Oct 26, 2024Ravie LakshmananCybercrime / Malware Four members of the now-defunct REvil ransomware operation have been sentenced to several years in prison in Russia, marking one of the rare instances where cybercriminals from the country have been convicted of hacking and money laundering charges. Russian news publication Kommersant reported that a court in St. Petersburg…
Read MoreOct 26, 2024Ravie LakshmananCloud Security / Cryptocurrency The infamous cryptojacking group known as TeamTNT appears to be readying for a new large-scale campaign targeting cloud-native environments for mining cryptocurrencies and renting out breached servers to third-parties. “The group is currently targeting exposed Docker daemons to deploy Sliver malware, a cyber worm, and cryptominers, using compromised…
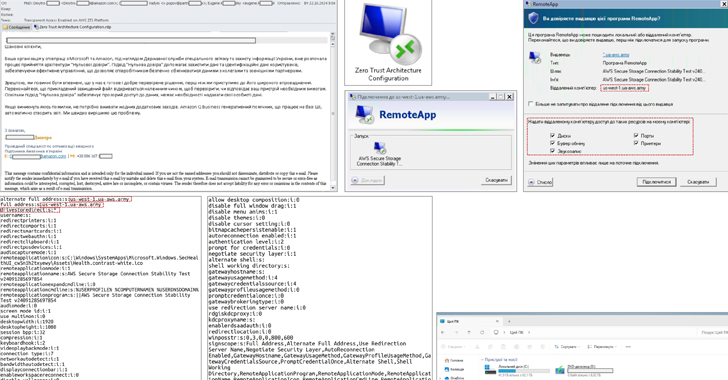
Read MoreOct 26, 2024Ravie LakshmananCyber Attack / Threat Intelligence The Computer Emergency Response Team of Ukraine (CERT-UA) has detailed a new malicious email campaign targeting government agencies, enterprises, and military entities. “The messages exploit the appeal of integrating popular services like Amazon or Microsoft and implementing a zero-trust architecture,” CERT-UA said. “These emails contain attachments in…
Read MoreThe BlackBasta ransomware operation has moved its social engineering attacks to Microsoft Teams, posing as corporate help desks contacting employees to assist them with an ongoing spam attack. Black Basta is a ransomware operation active since April 2022 and responsible for hundreds of attacks against corporations worldwide. After the Conti cybercrime syndicate shut down in…
Read MoreRussia has sentenced four members of the REvil ransomware operation to over 4 years in prison for distributing malware and illegal circulation of means of payment. REvil ransomware (aka Sodin and Sodinokibi) was launched in April 2019 as a direct successor of the GandCrab operation. In less than a year, the gang became the most prolific ransomware group, asking…
Read MoreAmazon has seized domains used by the Russian APT29 hacking group in targeted attacks against government and military organizations to steal Windows credentials and data using malicious Remote Desktop Protocol connection files. APT29, also known as “Cozy Bear” and “Midnight Blizzard,” is a Russian state-sponsored cyber-espionage group linked to Russia’s Foreign Intelligence Service (SVR). Amazon clarifies that…
Read MoreTuan Tran is stepping down from his role as president of HP’s printing and imaging business to lead the PC and print giant’s cross-company AI strategy as the leader of a new organization. Taking over the printing business is 30-year HP veteran Anneliese Olson. HP Inc. has tapped the leader of its printing and imaging…
Read MoreGad Rosenthal Gad Rosenthal is a senior product manager at Tenable, where he leads the development of data security posture management (DSPM) capabilities. He joined Tenable after it acquired Eureka, a cloud data security company. Gad has also held cybersecurity roles at Microsoft, Siemplify (now part of Google), and Imperva, and has led cybersecurity and…
Read MoreCVE-2024-47575: Frequently Asked Questions About FortiJump Zero-Day in FortiManager and FortiManager Cloud
by nlqip
Frequently asked questions about a zero-day vulnerability in Fortinet’s FortiManager that has reportedly been exploited in the wild. Background The Tenable Security Response Team (SRT) has compiled this blog to answer Frequently Asked Questions (FAQ) regarding a zero-day vulnerability in Fortinet’s FortiManager. Update October 23: The blog has been updated with new information about in-the-wild…
Read MoreCybersecurity Snapshot: New Guides Offer Best Practices for Preventing Shadow AI and for Deploying Secure Software Updates
by nlqip
Looking for help with shadow AI? Want to boost your software updates’ safety? New publications offer valuable tips. Plus, learn why GenAI and data security have become top drivers of cyber strategies. And get the latest on the top “no-nos” for software security; the EU’s new cyber law; and CISOs’ communications with boards. Dive into…
Read MoreRecent Posts
- Five HPE GreenLake Game Changers: A Look At Pay-Per-Use Cloud Service Improvements
- Multiple Vulnerabilities in Adobe Products Could Allow for Arbitrary Code Execution
- Critical Patches Issued for Microsoft Products, January 14, 2025
- CISA Releases Four Industrial Control Systems Advisories | CISA
- Ivanti Releases Security Updates for Multiple Products | CISA