Tag: cyber attacks
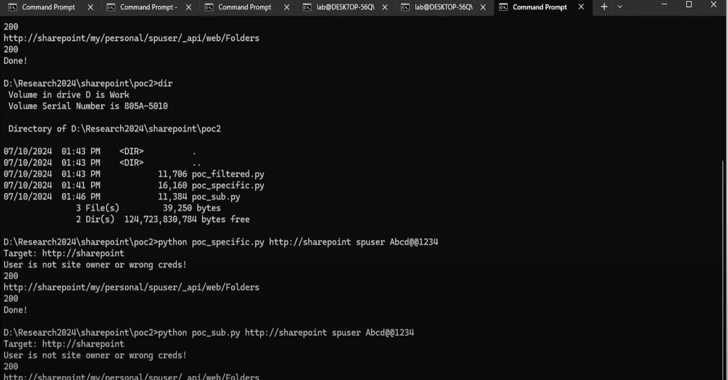
Oct 23, 2024Ravie LakshmananVulnerability / Threat Intelligence A high-severity flaw impacting Microsoft SharePoint has been added to the Known Exploited Vulnerabilities (KEV) catalog by the U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Tuesday, citing evidence of active exploitation. The vulnerability, tracked as CVE-2024-38094 (CVSS score: 7.2), has been described as a deserialization vulnerability impacting…
Read MoreOct 23, 2024The Hacker NewsIdentity Security / Data Protection Identity security is front, and center given all the recent breaches that include Microsoft, Okta, Cloudflare and Snowflake to name a few. Organizations are starting to realize that a shake-up is needed in terms of the way we approach identity security both from a strategic but…
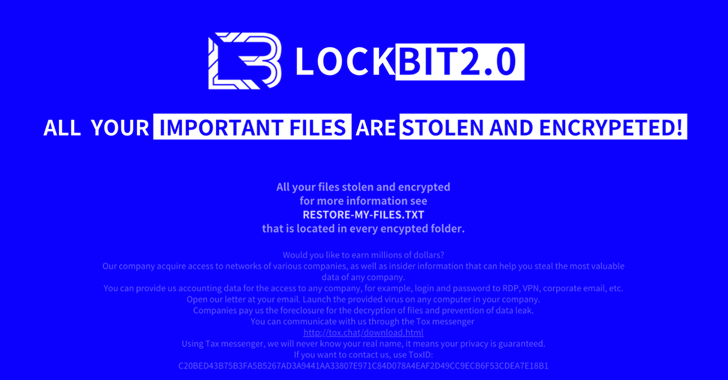
Read MoreThreat actors have been observed abusing Amazon S3 (Simple Storage Service) Transfer Acceleration feature as part of ransomware attacks designed to exfiltrate victim data and upload them to S3 buckets under their control. “Attempts were made to disguise the Golang ransomware as the notorious LockBit ransomware,” Trend Micro researchers Jaromir Horejsi and Nitesh Surana said.…
Read MoreIt may come as a surprise to learn that 34% of security practitioners are in the dark about how many SaaS applications are deployed in their organizations. And it’s no wonder—the recent AppOmni 2024 State of SaaS Security Report reveals that only 15% of organizations centralize SaaS security within their cybersecurity teams. These statistics not…
Read MoreOct 23, 2024Ravie LakshmananArtificial Intelligence / Vulnerability Cybersecurity researchers have shed light on a new adversarial technique that could be used to jailbreak large language models (LLMs) during the course of an interactive conversation by sneaking in an undesirable instruction between benign ones. The approach has been codenamed Deceptive Delight by Palo Alto Networks Unit…
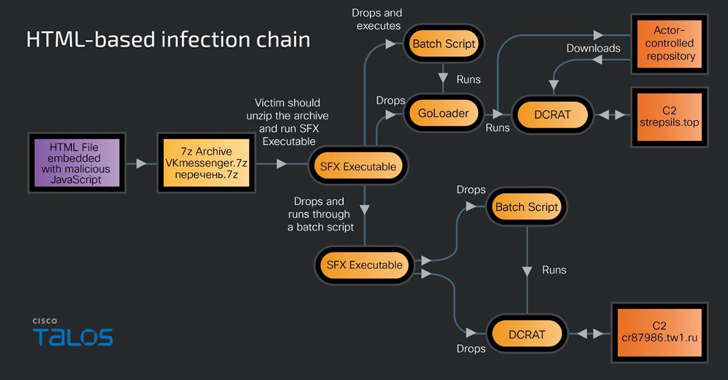
Read MoreRussian-speaking users have become the target of a new phishing campaign that leverages an open-source phishing toolkit called Gophish to deliver DarkCrystal RAT (aka DCRat) and a previously undocumented remote access trojan dubbed PowerRAT. “The campaign involves modular infection chains that are either Maldoc or HTML-based infections and require the victim’s intervention to trigger the…
Read MoreOct 22, 2024Ravie LakshmananDocker Security / Cloud Security Bad actors have been observed targeting Docker remote API servers to deploy the SRBMiner crypto miner on compromised instances, according to new findings from Trend Micro. “In this attack, the threat actor used the gRPC protocol over h2c to evade security solutions and execute their crypto mining…
Read MoreOct 22, 2024Ravie LakshmananVulnerability / Software Security Details have emerged about a now-patched security flaw in Styra’s Open Policy Agent (OPA) that, if successfully exploited, could have led to leakage of New Technology LAN Manager (NTLM) hashes. “The vulnerability could have allowed an attacker to leak the NTLM credentials of the OPA server’s local user…
Read MoreOct 22, 2024Ravie LakshmananIdentity Management / Security Automation Service accounts are vital in any enterprise, running automated processes like managing applications or scripts. However, without proper monitoring, they can pose a significant security risk due to their elevated privileges. This guide will walk you through how to locate and secure these accounts within Active Directory…
Read MoreOct 22, 2024Ravie LakshmananVulnerability / Supply Chain Cybersecurity researchers have discovered a number of suspicious packages published to the npm registry that are designed to harvest Ethereum private keys and gain remote access to the machine via the secure shell (SSH) protocol. The packages attempt to “gain SSH access to the victim’s machine by writing…
Read MoreRecent Posts
- Bob Sullivan Discovers a Scam That Strikes Twice
- A Vulnerability in Apache Struts2 Could Allow for Remote Code Execution
- CISA Adds One Known Exploited Vulnerability to Catalog | CISA
- Xerox To Buy Lexmark For $1.5B In Blockbuster Print Deal
- Vulnerability Summary for the Week of December 16, 2024 | CISA