Tag: cyber security news
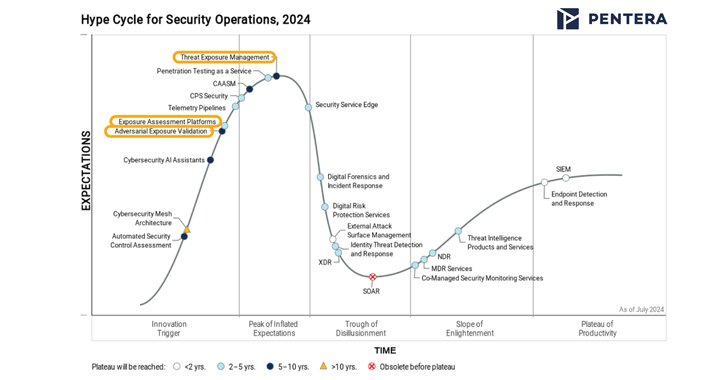
Want to know what’s the latest and greatest in SecOps for 2024? Gartner’s recently released Hype Cycle for Security Operations report takes important steps to organize and mature the domain of Continuous Threat Exposure Management, aka CTEM. Three categories within this domain are included in this year’s report: Threat Exposure Management, Exposure Assessment Platforms (EAP),…
Read MoreAug 27, 2024Ravie LakshmananVulnerability / Browser Security Google has revealed that a security flaw that was patched as part of a security update rolled out last week to its Chrome browser has come under active exploitation in the wild. Tracked as CVE-2024-7965, the vulnerability has been described as an inappropriate implementation bug in the V8…
Read MoreAug 27, 2024Ravie LakshmananAI Security / Vulnerability Details have emerged about a now-patched vulnerability in Microsoft 365 Copilot that could enable the theft of sensitive user information using a technique called ASCII smuggling. “ASCII Smuggling is a novel technique that uses special Unicode characters that mirror ASCII but are actually not visible in the user…
Read MoreAug 26, 2024Ravie LakshmananGDPR / Data Protection The Dutch Data Protection Authority (DPA) has fined Uber a record €290 million ($324 million) for allegedly failing to comply with European Union (E.U.) data protection standards when sending sensitive driver data to the U.S. “The Dutch DPA found that Uber transferred personal data of European taxi drivers…
Read MoreAug 26, 2024Ravie LakshmananVulnerability / Enterprise Security SonicWall has released security updates to address a critical flaw impacting its firewalls that, if successfully exploited, could grant malicious actors unauthorized access to the devices. The vulnerability, tracked as CVE-2024-40766 (CVSS score: 9.3), has been described as an improper access control bug. “An improper access control vulnerability…
Read MoreAug 26, 2024The Hacker NewsData Security / Compliance Nowadays, sensitive and critical data is traveling in everyday business channels that offer only the basic level of security and encryption, and companies are often oblivious to the risk. A case in point: Disney suffered a devastating data leak by a hacktivist group known as NullBulge that…
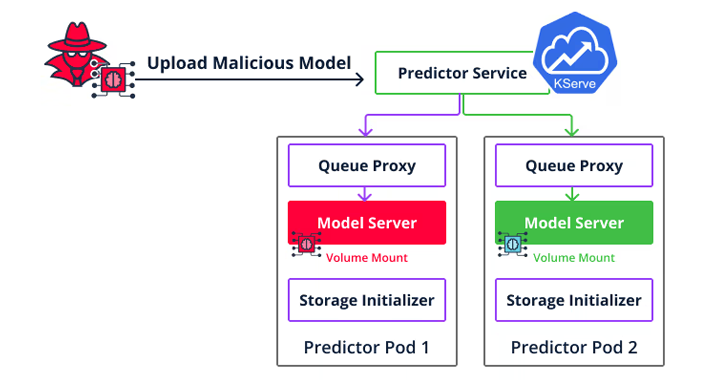
Read MoreCybersecurity researchers are warning about the security risks in the machine learning (ML) software supply chain following the discovery of more than 20 vulnerabilities that could be exploited to target MLOps platforms. These vulnerabilities, which are described as inherent- and implementation-based flaws, could have severe consequences, ranging from arbitrary code execution to loading malicious datasets.…
Read MoreAug 26, 2024Ravie LakshmananSoftware Security / Vulnerability Two security vulnerabilities have been disclosed in the open-source Traccar GPS tracking system that could be potentially exploited by unauthenticated attackers to achieve remote code execution under certain circumstances. Both the vulnerabilities are path traversal flaws and could be weaponized if guest registration is enabled, which is the…
Read MoreAug 26, 2024Ravie LakshmananFinancial Fraud / Mobile Security Cybersecurity researchers have uncovered new Android malware that can relay victims’ contactless payment data from physical credit and debit cards to an attacker-controlled device with the goal of conducting fraudulent operations. The Slovak cybersecurity company is tracking the novel malware as NGate, stating it observed the crimeware…
Read MoreAug 25, 2024Ravie LakshmananFinancial Fraud / Cybercrime Cybersecurity researchers have uncovered a new stealthy piece of Linux malware that leverages an unconventional technique to achieve persistence on infected systems and hide credit card skimmer code. The malware, attributed to a financially motivated threat actor, has been codenamed sedexp by Aon’s Stroz Friedberg incident response services…
Read More