alto Networks Security Advisory, apply the current mitigations, and update the affected software…
Read MoreToday, the National Security Agency’s Artificial Intelligence Security Center (NSA AISC) published the joint Cybersecurity Information Sheet Deploying AI Systems Securely in collaboration with CISA, the Federal Bureau of Investigation (FBI), the Australian Signals Directorate’s Australian Cyber Security Centre (ASD ACSC), the Canadian Centre for Cyber Security (CCCS), the New Zealand National Cyber Security Centre…
Read MoreApr 15, 2024NewsroomFirmware Security / Vulnerability A security flaw impacting the Lighttpd web server used in baseboard management controllers (BMCs) has remained unpatched by device vendors like Intel and Lenovo, new findings from Binarly reveal. While the original shortcoming was discovered and patched by the Lighttpd maintainers way back in August 2018 with version 1.4.51,…
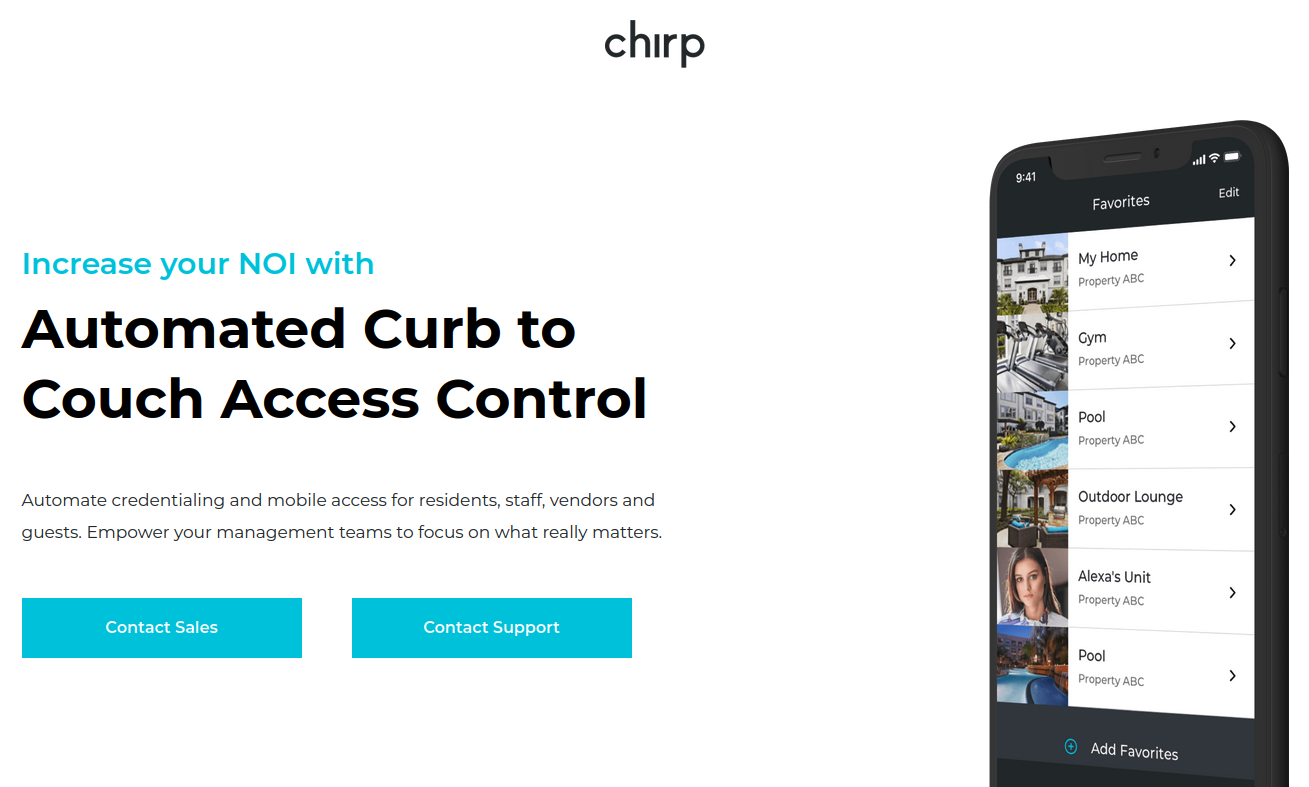
Read MoreThe U.S. government is warning that smart locks securing entry to an estimated 50,000 dwellings nationwide contain hard-coded credentials that can be used to remotely open any of the locks. The lock’s maker Chirp Systems remains unresponsive, even though it was first notified about the critical weakness in March 2021. Meanwhile, Chirp’s parent company, RealPage,…
Read MoreApr 15, 2024NewsroomCloud Security /SaaS Security The threat actor known as Muddled Libra has been observed actively targeting software-as-a-service (SaaS) applications and cloud service provider (CSP) environments in a bid to exfiltrate sensitive data. “Organizations often store a variety of data in SaaS applications and use services from CSPs,” Palo Alto Networks Unit 42 said…
Read MoreRecent Posts
- Arm To Seek Retrial In Qualcomm Case After Mixed Verdict
- Jury Sides With Qualcomm Over Arm In Case Related To Snapdragon X PC Chips
- Equinix Makes Dell AI Factory With Nvidia Available Through Partners
- AMD’s EPYC CPU Boss Seeks To Push Into SMB, Midmarket With Partners
- Fortinet Releases Security Updates for FortiManager | CISA