Tag: cyber resilience
The content of this post is solely the responsibility of the author. LevelBlue does not adopt or endorse any of the views, positions, or information provided by the author in this article. No, I am not taking a photo of my nose hair! I am Snapping and sharing for my Snapgroup to keep my Snapstreak active while I see where they are…
Read MoreThe content of this post is solely the responsibility of the author. LevelBlue does not adopt or endorse any of the views, positions, or information provided by the author in this article. Most companies have some cybersecurity protocols in place in case of a breach. They could be anything from antivirus software to spam filters.…
Read MoreThe content of this post is solely the responsibility of the author. LevelBlue does not adopt or endorse any of the views, positions, or information provided by the author in this article. Cloud computing has become a boon to organizations due to its flexibility, scalability, and cost-effectiveness. However, without proper oversight, it evolves into an…
Read MoreThe content of this post is solely the responsibility of the author. LevelBlue does not adopt or endorse any of the views, positions, or information provided by the author in this article. From stolen personal data to entire corporate databases, Raid Forums was a digital black market where the most valuable commodities weren’t physical goods…
Read MoreThe content of this post is solely the responsibility of the author. LevelBlue does not adopt or endorse any of the views, positions, or information provided by the author in this article. As we gear up to celebrate Internet Day on October 29th, let’s take a moment to appreciate how much the Internet has revolutionized…
Read MoreWhen you think of a cyberattack, you probably envision a sophisticated hacker behind a Matrix-esque screen actively penetrating networks with their technical prowess. However, the reality of many attacks is far more mundane. A simple email with an innocent subject line such as “Missed delivery attempt” sits in an employee’s spam folder. They open it…
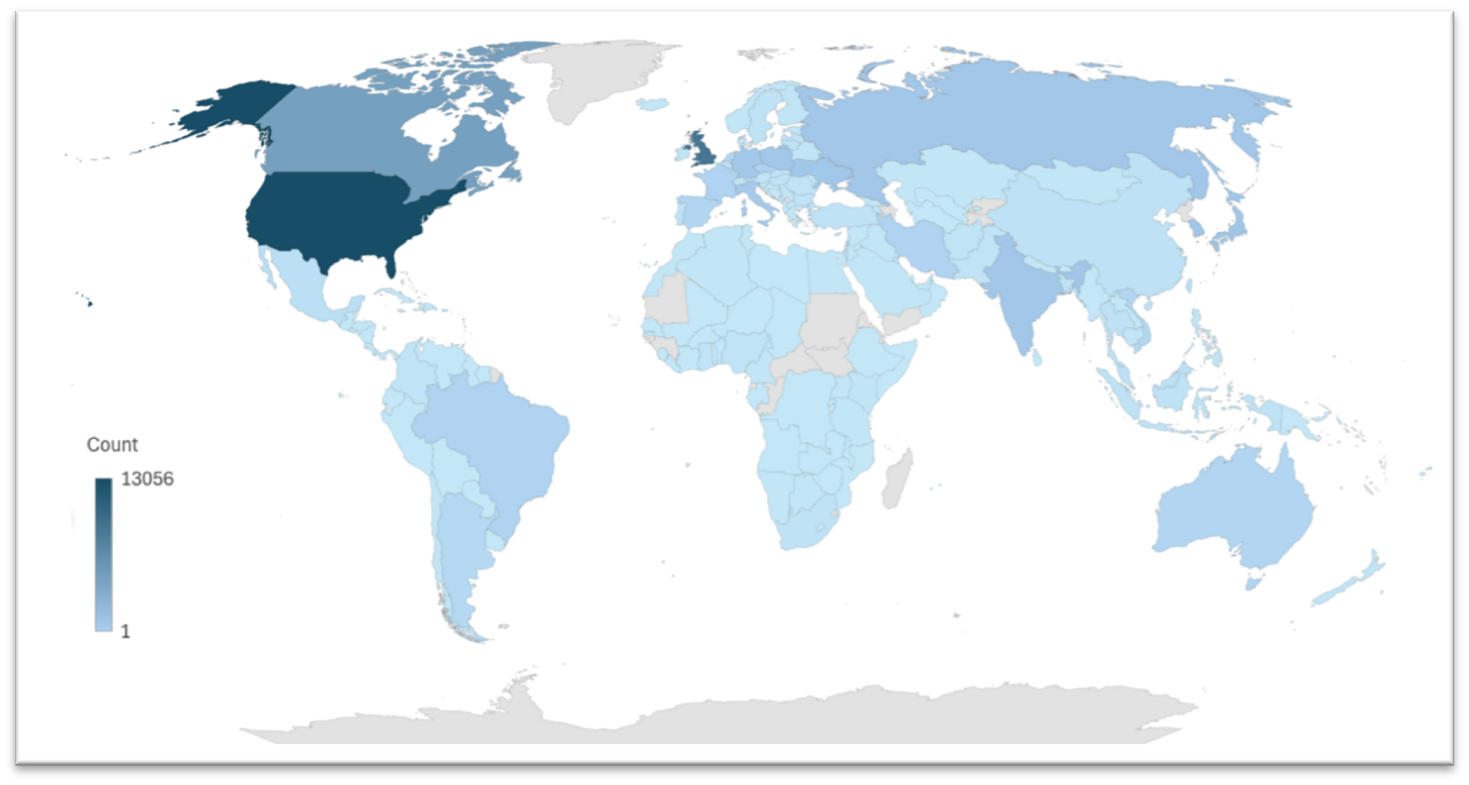
Read MoreExecutive Summary Seven years after its first appearance, the proxy server botnet Ngioweb continues its impactful presence on the internet with barely any relevant changes in its original code. Threat actors have continued to actively use Nbioweb extensively to scan for vulnerable devices (including a new arsenal of exploits) which can be turned into new…
Read MoreThe content of this post is solely the responsibility of the author. LevelBlue does not adopt or endorse any of the views, positions, or information provided by the author in this article. Over the last decade, web applications have become integral to everyday life. This includes business and personal activities, facilitating everything from banking and…
Read MoreThe content of this post is solely the responsibility of the author. LevelBlue does not adopt or endorse any of the views, positions, or information provided by the author in this article. Summer is a time for relaxation, travel, and spending quality moments with family and friends. However, it is also peak season for cybercriminals…
Read MoreThe content of this post is solely the responsibility of the author. LevelBlue does not adopt or endorse any of the views, positions, or information provided by the author in this article. Maintaining an active social media presence can be a great way to improve brand visibility and generate leads, but it also opens the…
Read MoreRecent Posts
- Hackers abuse popular Godot game engine to infect thousands of PCs
- Hackers exploit ProjectSend flaw to backdoor exposed servers
- Zello asks users to reset passwords after security incident
- Microsoft says it’s not using your Word, Excel data for AI training
- Ransomware Meets Retail: Sainsbury’s, Starbucks and Morrisons Feel the Heat from Blue Yonder Attack | BlackFog