Tag: how to hack
May 16, 2024NewsroomVulnerability / Network Security Researchers have discovered a new security vulnerability stemming from a design flaw in the IEEE 802.11 Wi-Fi standard that tricks victims into connecting to a less secure wireless network and eavesdrop on their network traffic. The SSID Confusion attack, tracked as CVE-2023-52424, impacts all operating systems and Wi-Fi clients,…
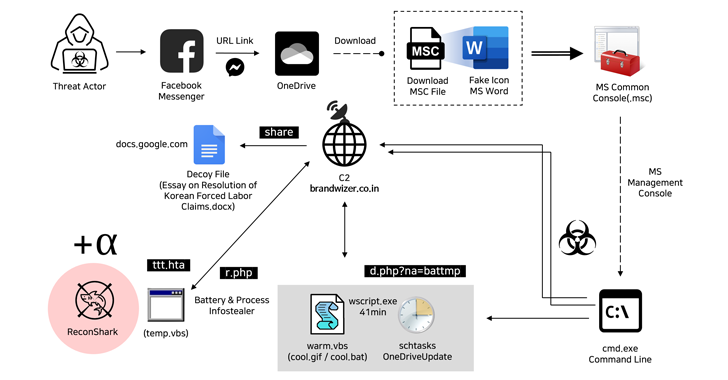
Read MoreMay 16, 2024NewsroomMalware / Cyber Espionage The North Korea-linked Kimsuky hacking group has been attributed to a new social engineering attack that employs fictitious Facebook accounts to targets via Messenger and ultimately delivers malware. “The threat actor created a Facebook account with a fake identity disguised as a public official working in the North Korean…
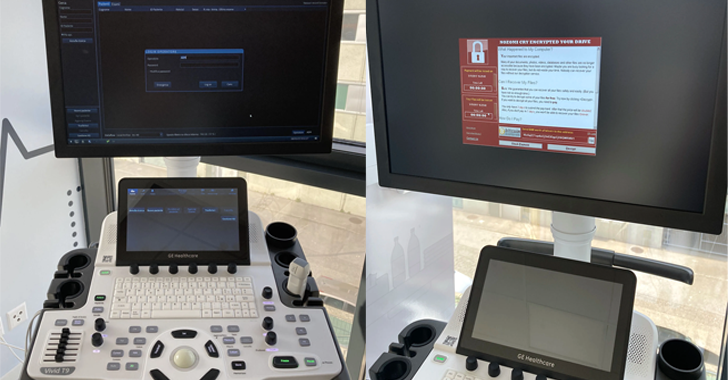
Read MoreSecurity researchers have disclosed almost a dozen security flaws impacting the GE HealthCare Vivid Ultrasound product family that could be exploited by malicious actors to tamper with patient data and even install ransomware under certain circumstances. “The impacts enabled by these flaws are manifold: from the implant of ransomware on the ultrasound machine to the…
Read MoreMay 16, 2024NewsroomBrowser Security / Vulnerability Google has rolled out fixes to address a set of nine security issues in its Chrome browser, including a new zero-day that has been exploited in the wild. Assigned the CVE identifier CVE-2024-4947, the vulnerability relates to a type confusion bug in the V8 JavaScript and WebAssembly engine. It…
Read MoreMay 16, 2024NewsroomRansomware / Incident Response The Microsoft Threat Intelligence team said it has observed a threat it tracks under the name Storm-1811 abusing the client management tool Quick Assist to target users in social engineering attacks. “Storm-1811 is a financially motivated cybercriminal group known to deploy Black Basta ransomware,” the company said in a…
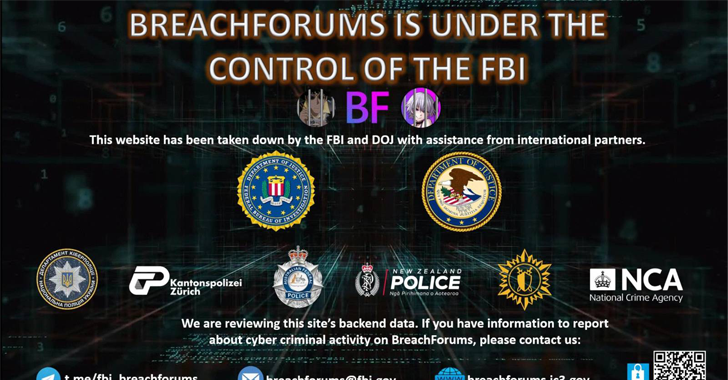
