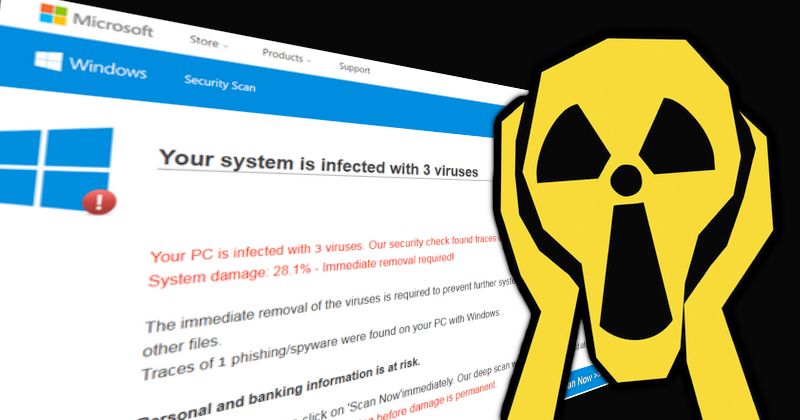
Two firms have been fined $26 million by the US Federal Trade Commission (FTC) for scaring consumers into believing their computers were infected by malware. The FTC claimed that Restoro Cyprus Limited and Reimage Cyprus Limited, both based in Cyprus, operated a tech support scam since at least 2018 that “bilked tens of millions of…
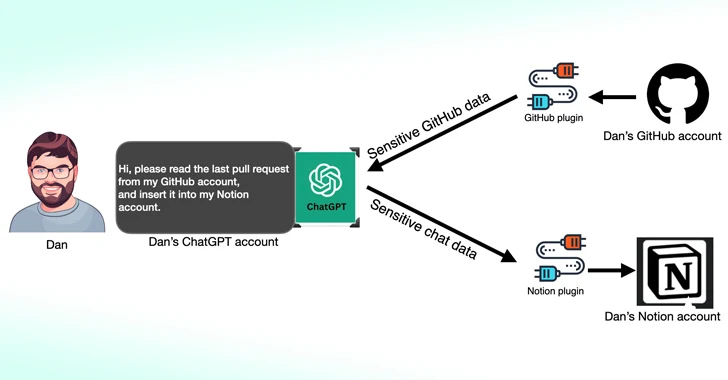
Read MoreMar 15, 2024NewsroomData Privacy / Artificial Intelligence Cybersecurity researchers have found that third-party plugins available for OpenAI ChatGPT could act as a new attack surface for threat actors looking to gain unauthorized access to sensitive data. According to new research published by Salt Labs, security flaws found directly in ChatGPT and within the ecosystem could…
Read MoreImproving C++ C++ guru Herb Sutter writes about how we can improve the programming language for better security. The immediate problem “is” that it’s Too Easy By Default™ to write security and safety vulnerabilities in C++ that would have been caught by stricter enforcement of known rules for type, bounds, initialization, and lifetime language safety.…
Read MoreMar 15, 2024NewsroomBrowser Security / Phishing Attack Google on Thursday announced an enhanced version of Safe Browsing to provide real-time, privacy-preserving URL protection and safeguard users from visiting potentially malicious sites. “The Standard protection mode for Chrome on desktop and iOS will check sites against Google’s server-side list of known bad sites in real-time,” Google’s…
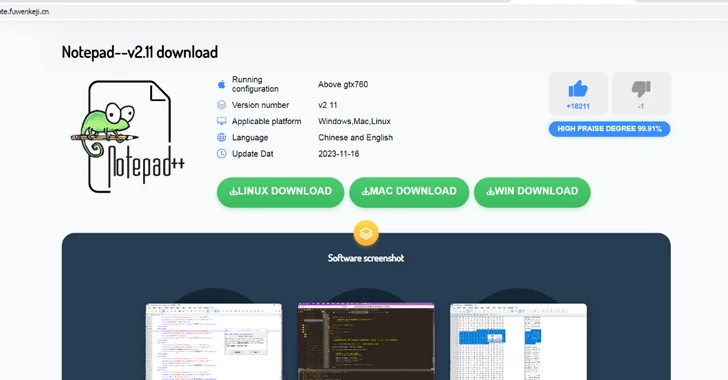
Read MoreMar 15, 2024NewsroomMalvertising / Threat Intelligence Chinese users looking for legitimate software such as Notepad++ and VNote on search engines like Baidu are being targeted with malicious ads and bogus links to distribute trojanized versions of the software and ultimately deploy Geacon, a Golang-based implementation of Cobalt Strike. “The malicious site found in the notepad++…
Read MoreSecurity analysts receive thousands of alerts daily, and the onslaught is rapidly growing without any signs of slowing down. Meanwhile, cybersecurity talent is extremely difficult to recruit and retain. According to the ISC2 Cybersecurity Workforce Study 2023, the global cybersecurity workforce of about 5.5 million would need to almost double to meet the current need.…
Read MorePersistent threats such as business email compromise (BEC) necessitate an evolution of cybersecurity defenses to protect identities. Transitioning away from a reliance on authenticator apps and IP fencing toward a comprehensive zero-trust framework, incorporating FIDO2 security keys or passkeys, offers a path to more secure and user-friendly authentication experiences. By embracing these technologies, organizations can…
Read MoreHow To Here are a few tips for secure file transfers and what else to consider when sharing sensitive documents so that your data remains safe 13 Mar 2024 • , 4 min. read Our lives are increasingly lived in the digital world. And while this comes with a host of benefits, it also exposes…
Read MoreCEO of Data Privacy Company Onerep.com Founded Dozens of People-Search Firms – Krebs on Security
by nlqip
The data privacy company Onerep.com bills itself as a Virginia-based service for helping people remove their personal information from almost 200 people-search websites. However, an investigation into the history of onerep.com finds this company is operating out of Belarus and Cyprus, and that its founder has launched dozens of people-search services over the years. Onerep’s…
Read MoreCisco released security updates to address vulnerabilities in Cisco IOS XR software. A cyber threat actor could exploit one of these vulnerabilities to take control of an affected device. CISA encourages users and administrators to review the following advisories and apply the necessary updates: Cisco IOS XR Software for ASR 9000 Series Aggregation Services Routers…
Read MoreRecent Posts
- Tenable Announces the Passing of Chairman and CEO Amit Yoran
- Opinion: Why Nvidia, MediaTek May Enter The PC CPU Market Soon
- Microsoft VP Of Silicon Engineering Jumps To Google Cloud To Head Chip Technology And Manufacturing
- 10 Cloud Startup Companies To Watch In 2025
- Cybersecurity Snapshot: After Telecom Hacks, CISA Offers Security Tips for Cell Phone Users, While Banks Seek Clearer AI Regulations