Feb 20, 2024NewsroomVulnerability / Network Security ConnectWise has released software updates to address two security flaws in its ScreenConnect remote desktop and access software, including a critical bug that could enable remote code execution on affected systems. The vulnerabilities, which currently lack CVE identifiers, are listed below – Authentication bypass using an alternate path or…
Read MoreMeanwhile, key operations of the ransomware gang are seized including access to LockBit’s affiliate panel, a central control panel for LockBit’s affiliate groups to create and modify various LockBit ransomware-as-a-service (RaaS) samples, manage attacks and victims, run attack analytics and publish blog posts. “Law Enforcement has taken control of Lockbit’s platform and obtained all the…
Read MoreThe US National Institute of Standards and Technology (NIST) cybersecurity framework is one of the world’s most important guidelines for securing networks. It can be applied to any number of applications, including SaaS. One of the challenges facing those tasked with securing SaaS applications is the different settings found in each application. It makes it…
Read MoreMicrosoft Is Spying on Users of Its AI Tools Microsoft announced that it caught Chinese, Russian, and Iranian hackers using its AI tools—presumably coding tools—to improve their hacking abilities. From their report: In collaboration with OpenAI, we are sharing threat intelligence showing detected state affiliated adversaries—tracked as Forest Blizzard, Emerald Sleet, Crimson Sandstorm, Charcoal Typhoon,…
Read MoreFeb 20, 2024The Hacker NewsWebinar / Incident Response In the tumultuous landscape of cybersecurity, the year 2023 left an indelible mark with the brazen exploits of the Scattered Spider threat group. Their attacks targeted the nerve centers of major financial and insurance institutions, culminating in what stands as one of the most impactful ransomware assaults…
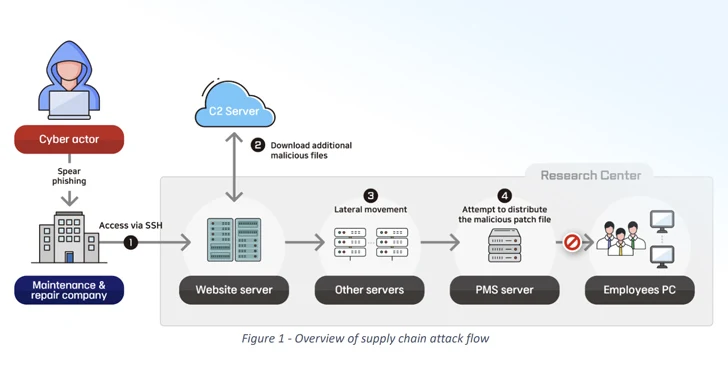
Read MoreFeb 20, 2024NewsroomHacking / Cyber Espionage The North Korean state-sponsored threat actors have been attributed to a cyber espionage campaign targeting the defense sector across the world. In a joint advisory published by Germany’s Federal Office for the Protection of the Constitution (BfV) and South Korea’s National Intelligence Service (NIS), the agencies said the goal…
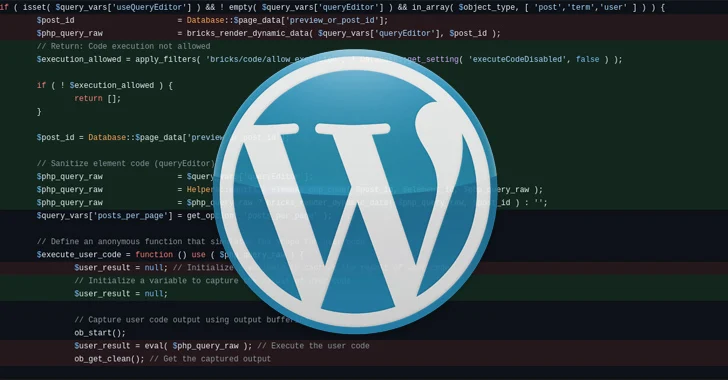
Read MoreFeb 20, 2024NewsroomWebsite Security / PHP Code A critical security flaw in the Bricks theme for WordPress is being actively exploited by threat actors to run arbitrary PHP code on susceptible installations. The flaw, tracked as CVE-2024-25600 (CVSS score: 9.8), enables unauthenticated attackers to achieve remote code execution. It impacts all versions of the Bricks…
Read MoreSome of the first phishing took place in the early 1990s when hackers used fake screen names to pose as AOL administrators and steal sensitive information via AOL Instant Messenger. Phishing really blew up in 2000, when an email with the subject line “ILOVEYOU” duped millions of people into clicking on an attachment loaded with…
Read MoreHackers backed by Iran and Hezbollah staged cyber attacks designed to undercut public support for the Israel-Hamas war after October 2023. This includes destructive attacks against key Israeli organizations, hack-and-leak operations targeting entities in Israel and the U.S., phishing campaigns designed to steal intelligence, and information operations to turn public opinion against Israel. Iran accounted…
Read MoreFeb 20, 2024NewsroomDark Web / Cybercrime An international law enforcement operation has led to the seizure of multiple darknet domains operated by LockBit, one of the most prolific ransomware groups, marking the latest in a long list of digital takedowns. While the full extent of the effort, codenamed Operation Cronos, is presently unknown, visiting the…
Read MoreRecent Posts
- Lumen Technologies CEO: ‘We’re Building The Backbone For The AI Economy’
- 9 Steps to Get CTEM on Your 2025 Budgetary Radar
- INTERPOL Disrupts Over 22,000 Malicious Servers in Global Crackdown on Cybercrime
- Singtel Hack Highlights Rising Threat of Chinese Cyber Attacks on Global Telecoms
- South Korea Fines Meta $15.67M for Illegally Sharing Sensitive User Data with Advertisers