Feds Seize LockBit Ransomware Websites, Offer Decryption Tools, Troll Affiliates – Krebs on Security
by nlqip
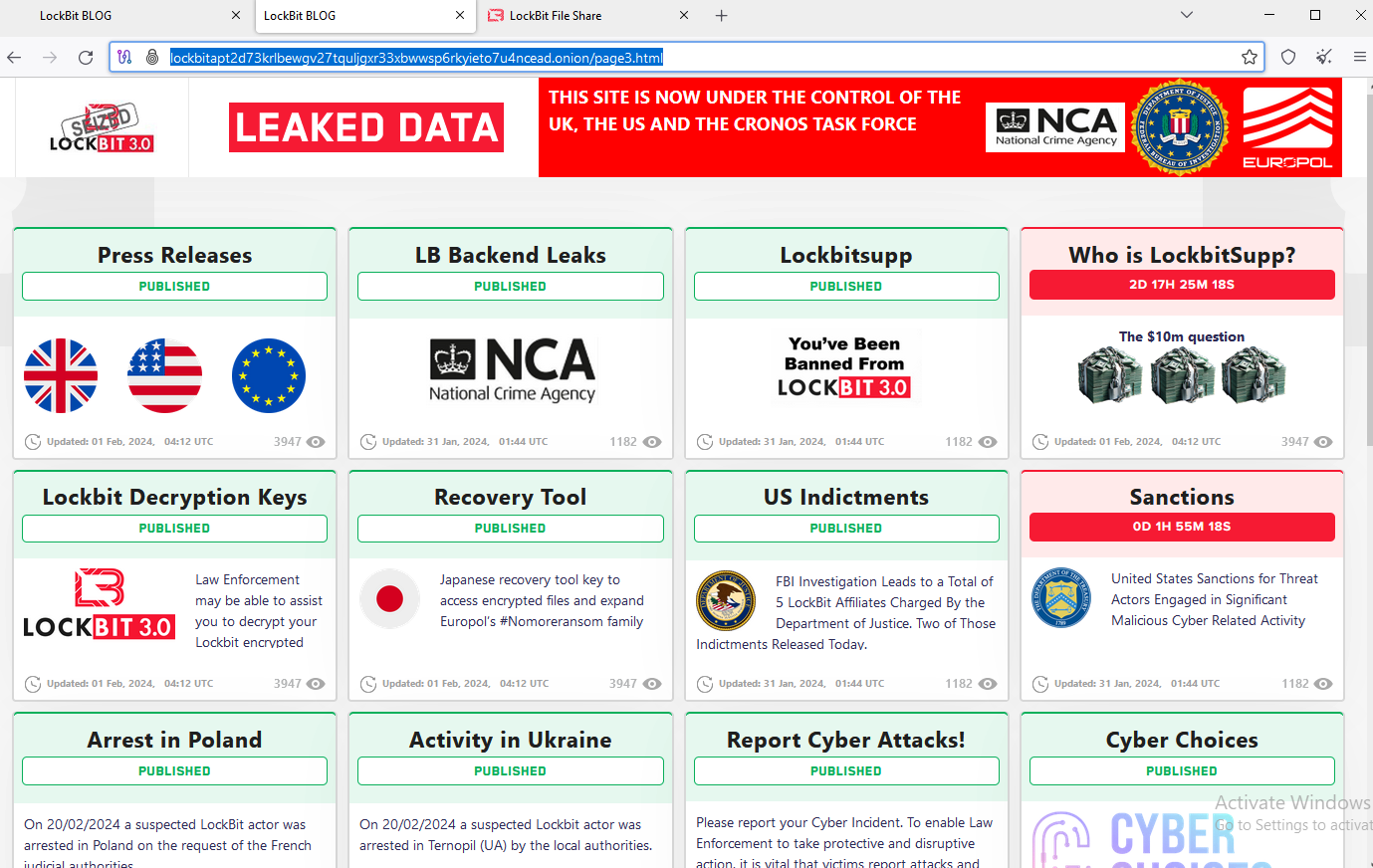
U.S. and U.K. authorities have seized the darknet websites run by LockBit, a prolific and destructive ransomware group that has claimed more than 2,000 victims worldwide and extorted over $120 million in payments. Instead of listing data stolen from ransomware victims who didn’t pay, LockBit’s victim shaming website now offers free recovery tools, as well…
Read MoreCISA released three Industrial Control Systems (ICS) advisories on February 20, 2024. These advisories provide timely information about current security issues, vulnerabilities, and exploits surrounding ICS. CISA encourages users and administrators to review the newly released ICS advisories for technical details and mitigations. Source link ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde…
Read MoreAdvisory ID: VMSA-2024-0003 CVSSv3 Range: 9.6 – 7.8 Issue Date: 2024-02-20 Updated On: 2024-02-20 (Initial Advisory) CVE(s): CVE-2024-22245, CVE-2024-22250 Synopsis: Addressing Arbitrary Authentication Relay and Session Hijack Vulnerabilities in Deprecated VMware Enhanced Authentication Plug-in (EAP) (CVE-2024-22245, CVE-2024-22250) Source link ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde…
Read MoreFeb 20, 2024NewsroomServer Security / Cryptojacking A novel malware campaign has been observed targeting Redis servers for initial access with the ultimate goal of mining cryptocurrency on compromised Linux hosts. “This particular campaign involves the use of a number of novel system weakening techniques against the data store itself,” Cado security researcher Matt Muir said…
Read MoreAnyone that utilizes technology in their daily lives understands that it is ever-changing, and the sentiment is especially true within the cybersecurity industry. Adversaries continue to evolve with new tactics to bypass defenses, so it is necessary that the methods of detecting and preventing these threats do so at an even more rapid pace. However,…
