Tag: computer security
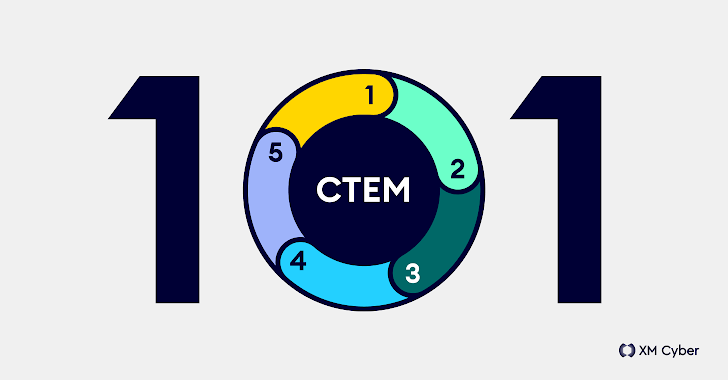
Mar 12, 2024The Hacker NewsCTEM / Vulnerability Management In a world of ever-expanding jargon, adding another FLA (Four-Letter Acronym) to your glossary might seem like the last thing you’d want to do. But if you are looking for ways to continuously reduce risk across your environment while making significant and consistent improvements to security posture,…
Read MoreMar 12, 2024NewsroomWordPress / Website Security A new malware campaign is leveraging a high-severity security flaw in the Popup Builder plugin for WordPress to inject malicious JavaScript code. According to Sucuri, the campaign has infected more than 3,900 sites over the past three weeks. “These attacks are orchestrated from domains less than a month old,…
Read MoreMar 12, 2024NewsroomCyber Espionage / Threat Russia has detained a South Korean national for the first time on cyber espionage charges and transferred from Vladivostok to Moscow for further investigation. The development was first reported by Russian news agency TASS. “During the investigation of an espionage case, a South Korean citizen Baek Won-soon was identified…
Read MoreEmbracing the Cloud: Revolutionizing Privileged Access Management with One Identity PAM Essentials
by nlqip
Mar 11, 2024The Hacker NewsPrivileged Access Management As cyber threats loom around every corner and privileged accounts become prime targets, the significance of implementing a robust Privileged Access Management (PAM) solution can’t be overstated. With organizations increasingly migrating to cloud environments, the PAM Solution Market is experiencing a transformative shift toward cloud-based offerings. One Identity…
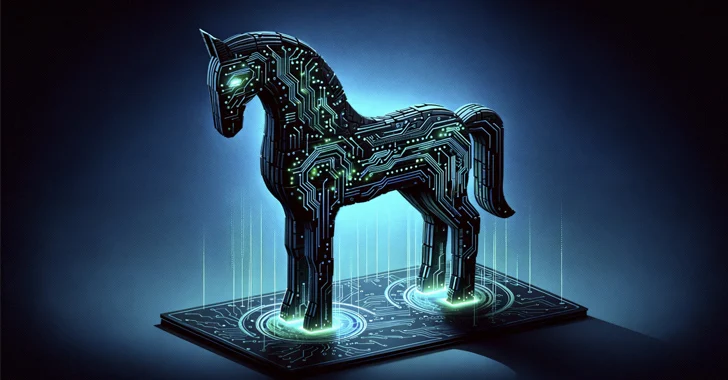
Read MoreUsers in Brazil are the target of a new banking trojan known as CHAVECLOAK that’s propagated via phishing emails bearing PDF attachments. “This intricate attack involves the PDF downloading a ZIP file and subsequently utilizing DLL side-loading techniques to execute the final malware,” Fortinet FortiGuard Labs researcher Cara Lin said. The attack chain involves the…
Read MoreMar 11, 2024The Hacker NewsCybersecurity / Browser Security As the shift of IT infrastructure to cloud-based solutions celebrates its 10-year anniversary, it becomes clear that traditional on-premises approaches to data security are becoming obsolete. Rather than protecting the endpoint, DLP solutions need to refocus their efforts to where corporate data resides – in the browser.…
Read MoreMar 11, 2024NewsroomRansomware / Vulnerability The threat actors behind the BianLian ransomware have been observed exploiting security flaws in JetBrains TeamCity software to conduct their extortion-only attacks. According to a new report from GuidePoint Security, which responded to a recent intrusion, the incident “began with the exploitation of a TeamCity server which resulted in the…
Read MoreMar 11, 2024NewsroomZero-Day / Endpoint Security A financially motivated threat actor called Magnet Goblin is swiftly adopting one-day security vulnerabilities into its arsenal in order to opportunistically breach edge devices and public-facing services and deploy malware on compromised hosts. “Threat actor group Magnet Goblin’s hallmark is its ability to swiftly leverage newly disclosed vulnerabilities, particularly…
Read MoreMar 11, 2024NewsroomNetwork Security / Vulnerability Technical specifics and a proof-of-concept (PoC) exploit have been made available for a recently disclosed critical security flaw in Progress Software OpenEdge Authentication Gateway and AdminServer, which could be potentially exploited to bypass authentication protections. Tracked as CVE-2024-1403, the vulnerability has a maximum severity rating of 10.0 on the…
Read MoreMar 09, 2024NewsroomCyber Attack / Threat Intelligence Microsoft on Friday revealed that the Kremlin-backed threat actor known as Midnight Blizzard (aka APT29 or Cozy Bear) managed to gain access to some of its source code repositories and internal systems following a hack that came to light in January 2024. “In recent weeks, we have seen…
Read MoreRecent Posts
- The Most Scary, Interesting, and Important Stories of 2024
- Choosing the Right CNAPP: Six Considerations for Mid-Sized Enterprises
- CISA Adds One Known Exploited Vulnerability to Catalog | CISA
- Vulnerability Summary for the Week of December 23, 2024 | CISA
- Navigating the SEC’s Cybersecurity Disclosure Rules: One Year On