Tag: how to hack
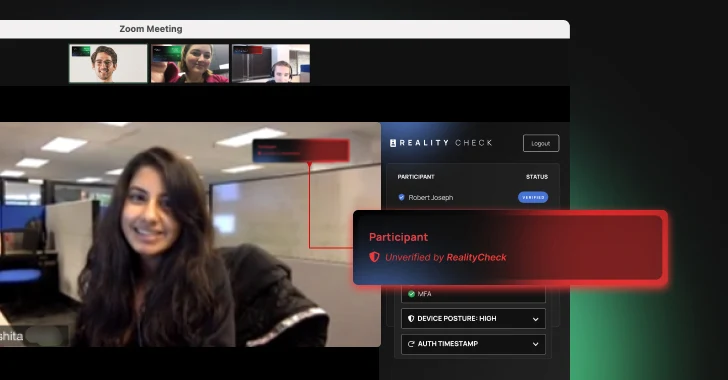
Oct 25, 2024The Hacker NewsArtificial Intelligence / Identity Security Artificial Intelligence (AI) has rapidly evolved from a futuristic concept to a potent weapon in the hands of bad actors. Today, AI-based attacks are not just theoretical threats—they’re happening across industries and outpacing traditional defense mechanisms. The solution, however, is not futuristic. It turns out a…
Read MoreOct 25, 2024Ravie LakshmananRegulatory Compliance / Data Breach The U.S. Securities and Exchange Commission (SEC) has charged four current and former public companies for making “materially misleading disclosures” related to the large-scale cyber attack that stemmed from the hack of SolarWinds in 2020. The SEC said the companies – Avaya, Check Point, Mimecast, and Unisys…
Read MoreOct 25, 2024Ravie LakshmananDigital Advertising / Privacy The Irish data protection watchdog on Thursday fined LinkedIn €310 million ($335 million) for violating the privacy of its users by conducting behavioral analyses of personal data for targeted advertising. “The inquiry examined LinkedIn’s processing of personal data for the purposes of behavioral analysis and targeted advertising of…
Read MoreOct 24, 2024Ravie LakshmananRansomware / Cybercrime Cybersecurity researchers have discovered an advanced version of the Qilin ransomware sporting increased sophistication and tactics to evade detection. The new variant is being tracked by cybersecurity firm Halcyon under the moniker Qilin.B. “Notably, Qilin.B now supports AES-256-CTR encryption for systems with AESNI capabilities, while still retaining Chacha20 for…
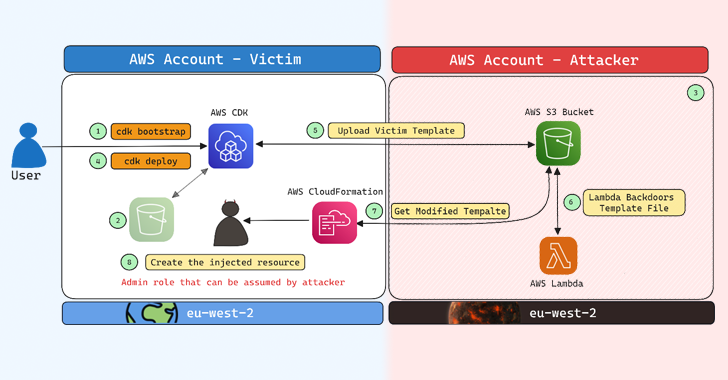
Read MoreCybersecurity researchers have disclosed a security flaw impacting Amazon Web Services (AWS) Cloud Development Kit (CDK) that could have resulted in an account takeover under specific circumstances. “The impact of this issue could, in certain scenarios, allow an attacker to gain administrative access to a target AWS account, resulting in a full account takeover,” Aqua…
Read MoreOct 24, 2024Ravie LakshmananVulnerability / Network Security Cisco on Wednesday said it has released updates to address an actively exploited security flaw in its Adaptive Security Appliance (ASA) that could lead to a denial-of-service (DoS) condition. The vulnerability, tracked as CVE-2024-20481 (CVSS score: 5.8), affects the Remote Access VPN (RAVPN) service of Cisco ASA and…
Read MoreSometimes, it turns out that the answers we struggled so hard to find were sitting right in front of us for so long that we somehow overlooked them. When the Department of Homeland Security, through the Cybersecurity and Infrastructure Security Agency (CISA), in coordination with the FBI, issues a cybersecurity warning and prescribes specific action,…
Read MoreThe North Korean threat actor known as Lazarus Group has been attributed to the zero-day exploitation of a now-patched security flaw in Google Chrome to seize control of infected devices. Cybersecurity vendor Kaspersky said it discovered a novel attack chain in May 2024 that targeted the personal computer of an unnamed Russian national with the…
Read MoreOct 24, 2024Ravie LakshmananVulnerability / Network Security Fortinet has confirmed details of a critical security flaw impacting FortiManager that has come under active exploitation in the wild. Tracked as CVE-2024-47575 (CVSS score: 9.8), the vulnerability is also known as FortiJump and is rooted in the FortiGate to FortiManager (FGFM) protocol. “A missing authentication for critical…
Read MoreNew variants of a banking malware called Grandoreiro have been found to adopt new tactics in an effort to bypass anti-fraud measures, indicating that the malicious software is continuing to be actively developed despite law enforcement efforts to crack down on the operation. “Only part of this gang was arrested: the remaining operators behind Grandoreiro…
Read MoreRecent Posts
- CVE-2025-0282: Ivanti Connect Secure Zero-Day Vulnerability Exploited In The Wild
- Google Cloud Hires Tech Superstar Francis DeSouza As New COO
- AWS Invests $11B In Georgia To ‘Support The Future Of AI’ Via Data Centers
- Google’s Willow Quantum Chip and Its Potential Threat to…
- Citrix Parent Cloud Software Group Confirms Layoffs