Mar 27, 2024NewsroomCyber Espionage / Data Breach Indian government entities and energy companies have been targeted by unknown threat actors with an aim to deliver a modified version of an open-source information stealer malware called HackBrowserData and exfiltrate sensitive information in some cases by using Slack as command-and-control (C2). “The information stealer was delivered via…
Read MoreThe trojan deployed on the system has a wide range of data theft capabilities. It searches for specific directories inside the Opera, Chrome, Brave, Vivaldi, Yandex and Edge browsers and extracts authentication cookies, autofill information, browsing history, bookmarks, credit card information and login credentials. The trojan also attempts to steal files associated with cryptocurrency wallets,…
Read MoreThe content of this post is solely the responsibility of the author. AT&T does not adopt or endorse any of the views, positions, or information provided by the author in this article. Beyond its fundamental port scanning capabilities, Nmap offers a suite of advanced techniques designed to uncover vulnerabilities, bypass security measures, and gather valuable…
Read MoreIn the early days of the pandemic, organizations relied on virtual private networks (VPNs) to link remote employees to their networks. However, legacy VPNs don’t provide the most efficient way to connect to network assets. And now that we’re fully in the age of the hybrid workforce, organizations are looking for a better and more comprehensive approach…
Read MoreApple released security updates to address a vulnerability (CVE-2024-1580) in Safari and macOS. A cyber threat actor could exploit this vulnerability to take control of an affected system. CISA encourages users and administrators to review the following advisories and apply the necessary updates: Source link lol
Read MoreMar 27, 2024NewsroomThreat Intelligence / Network Security The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added a security flaw impacting the Microsoft Sharepoint Server to its Known Exploited Vulnerabilities (KEV) catalog based on evidence of active exploitation in the wild. The vulnerability, tracked as CVE-2023-24955 (CVSS score: 7.2), is a critical remote code execution…
Read MoreIf you hear the term “microbranch,” you probably picture a small banking location with a handful of ATMs. For many years, this term was specific to the financial industry, but as remote work and internet-connected devices have grown more common, the definition has evolved to include any small remote office associated with a larger corporation.…
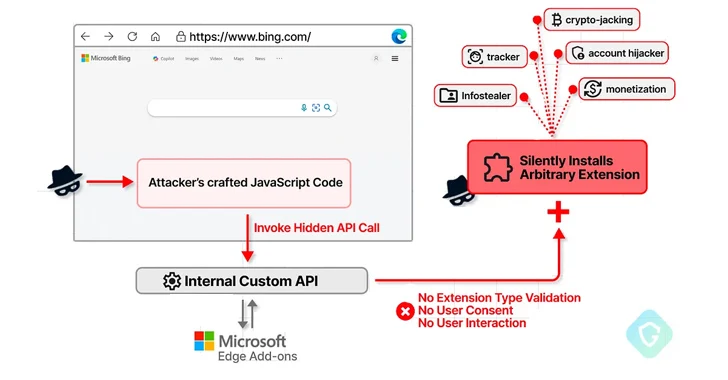
Read MoreMar 27, 2024NewsroomVulnerability / API Security A now-patched security flaw in the Microsoft Edge web browser could have been abused to install arbitrary extensions on users’ systems and carry out malicious actions. “This flaw could have allowed an attacker to exploit a private API, initially intended for marketing purposes, to covertly install additional browser extensions…
Read MoreScams Personal loan scams prey on your financial vulnerability and might even trap you in a vicious circle of debt. Here’s how to avoid being scammed when considering a loan. 26 Mar 2024 • , 6 min. read Times have been tough financially for many of us since the pandemic. Climate shocks, food and energy…
Read More“With Verify API, businesses can customize the verification and authentication experience by market needs, customer preferences, or business priorities with peace of mind—and with automatic multichannel fallback,” the company said in a press release. Verify API also allows custom routing to help customers build routing rules for tailored delivery across all channels and markets. Arms…
Read MoreRecent Posts
- Bob Sullivan Discovers a Scam That Strikes Twice
- A Vulnerability in Apache Struts2 Could Allow for Remote Code Execution
- CISA Adds One Known Exploited Vulnerability to Catalog | CISA
- Xerox To Buy Lexmark For $1.5B In Blockbuster Print Deal
- Vulnerability Summary for the Week of December 16, 2024 | CISA