Tag: cyber attacks
Oct 02, 2024Ravie LakshmananVulnerability / Network Security A little over a dozen new security vulnerabilities have been discovered in residential and enterprise routers manufactured by DrayTek that could be exploited to take over susceptible devices. “These vulnerabilities could enable attackers to take control of a router by injecting malicious code, allowing them to persist on…
Read MoreOct 02, 2024Ravie LakshmananVulnerability / Data Breach Cybersecurity researchers have disclosed that 5% of all Adobe Commerce and Magento stores have been hacked by malicious actors by exploiting a security vulnerability dubbed CosmicSting. Tracked as CVE-2024-34102 (CVSS score: 9.8), the critical flaw relates to an improper restriction of XML external entity reference (XXE) vulnerability that…
Read MoreDynamic malware analysis is a key part of any threat investigation. It involves executing a sample of a malicious program in the isolated environment of a malware sandbox to monitor its behavior and gather actionable indicators. Effective analysis must be fast, in-depth, and precise. These five tools will help you achieve it with ease. 1.…
Read MoreOct 02, 2024Ravie LakshmananCyber Threat / Malware Three different organizations in the U.S. were targeted in August 2024 by a North Korean state-sponsored threat actor called Andariel as part of a likely financially motivated attack. “While the attackers didn’t succeed in deploying ransomware on the networks of any of the organizations affected, it is likely…
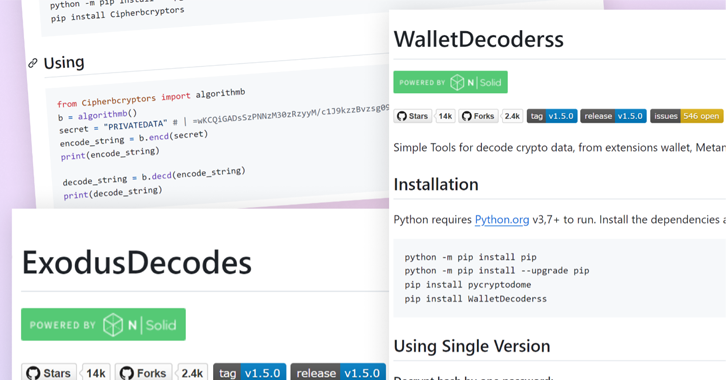
Read MoreOct 02, 2024The Hacker NewsSupply Chain Attack / Cryptocurrency A new set of malicious packages has been unearthed in the Python Package Index (PyPI) repository that masqueraded as cryptocurrency wallet recovery and management services, only to siphon sensitive data and facilitate the theft of valuable digital assets. “The attack targeted users of Atomic, Trust Wallet,…
Read MoreOct 02, 2024The Hacker NewsEmail Security / Vulnerability Cybersecurity researchers are warning about active exploitation attempts targeting a newly disclosed security flaw in Synacor’s Zimbra Collaboration. Enterprise security firm Proofpoint said it began observing the activity starting September 28, 2024. The attacks seek to exploit CVE-2024-45519, a severe security flaw in its postjournal service that…
Read MoreThe threat actors behind the Rhadamanthys information stealer have added new advanced features to the malware, including using artificial intelligence (AI) for optical character recognition (OCR) as part of what’s called “Seed Phrase Image Recognition.” “This allows Rhadamanthys to extract cryptocurrency wallet seed phrases from images, making it a highly potent threat for anyone dealing…
Read MoreOct 01, 2024The Hacker NewsGenerative AI / Data Protection Since its emergence, Generative AI has revolutionized enterprise productivity. GenAI tools enable faster and more effective software development, financial analysis, business planning, and customer engagement. However, this business agility comes with significant risks, particularly the potential for sensitive data leakage. As organizations attempt to balance productivity…
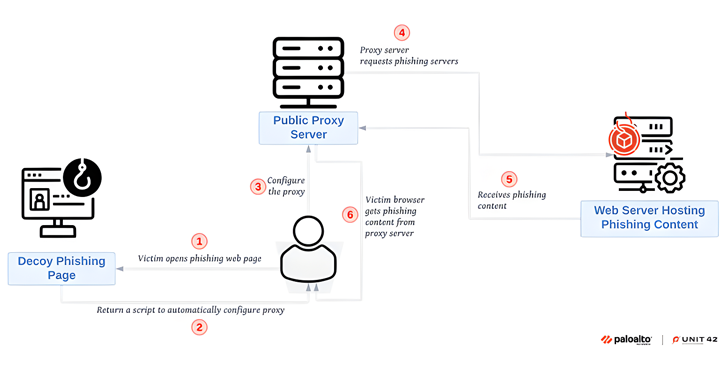
Read MoreMore than 140,000 phishing websites have been found linked to a phishing-as-a-service (PhaaS) platform named Sniper Dz over the past year, indicating that it’s being used by a large number of cybercriminals to conduct credential theft. “For prospective phishers, Sniper Dz offers an online admin panel with a catalog of phishing pages,” Palo Alto Networks…
Read MoreCybersecurity researchers have uncovered a new cryptojacking campaign targeting the Docker Engine API with the goal of co-opting the instances to join a malicious Docker Swarm controlled by the threat actor. This enabled the attackers to “use Docker Swarm’s orchestration features for command-and-control (C2) purposes,” Datadog researchers Matt Muir and Andy Giron said in an…
Read More