Tag: blueapps
The content of this post is solely the responsibility of the author. LevelBlue does not adopt or endorse any of the views, positions, or information provided by the author in this article. As we gear up to celebrate Internet Day on October 29th, let’s take a moment to appreciate how much the Internet has revolutionized…
Read MoreWhen you think of a cyberattack, you probably envision a sophisticated hacker behind a Matrix-esque screen actively penetrating networks with their technical prowess. However, the reality of many attacks is far more mundane. A simple email with an innocent subject line such as “Missed delivery attempt” sits in an employee’s spam folder. They open it…
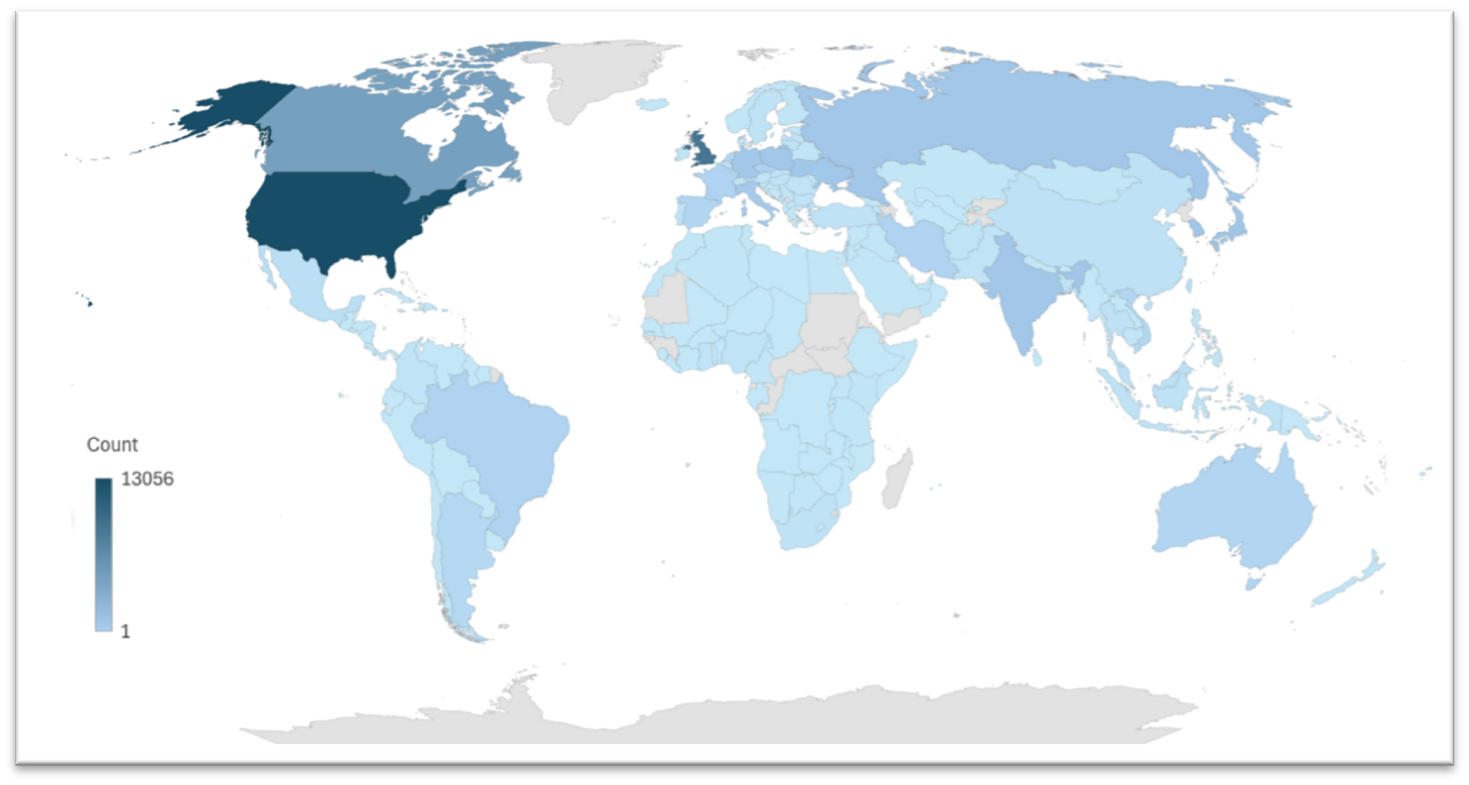
Read MoreExecutive Summary Seven years after its first appearance, the proxy server botnet Ngioweb continues its impactful presence on the internet with barely any relevant changes in its original code. Threat actors have continued to actively use Nbioweb extensively to scan for vulnerable devices (including a new arsenal of exploits) which can be turned into new…
Read MoreThe content of this post is solely the responsibility of the author. LevelBlue does not adopt or endorse any of the views, positions, or information provided by the author in this article. Over the last decade, web applications have become integral to everyday life. This includes business and personal activities, facilitating everything from banking and…
Read MoreThe content of this post is solely the responsibility of the author. LevelBlue does not adopt or endorse any of the views, positions, or information provided by the author in this article. Summer is a time for relaxation, travel, and spending quality moments with family and friends. However, it is also peak season for cybercriminals…
Read MoreThe content of this post is solely the responsibility of the author. LevelBlue does not adopt or endorse any of the views, positions, or information provided by the author in this article. Maintaining an active social media presence can be a great way to improve brand visibility and generate leads, but it also opens the…
Read MoreThe content of this post is solely the responsibility of the author. LevelBlue does not adopt or endorse any of the views, positions, or information provided by the author in this article. From humble beginnings as a niche hobby relegated to small gaming cafes and basements, eSports has grown into a huge affair where gamers…
Read MoreWhat is Operational Technology? Operational Technology (OT) is the backbone of our modern world as we know it today. Think about the daily operations of a factory, the precise control of our power grids, and even the supply of clean water to our homes. All of these modern capabilities are made possible and efficient due…
Read MoreThe content of this post is solely the responsibility of the author. LevelBlue does not adopt or endorse any of the views, positions, or information provided by the author in this article. Firewall technology has mirrored the complexities in network security, evolving significantly over time. Originally serving as basic traffic regulators based on IP addresses,…
Read MorePenetration testing is a cornerstone of any mature security program and is a mature and well understood practice supported by robust methodologies, tools, and frameworks. The tactical goals of these engagements typically revolve around identification and exploitation of vulnerabilities in technology, processes, and people to gain initial, elevated, and administrative access to the target environment.…
Read MoreRecent Posts
- Bob Sullivan Discovers a Scam That Strikes Twice
- A Vulnerability in Apache Struts2 Could Allow for Remote Code Execution
- CISA Adds One Known Exploited Vulnerability to Catalog | CISA
- Xerox To Buy Lexmark For $1.5B In Blockbuster Print Deal
- Vulnerability Summary for the Week of December 16, 2024 | CISA