Tag: cyber security news
Jul 17, 2024NewsroomVulnerability / Data Security Threat actors are actively exploiting a recently disclosed critical security flaw impacting Apache HugeGraph-Server that could lead to remote code execution attacks. Tracked as CVE-2024-27348 (CVSS score: 9.8), the vulnerability impacts all versions of the software before 1.3.0. It has been described as a remote command execution flaw in…
Read MoreJul 16, 2024NewsroomMobile Security / Online Security ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt…
Read MoreIdentity-based threats on SaaS applications are a growing concern among security professionals, although few have the capabilities to detect and respond to them. According to the US Cybersecurity and Infrastructure Security Agency (CISA), 90% of all cyberattacks begin with phishing, an identity-based threat. Throw in attacks that use stolen credentials, over-provisioned accounts, and insider threats,…
Read MoreThe Iranian nation-state actor known as MuddyWater has been observed using a never-before-seen backdoor as part of a recent attack campaign, shifting away from its well-known tactic of deploying legitimate remote monitoring and management (RMM) software for maintaining persistent access. That’s according to independent findings from cybersecurity firms Check Point and Sekoia, which have codenamed…
Read MoreJul 16, 2024NewsroomOpen Source / Software Supply Chain Cybersecurity researchers have identified two malicious packages on the npm package registry that concealed backdoor code to execute malicious commands sent from a remote server. The packages in question – img-aws-s3-object-multipart-copy and legacyaws-s3-object-multipart-copy – have been downloaded 190 and 48 times each. As of writing, they have…
Read MoreJul 16, 2024NewsroomData Security / Vulnerability An advanced persistent threat (APT) group called Void Banshee has been observed exploiting a recently disclosed security flaw in the Microsoft MHTML browser engine as a zero-day to deliver an information stealer called Atlantida. Cybersecurity firm Trend Micro, which observed the activity in mid-May 2024, the vulnerability – tracked…
Read MoreJul 16, 2024NewsroomVulnerability / Infrastructure Security The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added a critical security flaw impacting OSGeo GeoServer GeoTools to its Known Exploited Vulnerabilities (KEV) catalog, based on evidence of active exploitation. GeoServer is an open-source software server written in Java that allows users to share and edit geospatial…
Read MoreJul 16, 2024NewsroomNational Security / Data Security Russian security vendor Kaspersky has said it’s exiting the U.S. market nearly a month after the Commerce Department announced a ban on the sale of its software in the country citing a national security risk. News of the closure was first reported by journalist Kim Zetter. The company…
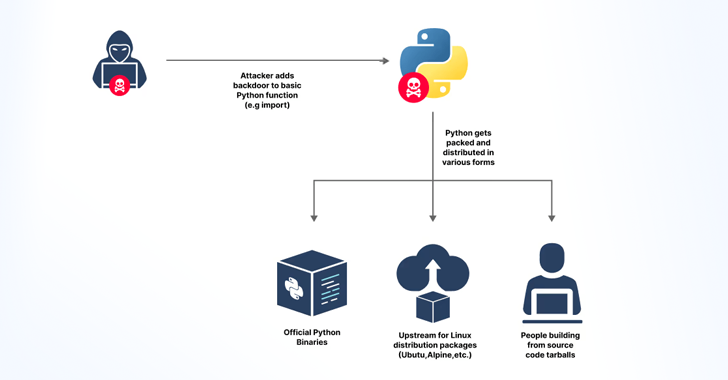
Read MoreJul 15, 2024NewsroomSupply Chain Attack / Cyber Threat Cybersecurity researchers said they discovered an accidentally leaked GitHub token that could have granted elevated access to the GitHub repositories of the Python language, Python Package Index (PyPI), and the Python Software Foundation (PSF) repositories. JFrog, which found the GitHub Personal Access Token, said the secret was…
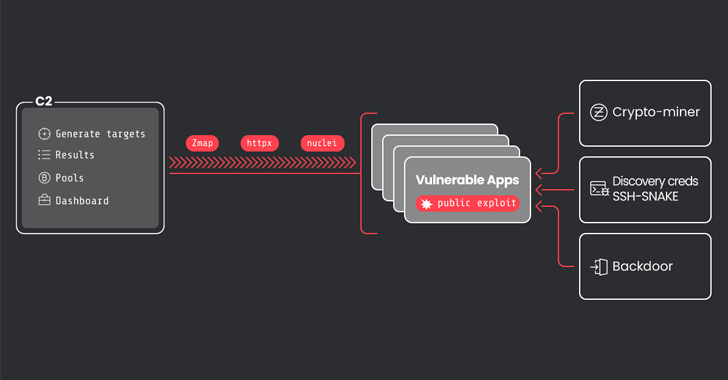
Read MoreJul 15, 2024NewsroomSaaS Security / Vulnerability A threat actor that was previously observed using an open-source network mapping tool has greatly expanded their operations to infect over 1,500 victims. Sysdig, which is tracking the cluster under the name CRYSTALRAY, said the activities have witnessed a 10x surge, adding it includes “mass scanning, exploiting multiple vulnerabilities,…
Read MoreRecent Posts
- Trump Touts New $20B Data Center Investment In US
- AMD Wins Over Dell In Commercial PC Deal For Ryzen AI Pro Chips
- Google Gemini AI Coming To TVs And Smartwatches: CES 2025
- CISA Adds Three Known Exploited Vulnerabilities to Catalog | CISA
- CISA Releases Two Industrial Control Systems Advisories | CISA