Tag: data breach
Executive Summary Phishing remains a popular method of stealing credentials, committing fraud, and distributing malware. But what appears on the surface to be a juvenile form of cybercrime can be, in practice, a well-orchestrated, multi-faceted, and sustained attack campaign by organized crime groups. From finding victims and creating phishing sites to harvesting and fraudulently using…
Read MoreAPIs and Sectors As more APIs are published, both by large enterprises who want to make their data more available (such as Google) and by smaller, industry-specific organizations hoping to generate value, some interesting industry patterns are also emerging. Of the organizations for which we had sector information, social networking organizations made up the largest…
Read MoreThe title of this report is not a typo. “The State of the State of Application Exploits in Security Incidents” is a meta-analysis of several prominent industry reports, each of which covers the state of application security, hence the name, “the state of the state of.” This report is both an attempt to stitch together…
Read MoreMitigation Coverage Restrict web-based content 7 Disable or remove feature or program 5 Multifactor authentication 5 Network segmentation 5 User training 5 Application isolation and sandboxing 4 Exploit protection 4 Network intrusion prevention 4 Privileged account management 4 User account management 4 Antivirus/antimalware 3 Data backup 3 Filter network traffic 3 Password policies 3 Update…
Read MoreMuch of our threat research is focused on analyzing quantitative threat data—the larger the sample size, the better. However, the critical piece of information about a specific attack, the thing that differentiates it from the attacks that happened the day before or after, often lies in minute detail that is rarely captured in a large…
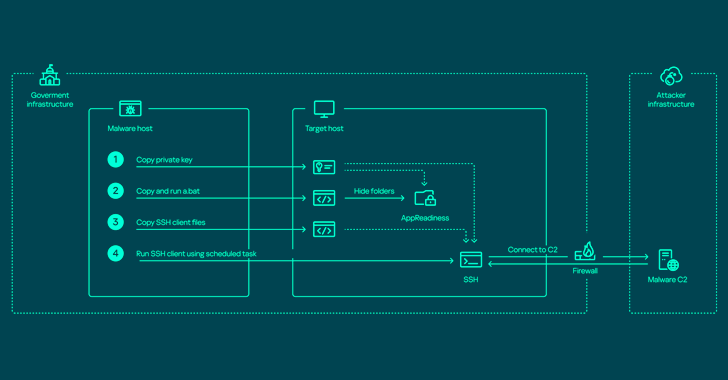
Read MoreApr 22, 2024NewsroomNetwork Security / Endpoint Security The threat actor known as ToddyCat has been observed using a wide range of tools to retain access to compromised environments and steal valuable data. Russian cybersecurity firm Kaspersky characterized the adversary as relying on various programs to harvest data on an “industrial scale” from primarily governmental organizations,…
Read MoreApr 22, 2024The Hacker NewsNetwork Security / Cybersecurity The MITRE Corporation revealed that it was the target of a nation-state cyber attack that exploited two zero-day flaws in Ivanti Connect Secure appliances starting in January 2024. The intrusion led to the compromise of its Networked Experimentation, Research, and Virtualization Environment (NERVE), an unclassified research and…
Read MorePentera’s 2024 Report Reveals Hundreds of Security Events per Week, Highlighting the Criticality of Continuous Validation
by nlqip
Over the past two years, a shocking 51% of organizations surveyed in a leading industry report have been compromised by a cyberattack. Yes, over half. And this, in a world where enterprises deploy an average of 53 different security solutions to safeguard their digital domain. Alarming? Absolutely. A recent survey of CISOs and CIOs, commissioned…
Read MoreBetween crossovers – Do threat actors play dirty or desperate? In our dataset of over 11,000 victim organizations that have experienced a Cyber Extortion / Ransomware attack, we noticed that some victims re-occur. Consequently, the question arises why we observe a re-victimization and whether or not this is an actual second attack, an affiliate crossover…
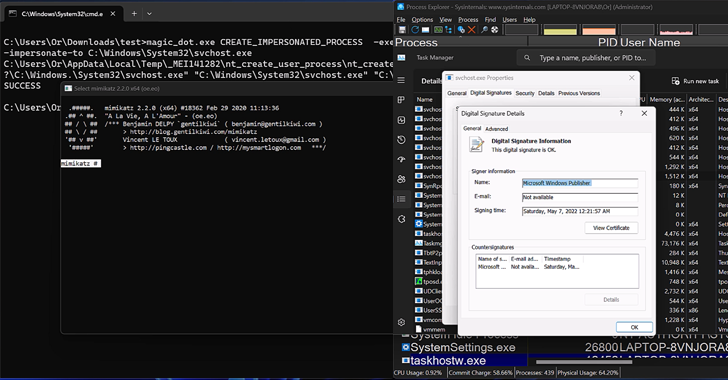
Read MoreApr 22, 2024NewsroomRootkit / Software Security New research has found that the DOS-to-NT path conversion process could be exploited by threat actors to achieve rootkit-like capabilities to conceal and impersonate files, directories, and processes. “When a user executes a function that has a path argument in Windows, the DOS path at which the file or…
Read More