Tag: hacking news
Nov 07, 2024Ravie LakshmananThreat Intelligence / Cyber Espionage The China-aligned threat actor known as MirrorFace has been observed targeting a diplomatic organization in the European Union, marking the first time the hacking crew has targeted an entity in the region. “During this attack, the threat actor used as a lure the upcoming World Expo, which…
Read MoreNov 07, 2024The Hacker NewsPassword Security / Network Security Defending your organization’s security is like fortifying a castle—you need to understand where attackers will strike and how they’ll try to breach your walls. And hackers are always searching for weaknesses, whether it’s a lax password policy or a forgotten backdoor. To build a stronger defense,…
Read MoreA threat actor with ties to the Democratic People’s Republic of Korea (DPRK) has been observed targeting cryptocurrency-related businesses with a multi-stage malware capable of infecting Apple macOS devices. Cybersecurity company SentinelOne, which dubbed the campaign Hidden Risk, attributed it with high confidence to BlueNoroff, which has been previously linked to malware families such as…
Read MoreNov 07, 2024Ravie LakshmananVulnerability / Cloud Security Cybersecurity researchers have discovered a malicious package on the Python Package Index (PyPI) that has racked up thousands of downloads for over three years while stealthily exfiltrating developers’ Amazon Web Services (AWS) credentials. The package in question is “fabrice,” which typosquats a popular Python library known as “fabric,”…
Read MoreAn ongoing phishing campaign is employing copyright infringement-related themes to trick victims into downloading a newer version of the Rhadamanthys information stealer since July 2024. Cybersecurity firm Check Point is tracking the large-scale campaign under the name CopyRh(ight)adamantys. Targeted regions include the United States, Europe, East Asia, and South America. “The campaign impersonates dozens of…
Read MoreTactics, techniques, and procedures (TTPs) form the foundation of modern defense strategies. Unlike indicators of compromise (IOCs), TTPs are more stable, making them a reliable way to identify specific cyber threats. Here are some of the most commonly used techniques, according to ANY.RUN’s Q3 2024 report on malware trends, complete with real-world examples. Disabling of…
Read MoreNov 07, 2024Ravie LakshmananVulnerability / Wireless Technology Cisco has released security updates to address a maximum severity security flaw impacting Ultra-Reliable Wireless Backhaul (URWB) Access Points that could permit unauthenticated, remote attackers to run commands with elevated privileges. Tracked as CVE-2024-20418 (CVS score: 10.0), the vulnerability has been described as stemming from a lack of…
Read MoreNov 07, 2024Ravie LakshmananNational Security / Social Media The Canadian government on Wednesday ordered ByteDance-owned TikTok to dissolve its operations in the country, citing national security risks, but stopped short of instituting a ban on the popular video-sharing platform. “The decision was based on the information and evidence collected over the course of the review…
Read MoreNov 06, 2024Ravie LakshmananSaaS Security / Threat Detection An ongoing threat campaign dubbed VEILDrive has been observed taking advantage of legitimate services from Microsoft, including Teams, SharePoint, Quick Assist, and OneDrive, as part of its modus operandi. “Leveraging Microsoft SaaS services — including Teams, SharePoint, Quick Assist, and OneDrive — the attacker exploited the trusted…
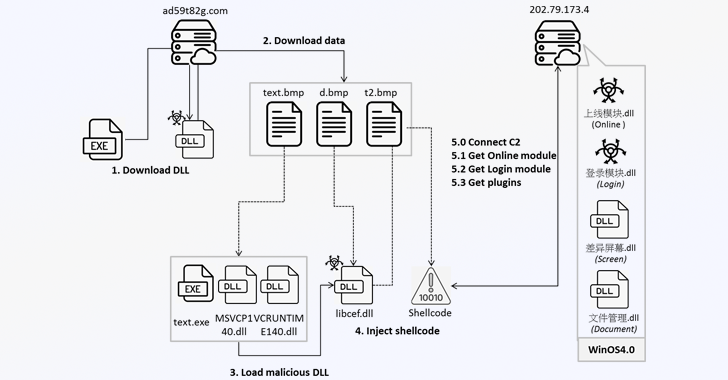
Read MoreNov 06, 2024Ravie LakshmananMalware / Online Security Cybersecurity researchers are warning that a command-and-control (C&C) framework called Winos is being distributed within gaming-related applications like installation tools, speed boosters, and optimization utilities. “Winos 4.0 is an advanced malicious framework that offers comprehensive functionality, a stable architecture, and efficient control over numerous online endpoints to execute…
Read MoreRecent Posts
- Tenable Announces the Passing of Chairman and CEO Amit Yoran
- Opinion: Why Nvidia, MediaTek May Enter The PC CPU Market Soon
- Microsoft VP Of Silicon Engineering Jumps To Google Cloud To Head Chip Technology And Manufacturing
- 10 Cloud Startup Companies To Watch In 2025
- Cybersecurity Snapshot: After Telecom Hacks, CISA Offers Security Tips for Cell Phone Users, While Banks Seek Clearer AI Regulations