Tag: cyber news
A guide to finding the right endpoint detection and response (EDR) solution for your business’ unique needs. Cybersecurity has become an ongoing battle between hackers and small- and mid-sized businesses. Though perimeter security measures like antivirus and firewalls have traditionally served as the frontlines of defense, the battleground has shifted to endpoints. This is why…
Read MoreMay 10, 2024NewsroomBrowser Security / Vulnerability Google on Thursday released security updates to address a zero-day flaw in Chrome that it said has been actively exploited in the wild. Tracked as CVE-2024-4671, the high-severity vulnerability has been described as a case of use-after-free in the Visuals component. It was reported by an anonymous researcher on…
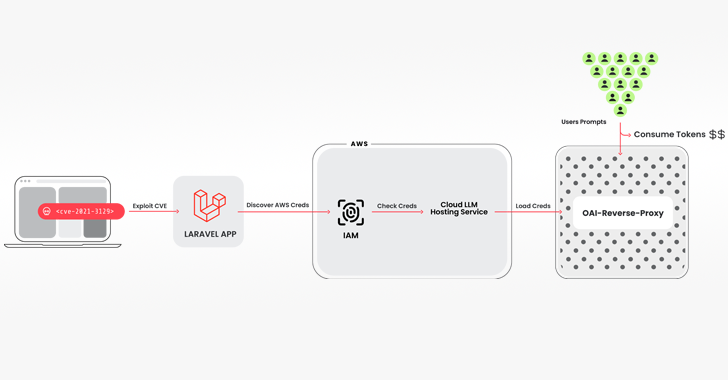
Read MoreMay 10, 2024NewsroomVulnerability / Cloud Security Cybersecurity researchers have discovered a novel attack that employs stolen cloud credentials to target cloud-hosted large language model (LLM) services with the goal of selling access to other threat actors. The attack technique has been codenamed LLMjacking by the Sysdig Threat Research Team. “Once initial access was obtained, they…
Read MoreMay 09, 2024NewsroomEncryption / Data Privacy Researchers have detailed a Virtual Private Network (VPN) bypass technique dubbed TunnelVision that allows threat actors to snoop on victim’s network traffic by just being on the same local network. The “decloaking” method has been assigned the CVE identifier CVE-2024-3661 (CVSS score: 7.6). It impacts all operating systems that…
Read MoreMay 09, 2024NewsroomMobile Security / Cyber Attack Polish government institutions have been targeted as part of a large-scale malware campaign orchestrated by a Russia-linked nation-state actor called APT28. “The campaign sent emails with content intended to arouse the recipient’s interest and persuade him to click on the link,” the computer emergency response team, CERT Polska,…
Read MoreMay 09, 2024NewsroomNetwork Security / Botnet Two recently disclosed security flaws in Ivanti Connect Secure (ICS) devices are being exploited to deploy the infamous Mirai botnet. That’s according to findings from Juniper Threat Labs, which said the vulnerabilities CVE-2023-46805 and CVE-2024-21887 have been leveraged to deliver the botnet payload. While CVE-2023-46805 is an authentication bypass…
Read MoreMay 09, 2024The Hacker NewsvCISO / Regulatory Compliance Cybersecurity and compliance guidance are in high demand among SMEs. However, many of them cannot afford to hire a full-time CISO. A vCISO can answer this need by offering on-demand access to top-tier cybersecurity expertise. This is also an opportunity for MSPs and MSSPs to grow their…
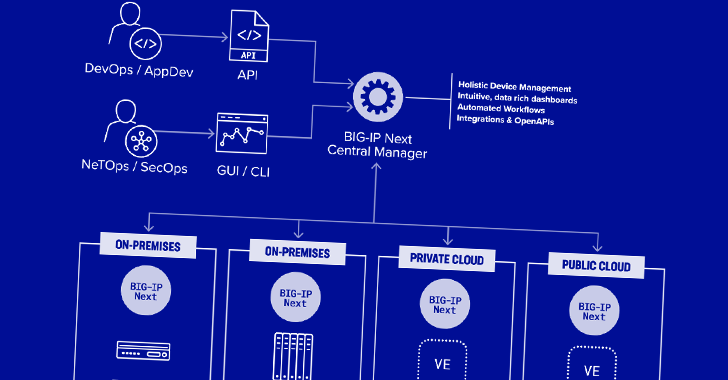
Read MoreMay 09, 2024NewsroomFirewall / Network Security Two security vulnerabilities have been discovered in F5 Next Central Manager that could be exploited by a threat actor to seize control of the devices and create hidden rogue administrator accounts for persistence. The remotely exploitable flaws “can give attackers full administrative control of the device, and subsequently allow…
Read MoreMay 08, 2024NewsroomData Encryption / Hardware Security Researchers have discovered two novel attack methods targeting high-performance Intel CPUs that could be exploited to stage a key recovery attack against the Advanced Encryption Standard (AES) algorithm. The techniques have been collectively dubbed Pathfinder by a group of academics from the University of California San Diego, Purdue…
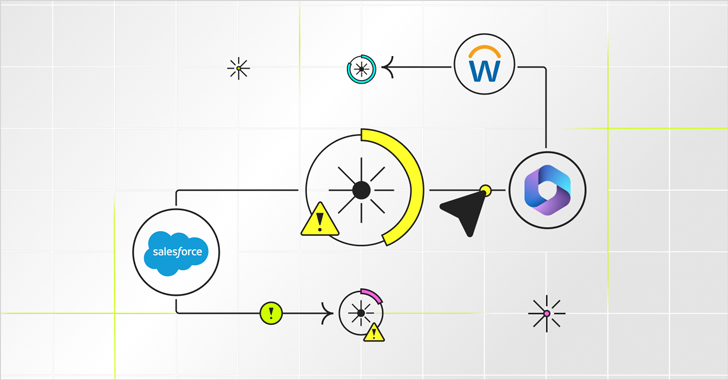
Read MorePermissions in SaaS platforms like Salesforce, Workday, and Microsoft 365 are remarkably precise. They spell out exactly which users have access to which data sets. The terminology differs between apps, but each user’s base permission is determined by their role, while additional permissions may be granted based on tasks or projects they are involved with.…
Read More