Tag: cyber news
Sep 17, 2024Ravie LakshmananCryptocurrency / Malware Cryptocurrency exchange Binance is warning of an “ongoing” global threat that’s targeting cryptocurrency users with clipper malware with the goal of facilitating financial fraud. Clipper malware, also called ClipBankers, is a type of malware that Microsoft calls cryware, which comes with capabilities to monitor a victim’s clipboard activity and…
Read MoreSep 17, 2024Ravie LakshmananSoftware Security / Data Protection SolarWinds has released fixes to address two security flaws in its Access Rights Manager (ARM) software, including a critical vulnerability that could result in remote code execution. The vulnerability, tracked as CVE-2024-28991, is rated 9.0 out of a maximum of 10.0 on the CVSS scoring system. It…
Read MoreSep 16, 2024Ravie LakshmananFinancial Security / Malware Cybersecurity researchers are continuing to warn about North Korean threat actors’ attempts to target prospective victims on LinkedIn to deliver malware called RustDoor. The latest advisory comes from Jamf Threat Labs, which said it spotted an attack attempt in which a user was contacted on the professional social…
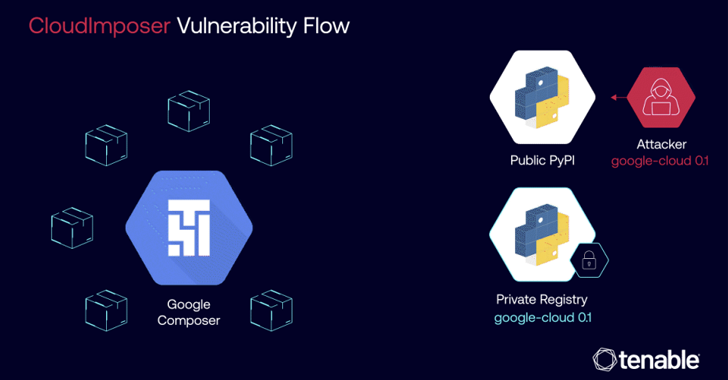
Read MoreSep 16, 2024Ravie LakshmananCloud Security / Vulnerability A now-patched critical security flaw impacting Google Cloud Platform (GCP) Composer could have been exploited to achieve remote code execution on cloud servers by means of a supply chain attack technique called dependency confusion. The vulnerability has been codenamed CloudImposer by Tenable Research. “The vulnerability could have allowed…
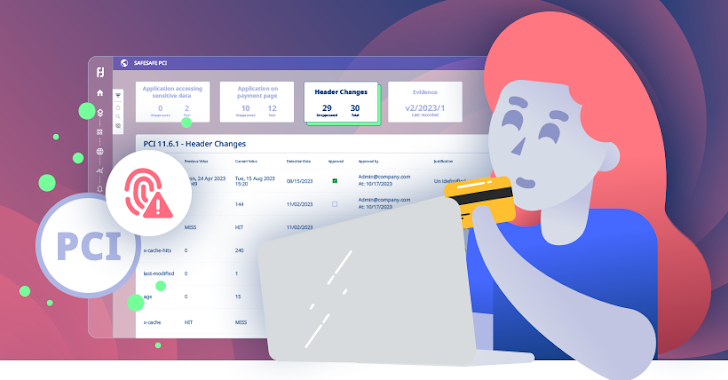
Read MoreSep 16, 2024The Hacker NewsPayment Security / Data Protection The PCI DSS landscape is evolving rapidly. With the Q1 2025 deadline looming ever larger, businesses are scrambling to meet the stringent new requirements of PCI DSS v4.0. Two sections in particular, 6.4.3 and 11.6.1, are troublesome as they demand that organizations rigorously monitor and manage…
Read MoreSep 16, 2024The Hacker NewsIdentity Protection / Incident Response Imagine this… You arrive at work to a chaotic scene. Systems are down, panic is in the air. The culprit? Not a rogue virus, but a compromised identity. The attacker is inside your walls, masquerading as a trusted user. This isn’t a horror movie, it’s the…
Read MoreSep 16, 2024Ravie LakshmananSpyware / Threat Intelligence Apple has filed a motion to “voluntarily” dismiss its lawsuit against commercial spyware vendor NSO Group, citing a shifting risk landscape that could lead to exposure of critical “threat intelligence” information. The development was first reported by The Washington Post on Friday. The iPhone maker said its efforts,…
Read MoreCybersecurity researchers have warned of ongoing phishing campaigns that abuse refresh entries in HTTP headers to deliver spoofed email login pages that are designed to harvest users’ credentials. “Unlike other phishing webpage distribution behavior through HTML content, these attacks use the response header sent by a server, which occurs before the processing of the HTML…
Read MoreSep 14, 2024Ravie LakshmananEnterprise Security / Threat Intelligence Ivanti has revealed that a newly patched security flaw in its Cloud Service Appliance (CSA) has come under active exploitation in the wild. The high-severity vulnerability in question is CVE-2024-8190 (CVSS score: 7.2), which allows remote code execution under certain circumstances. “An OS command injection vulnerability in…
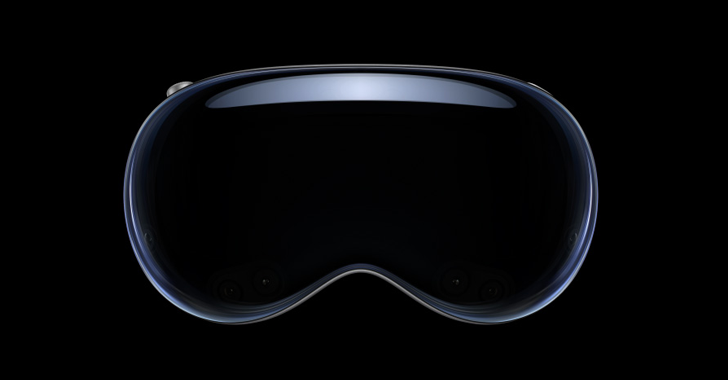
Read MoreSep 13, 2024Ravie LakshmananVirtual Reality / Vulnerability Details have emerged about a now-patched security flaw impacting Apple’s Vision Pro mixed reality headset that, if successfully exploited, could allow malicious attackers to infer data entered on the device’s virtual keyboard. The attack, dubbed GAZEploit, has been assigned the CVE identifier CVE-2024-40865. “A novel attack that can…
Read More