Tag: computer security
Jul 25, 2024NewsroomMalware / Cyber Espionage A North Korea-linked threat actor known for its cyber espionage operations has gradually expanded into financially-motivated attacks that involve the deployment of ransomware, setting it apart from other nation-state hacking groups linked to the country. Google-owned Mandiant is tracking the activity cluster under a new moniker APT45, which overlaps…
Read MoreJul 25, 2024NewsroomCybercrime / Online Safety Meta Platforms on Wednesday said it took steps to remove around 63,000 Instagram accounts in Nigeria that were found to target people with financial sextortion scams. “These included a smaller coordinated network of around 2,500 accounts that we were able to link to a group of around 20 individuals,”…
Read MoreWhile the specifics for security testing vary for applications, web applications, and APIs, a holistic and proactive applications security strategy is essential for all three types. There are six core types of testing that every security professional should know about to secure their applications, regardless of what phase they are in in development or deployment.…
Read MoreJul 25, 2024NewsroomDNS Security /Vulnerability The Internet Systems Consortium (ISC) has released patches to address multiple security vulnerabilities in the Berkeley Internet Name Domain (BIND) 9 Domain Name System (DNS) software suite that could be exploited to trigger a denial-of-service (DoS) condition. “A cyber threat actor could exploit one of these vulnerabilities to cause a…
Read MoreJul 25, 2024NewsroomCloud Security / Vulnerability Cybersecurity researchers have disclosed a privilege escalation vulnerability impacting Google Cloud Platform’s Cloud Functions service that an attacker could exploit to access other services and sensitive data in an unauthorized manner. Tenable has given the vulnerability the name ConfusedFunction. “An attacker could escalate their privileges to the Default Cloud…
Read MoreWebinar: Securing the Modern Workspace: What Enterprises MUST Know about Enterprise Browser Security
by nlqip
Jul 25, 2024The Hacker NewsBrowser Security / Enterprise Security The browser is the nerve center of the modern workspace. Ironically, however, the browser is also one of the least protected threat surfaces of the modern enterprise. Traditional security tools provide little protection against browser-based threats, leaving organizations exposed. Modern cybersecurity requires a new approach based…
Read MoreA zero-day security flaw in Telegram’s mobile app for Android called EvilVideo made it possible for attackers to malicious files disguised as harmless-looking videos. The exploit appeared for sale for an unknown price in an underground forum on June 6, 2024, ESET said. Following responsible disclosure on June 26, the issue was addressed by Telegram…
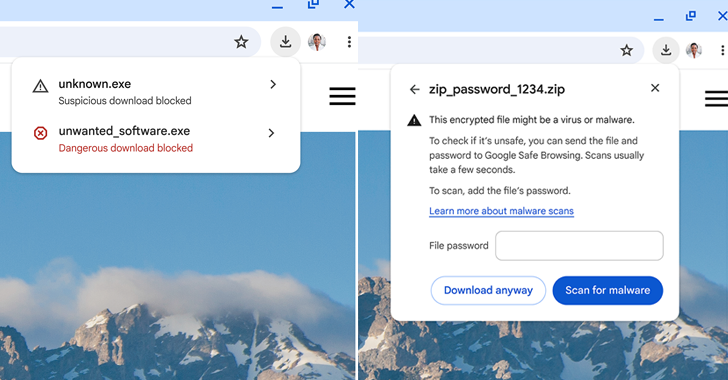
Read MoreJul 25, 2024NewsroomBrowser Security / Data Protection Google said it’s adding new security warnings when downloading potentially suspicious and malicious files via its Chrome web browser. “We have replaced our previous warning messages with more detailed ones that convey more nuance about the nature of the danger and can help users make more informed decisions,”…
Read MoreJul 25, 2024NewsroomContainer Security / Vulnerability Docker is warning of a critical flaw impacting certain versions of Docker Engine that could allow an attacker to sidestep authorization plugins (AuthZ) under specific circumstances. Tracked as CVE-2024-41110, the bypass and privilege escalation vulnerability carries a CVSS score of 10.0, indicating maximum severity. “An attacker could exploit a…
Read MoreSecurity questionnaires aren’t just an inconvenience — they’re a recurring problem for security and sales teams. They bleed time from organizations, filling the schedules of professionals with monotonous, automatable work. But what if there were a way to reduce or even altogether eliminate security questionnaires? The root problem isn’t a lack of great questionnaire products…
Read MoreRecent Posts
- CISA Releases the Cybersecurity Performance Goals Adoption Report | CISA
- Multiple vulnerabilities in SonicWall SonicOS could allow a remote attacker to bypass authentication.
- Dell Sales Leader, Former Channel Chief John Byrne Steps Down
- The Dangers of DNS Hijacking
- CES 2025: 15 PC Chips Announced By Intel, Nvidia, AMD And Qualcomm