Tag: computer security
Jun 06, 2024NewsroomBotnet / DDoS Attack The distributed denial-of-service (DDoS) botnet known as Muhstik has been observed leveraging a now-patched security flaw impacting Apache RocketMQ to co-opt susceptible servers and expand its scale. “Muhstik is a well-known threat targeting IoT devices and Linux-based servers, notorious for its ability to infect devices and utilize them for…
Read MoreLearn about critical threats that can impact your organization and the bad actors behind them from Cybersixgill’s threat experts. Each story shines a light on underground activities, the threat actors involved, and why you should care, along with what you can do to mitigate risk. In an increasingly interconnected world, supply chain attacks have emerged…
Read MoreJun 06, 2024NewsroomEndpoint Security / Malware Threat actors are increasingly abusing legitimate and commercially available packer software such as BoxedApp to evade detection and distribute malware such as remote access trojans and information stealers. “The majority of the attributed malicious samples targeted financial institutions and government industries,” Check Point security researcher Jiri Vinopal said in…
Read MoreJun 06, 2024The Hacker NewsPassword Security / Dark Web Tom works for a reputable financial institution. He has a long, complex password that would be near-impossible to guess. He’s memorized it by heart, so he started using it for his social media accounts and on his personal devices too. Unbeknownst to Tom, one of these…
Read MoreJun 06, 2024NewsroomData Encryption / Privacy Google has announced plans to store Maps Timeline data locally on users’ devices instead of their Google account effective December 1, 2024. The changes were originally announced by the tech giant in December 2023, alongside changes to the auto-delete control when enabling Location History by setting it to three…
Read MoreJun 06, 2024NewsroomSoftware Security / Data Theft Cybersecurity researchers have discovered a malicious Python package uploaded to the Python Package Index (PyPI) repository that’s designed to deliver an information stealer called Lumma (aka LummaC2). The package in question is crytic-compilers, a typosquatted version of a legitimate library named crytic-compile. The rogue package was downloaded 441…
Read MoreEarly in 2024, Wing Security released its State of SaaS Security report, offering surprising insights into emerging threats and best practices in the SaaS domain. Now, halfway through the year, several SaaS threat predictions from the report have already proven accurate. Fortunately, SaaS Security Posture Management (SSPM) solutions have prioritized mitigation capabilities to address many…
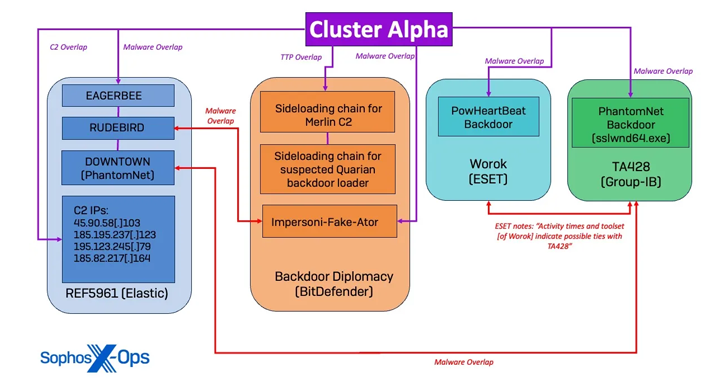
Read MoreJun 05, 2024NewsroomCyber Espionage / Threat Intelligence An unnamed high-profile government organization in Southeast Asia emerged as the target of a “complex, long-running” Chinese state-sponsored cyber espionage operation codenamed Crimson Palace. “The overall goal behind the campaign was to maintain access to the target network for cyberespionage in support of Chinese state interests,” Sophos researchers…
Read MoreAn analysis of a nascent ransomware strain called RansomHub has revealed it to be an updated and rebranded version of Knight ransomware, itself an evolution of another ransomware known as Cyclops. Knight (aka Cyclops 2.0) ransomware first arrived in May 2023, employing double extortion tactics to steal and encrypt victims’ data for financial gain. It’s…
Read MoreJun 05, 2024NewsroomVulnerability / Data Security Zyxel has released security updates to address critical flaws impacting two of its network-attached storage (NAS) devices that have currently reached end-of-life (EoL) status. Successful exploitation of three of the five vulnerabilities could permit an unauthenticated attacker to execute operating system (OS) commands and arbitrary code on affected installations.…
Read MoreRecent Posts
- CISA Releases the Cybersecurity Performance Goals Adoption Report | CISA
- Multiple vulnerabilities in SonicWall SonicOS could allow a remote attacker to bypass authentication.
- Dell Sales Leader, Former Channel Chief John Byrne Steps Down
- The Dangers of DNS Hijacking
- CES 2025: 15 PC Chips Announced By Intel, Nvidia, AMD And Qualcomm