Tag: information security
Feb 28, 2024NewsroomFirmware Security / Vulnerability In a new joint advisory, cybersecurity and intelligence agencies from the U.S. and other countries are urging users of Ubiquiti EdgeRouter to take protective measures, weeks after a botnet comprising infected routers was felled by law enforcement as part of an operation codenamed Dying Ember. The botnet, named MooBot,…
Read MoreFeb 27, 2024NewsroomVulnerability / Website Security A security vulnerability has been disclosed in the LiteSpeed Cache plugin for WordPress that could enable unauthenticated users to escalate their privileges. Tracked as CVE-2023-40000, the vulnerability was addressed in October 2023 in version 5.7.0.1. “This plugin suffers from unauthenticated site-wide stored [cross-site scripting] vulnerability and could allow any…
Read MoreFeb 27, 2024The Hacker NewsMalware / Network Security An “intricately designed” remote access trojan (RAT) called Xeno RAT has been made available on GitHub, making it available to other actors at no extra cost. Written in C# and compatible with Windows 10 and Windows 11 operating systems, the open-source RAT comes with a “comprehensive set…
Read MoreFeb 27, 2024NewsroomSupply Chain Attack / Data Security Cybersecurity researchers have found that it’s possible to compromise the Hugging Face Safetensors conversion service to ultimately hijack the models submitted by users and result in supply chain attacks. “It’s possible to send malicious pull requests with attacker-controlled data from the Hugging Face service to any repository…
Read MoreProcessing alerts quickly and efficiently is the cornerstone of a Security Operations Center (SOC) professional’s role. Threat intelligence platforms can significantly enhance their ability to do so. Let’s find out what these platforms are and how they can empower analysts. The Challenge: Alert Overload The modern SOC faces a relentless barrage of security alerts generated…
Read MoreFeb 27, 2024NewsroomCloud Security / Threat Intelligence Cybersecurity and intelligence agencies from the Five Eyes nations have released a joint advisory detailing the evolving tactics of the Russian state-sponsored threat actor known as APT29. The hacking outfit, also known as BlueBravo, Cloaked Ursa, Cozy Bear, Midnight Blizzard (formerly Nobelium), and The Dukes, is assessed to…
Read MoreFeb 27, 2024NewsroomWebsite Security / Cryptojacking A critical security flaw has been disclosed in a popular WordPress plugin called Ultimate Member that has more than 200,000 active installations. The vulnerability, tracked as CVE-2024-1071, carries a CVSS score of 9.8 out of a maximum of 10. Security researcher Christiaan Swiers has been credited with discovering and…
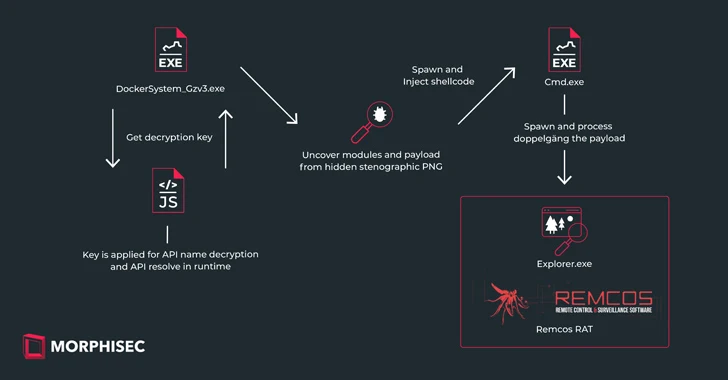
Read MoreFeb 26, 2024The Hacker NewsSteganography / Malware Ukrainian entities based in Finland have been targeted as part of a malicious campaign distributing a commercial remote access trojan known as Remcos RAT using a malware loader called IDAT Loader. The attack has been attributed to a threat actor tracked by the Computer Emergency Response Team of…
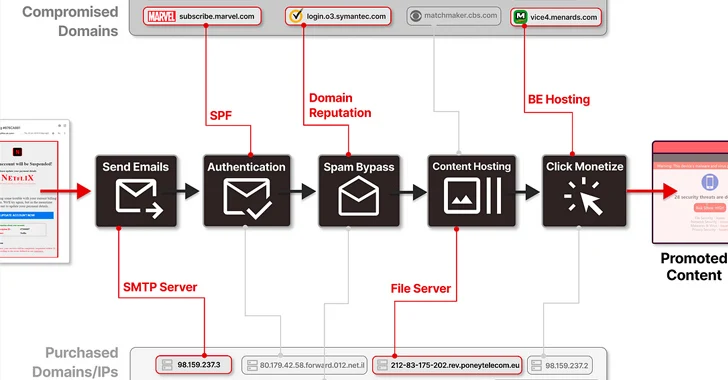
Read MoreMore than 8,000 subdomains belonging to legitimate brands and institutions have been hijacked as part of a sophisticated distribution architecture for spam proliferation and click monetization. Guardio Labs is tracking the coordinated malicious activity, which has been ongoing since at least September 2022, under the name SubdoMailing. The emails range from “counterfeit package delivery alerts…
Read MoreFeb 26, 2024The Hacker NewsSoftware Security / Cryptocurrency A set of fake npm packages discovered on the Node.js repository has been found to share ties with North Korean state-sponsored actors, new findings from Phylum show. The packages are named execution-time-async, data-time-utils, login-time-utils, mongodb-connection-utils, and mongodb-execution-utils. One of the packages in question, execution-time-async, masquerades as its…
Read MoreRecent Posts
- Arm To Seek Retrial In Qualcomm Case After Mixed Verdict
- Jury Sides With Qualcomm Over Arm In Case Related To Snapdragon X PC Chips
- Equinix Makes Dell AI Factory With Nvidia Available Through Partners
- AMD’s EPYC CPU Boss Seeks To Push Into SMB, Midmarket With Partners
- Fortinet Releases Security Updates for FortiManager | CISA