Tag: computer security
Apr 01, 2024NewsroomCryptocurrency / Financial Fraud The Indian government said it has rescued and repatriated about 250 citizens in Cambodia who were held captive and coerced into running cyber scams. The Indian nationals “were lured with employment opportunities to that country but were forced to undertake illegal cyber work,” the Ministry of External Affairs (MEA)…
Read MoreDespite a plethora of available security solutions, more and more organizations fall victim to Ransomware and other threats. These continued threats aren’t just an inconvenience that hurt businesses and end users – they damage the economy, endanger lives, destroy businesses and put national security at risk. But if that wasn’t enough – North Korea appears…
Read MoreApr 01, 2024NewsroomBotnet / Mobile Security Several malicious Android apps that turn mobile devices running the operating system into residential proxies (RESIPs) for other threat actors have been observed on the Google Play Store. The findings come from HUMAN’s Satori Threat Intelligence team, which said the cluster of VPN apps came fitted with a Golang…
Read MoreThe Android banking trojan known as Vultur has resurfaced with a suite of new features and improved anti-analysis and detection evasion techniques, enabling its operators to remotely interact with a mobile device and harvest sensitive data. “Vultur has also started masquerading more of its malicious activity by encrypting its C2 communication, using multiple encrypted payloads…
Read MoreMar 30, 2024NewsroomMalware / Cryptocurrency Malicious ads and bogus websites are acting as a conduit to deliver two different stealer malware, including Atomic Stealer, targeting Apple macOS users. The ongoing infostealer attacks targeting macOS users may have adopted different methods to compromise victims’ Macs, but operate with the end goal of stealing sensitive data, Jamf…
Read MoreMar 30, 2024NewsroomLinux / Supply Chain Attack RedHat on Friday released an “urgent security alert” warning that two versions of a popular data compression library called XZ Utils (previously LZMA Utils) have been backdoored with malicious code designed to allow unauthorized remote access. The software supply chain compromise, tracked as CVE-2024-3094, has a CVSS score…
Read MoreMar 29, 2024NewsroomReverse Engineering / RFID Security Security vulnerabilities discovered in Dormakaba’s Saflok electronic RFID locks used in hotels could be weaponized by threat actors to forge keycards and stealthily slip into locked rooms. The shortcomings have been collectively named Unsaflok by researchers Lennert Wouters, Ian Carroll, rqu, BusesCanFly, Sam Curry, sshell, and Will Caruana.…
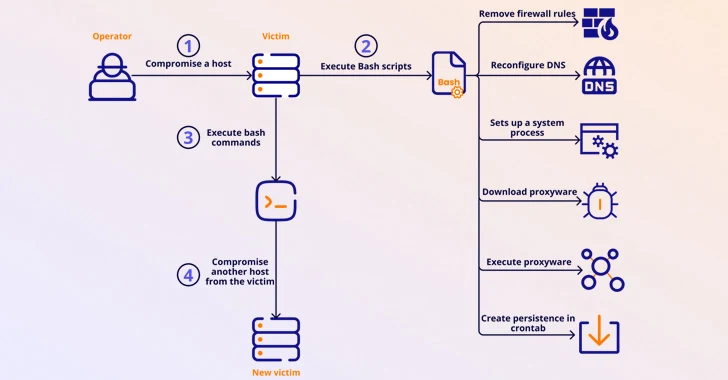
Read MoreMar 29, 2024NewsroomNetwork Security / IoT Security A botnet previously considered to be rendered inert has been observed enslaving end-of-life (EoL) small home/small office (SOHO) routers and IoT devices to fuel a criminal proxy service called Faceless. “TheMoon, which emerged in 2014, has been operating quietly while growing to over 40,000 bots from 88 countries…
Read MoreMar 29, 2024The Hacker NewsPen Testing / Regulatory Compliance Network penetration testing plays a vital role in detecting vulnerabilities that can be exploited. The current method of performing pen testing is pricey, leading many companies to undertake it only when necessary, usually once a year for their compliance requirements. This manual approach often misses opportunities…
Read MoreMar 29, 2024NewsroomVulnerability / Linux Details have emerged about a vulnerability impacting the “wall” command of the util-linux package that could be potentially exploited by a bad actor to leak a user’s password or alter the clipboard on certain Linux distributions. The bug, tracked as CVE-2024-28085, has been codenamed WallEscape by security researcher Skyler Ferrante.…
Read MoreRecent Posts
- Seven Trends to Watch for in 2025
- Multiple Vulnerabilities in Ivanti Products Could Allow for Remote Code Execution
- Ivanti Releases Security Updates for Connect Secure, Policy Secure, and ZTA Gateways | CISA
- CISA Adds One Vulnerability to the KEV Catalog | CISA
- CVE-2025-0282: Ivanti Connect Secure Zero-Day Vulnerability Exploited In The Wild