Read MoreMay 15, 2024NewsroomData Breach / Cyber Crime Law enforcement agencies have officially seized control of the notorious BreachForums platform, an online bazaar known for peddling stolen data, for the second time within a year. The website (“breachforums[.]st”) has been replaced by a seizure banner stating the clearnet cybercrime forum is under the control of the…
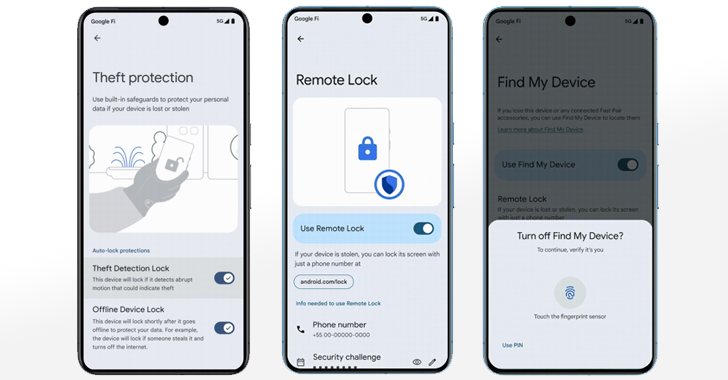
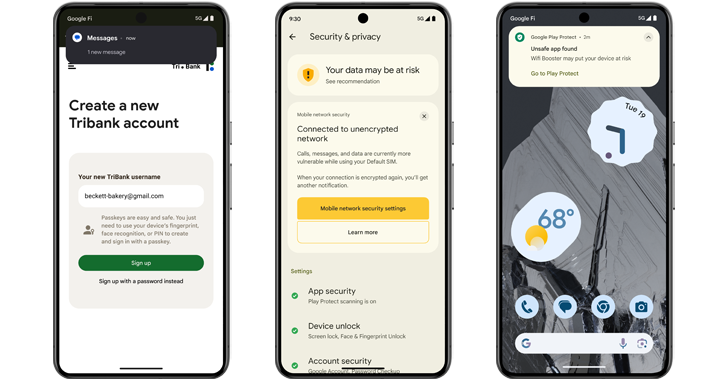
Read MoreMay 15, 2024NewsroomPrivacy / Data Protection Google has announced a slew of privacy and security features in Android, including a suite of advanced protection features to help secure users’ devices and data in the event of a theft. These features aim to help protect data before, during and after a theft attempt, the tech giant…
Read MoreMay 15, 2024NewsroomAndroid Security / Malware Google is unveiling a set of new features in Android 15 to prevent malicious apps installed on the device from capturing sensitive data. This constitutes an update to the Play Integrity API that third-party app developers can take advantage of to secure their applications against malware. “Developers can check…
Read MoreAn unnamed European Ministry of Foreign Affairs (MFA) and its three diplomatic missions in the Middle East were targeted by two previously undocumented backdoors tracked as LunarWeb and LunarMail. ESET, which identified the activity, attributed it with medium confidence to the Russia-aligned cyberespionage group Turla (aka Iron Hunter, Pensive Ursa, Secret Blizzard, Snake, Uroburos, and…
Read MoreHere’s How to Enhance Your Cyber Resilience with CVSS In late 2023, the Common Vulnerability Scoring System (CVSS) v4.0 was unveiled, succeeding the eight-year-old CVSS v3.0, with the aim to enhance vulnerability assessment for both industry and the public. This latest version introduces additional metrics like safety and automation to address criticism of lacking granularity…
Read MoreRecent Posts
- Bob Sullivan Discovers a Scam That Strikes Twice
- A Vulnerability in Apache Struts2 Could Allow for Remote Code Execution
- CISA Adds One Known Exploited Vulnerability to Catalog | CISA
- Xerox To Buy Lexmark For $1.5B In Blockbuster Print Deal
- Vulnerability Summary for the Week of December 16, 2024 | CISA