Read MoreIf the attackers gain access to a server using some other method — for example SSH — and that server runs a Redis instance in Protected Mode, they can connect to it locally to disable the protection and then be able to send other commands over the internet. Another command disables the replica-read-only configuration option.…
Read MoreBrett Johnson has been called the Godfather of cyber crime. He was on the FBI’s most-wanted list. And he was on What the Hack before! He returns for a freewheeling conversation about what’s new in cybercrime, how it’s changed and wants you to know how to better protect your digital life. This week’s episode is…
Read MoreFeb 20, 2024NewsroomMalware / Supply Chain Security Cybersecurity researchers have discovered two malicious packages on the Python Package Index (PyPI) repository that were found leveraging a technique called DLL side-loading to circumvent detection by security software and run malicious code. The packages, named NP6HelperHttptest and NP6HelperHttper, were each downloaded 537 and 166 times, respectively, before…
Read MoreFeb 20, 2024NewsroomRansomware / Data Protection The U.K. National Crime Agency (NCA) on Tuesday confirmed that it obtained LockBit’s source code as well as intelligence pertaining to its activities and their affiliates as part of a dedicated task force called Operation Cronos. “Some of the data on LockBit’s systems belonged to victims who had paid…
Read MoreA robust IR plan ensures that an organization is prepared to respond swiftly and efficiently to potential threats. Coordinating IR planning with your Managed Detection and Response (MDR) partner is an essential component. Successful defense requires collaboration and the agility to respond to threats to minimize damage. What Is Incident Response (IR)? Incident Response (IR)…
Read MoreRecent Posts
- Arm To Seek Retrial In Qualcomm Case After Mixed Verdict
- Jury Sides With Qualcomm Over Arm In Case Related To Snapdragon X PC Chips
- Equinix Makes Dell AI Factory With Nvidia Available Through Partners
- AMD’s EPYC CPU Boss Seeks To Push Into SMB, Midmarket With Partners
- Fortinet Releases Security Updates for FortiManager | CISA