Tag: Cybersecurity
In our annual Stellar Startups special report, CRN shines a spotlight on some of the most exciting channel-focused startup vendors with leading-edge technologies that are creating new opportunities for solution providers. The pace of IT industry innovation, always moving at a brisk clip, has accelerated to a full-on sprint over the last two years with…
Read More‘It’s nice to see them focus on what MSPs need. In the last few years, they’ve been focused on big trends. This is a return to basics in a good way,’ says Dustin Bolander, founder, partner and CIO of Clear Guidance Partners. ConnectWise Chief Product Officer Jeff Bishop said the company’s new Asio platform is…
Read MoreFor the week ending Nov. 8, CRN takes a look at the companies that brought their ‘A’ game to the channel including Ingram Micro, CrowdStrike, Accenture, Cynomi and Nerdio. The Week Ending Nov. 8 Topping this week’s Came to Win list is distributor Ingram Micro for its latest steps to help solution providers work with…
Read MoreWith global spending on the technology industry expected to reach $5.74 trillion in 2025, CRN breaks down the five largest markets that will reap the most revenue next year, according to new data from Gartner. Worldwide spending on IT will hit a record $5.74 trillion in 2025 with all areas of technology—from software to communications…
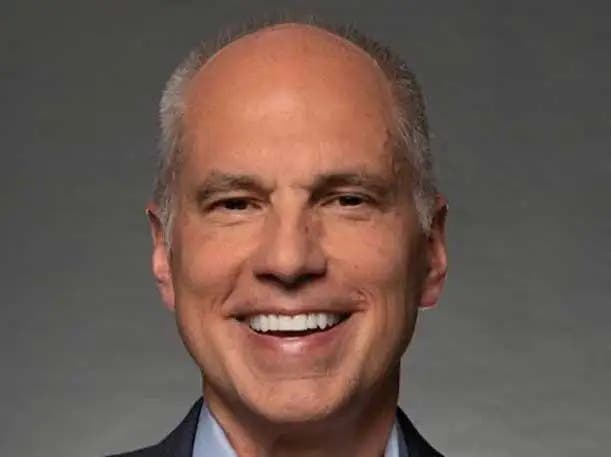
Read More‘We’ve been talking about Asio for numerous years. We’ve been showing you glimpses of Asio. I’m here to tell you that we are at that tipping point. I’m here to tell you that it is ready for prime time,’ ConnectWise CEO Manny Rivelo told IT Nation 2024 ConnectWise CEO Manny Rivelo said the long-promised Asio…
Read MoreThe results from Q3 are ‘further validating our view that the firewall market is recovering,’ Fortinet CFO Keith Jensen said Thursday. Fortinet is once again seeing growth from its firewall business after several quarters of decline in the cybersecurity vendor’s largest segment, executives said Thursday. While specifics on the firewall growth were not disclosed, during…
Read MoreThe vulnerability affects Palo Alto Networks’ Expedition migration tool and was originally disclosed in July. A critical-severity vulnerability affecting a Palo Alto Networks tool — originally disclosed in July — is now known to have been exploited in cyberattacks, according to the U.S. Cybersecurity and Infrastructure Security Agency (CISA). CISA released an advisory Thursday mentioning…
Read MoreSonicWall CEO Bob VanKirk tells CRN that the launch of a major new SMB firewall is just the latest in a series of moves this year focused on ‘transformation’ of the company. SonicWall’s unveiling of a major new SMB firewall Thursday is just the latest in a series of moves this year focused on “transformation”…
Read MoreLeft unchecked, ‘generative AI in the software development process is going to produce worse outcomes from a software security perspective,’ says software security pioneer and Veracode Co-Founder Chris Wysopal. While generative AI continues to deliver massive boosts to workplace productivity as adoption climbs, the trade-offs for security are becoming increasingly evident, as well, according to…
Read MoreFrom AI governance platforms and polyfunctional robots to energy-efficient and spatial computing, here are the top 10 technology trends and use cases for 2025, according to Gartner’s new report. IT research firm Gartner predicts the 10 biggest technology trends of 2025, which includes the rise of agentic AI technology, demand for disinformation cybersecurity solutions and…
Read MoreRecent Posts
- Bob Sullivan Discovers a Scam That Strikes Twice
- A Vulnerability in Apache Struts2 Could Allow for Remote Code Execution
- CISA Adds One Known Exploited Vulnerability to Catalog | CISA
- Xerox To Buy Lexmark For $1.5B In Blockbuster Print Deal
- Vulnerability Summary for the Week of December 16, 2024 | CISA