Tag: network security
Oct 26, 2024Ravie LakshmananCloud Security / Cryptocurrency The infamous cryptojacking group known as TeamTNT appears to be readying for a new large-scale campaign targeting cloud-native environments for mining cryptocurrencies and renting out breached servers to third-parties. “The group is currently targeting exposed Docker daemons to deploy Sliver malware, a cyber worm, and cryptominers, using compromised…
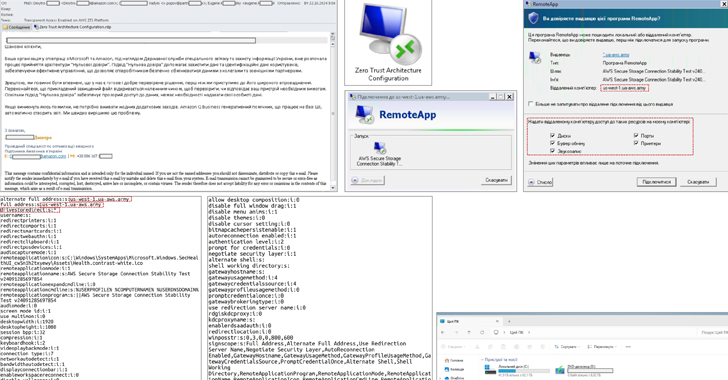
Read MoreOct 26, 2024Ravie LakshmananCyber Attack / Threat Intelligence The Computer Emergency Response Team of Ukraine (CERT-UA) has detailed a new malicious email campaign targeting government agencies, enterprises, and military entities. “The messages exploit the appeal of integrating popular services like Amazon or Microsoft and implementing a zero-trust architecture,” CERT-UA said. “These emails contain attachments in…
Read MoreOct 25, 2024Ravie LakshmananVulnerability / Wi-Fi Security A security flaw impacting the Wi-Fi Test Suite could enable unauthenticated local attackers to execute arbitrary code with elevated privileges. The CERT Coordination Center (CERT/CC) said the vulnerability, tracked as CVE-2024-41992, said the susceptible code from the Wi-Fi Alliance has been found deployed on Arcadyan FMIMG51AX000J routers. “This…
Read MoreOct 25, 2024Ravie LakshmananCloud Security / Artificial Intelligence Apple has publicly made available its Private Cloud Compute (PCC) Virtual Research Environment (VRE), allowing the research community to inspect and verify the privacy and security guarantees of its offering. PCC, which Apple unveiled earlier this June, has been marketed as the “most advanced security architecture ever…
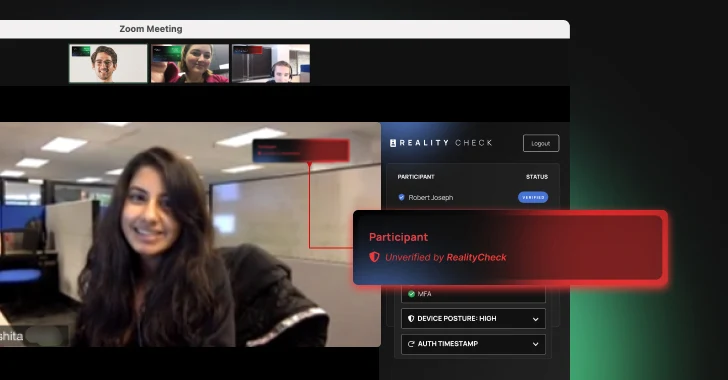
Read MoreOct 25, 2024The Hacker NewsArtificial Intelligence / Identity Security Artificial Intelligence (AI) has rapidly evolved from a futuristic concept to a potent weapon in the hands of bad actors. Today, AI-based attacks are not just theoretical threats—they’re happening across industries and outpacing traditional defense mechanisms. The solution, however, is not futuristic. It turns out a…
Read MoreOct 25, 2024Ravie LakshmananRegulatory Compliance / Data Breach The U.S. Securities and Exchange Commission (SEC) has charged four current and former public companies for making “materially misleading disclosures” related to the large-scale cyber attack that stemmed from the hack of SolarWinds in 2020. The SEC said the companies – Avaya, Check Point, Mimecast, and Unisys…
Read MoreOct 25, 2024Ravie LakshmananDigital Advertising / Privacy The Irish data protection watchdog on Thursday fined LinkedIn €310 million ($335 million) for violating the privacy of its users by conducting behavioral analyses of personal data for targeted advertising. “The inquiry examined LinkedIn’s processing of personal data for the purposes of behavioral analysis and targeted advertising of…
Read MoreOct 24, 2024Ravie LakshmananRansomware / Cybercrime Cybersecurity researchers have discovered an advanced version of the Qilin ransomware sporting increased sophistication and tactics to evade detection. The new variant is being tracked by cybersecurity firm Halcyon under the moniker Qilin.B. “Notably, Qilin.B now supports AES-256-CTR encryption for systems with AESNI capabilities, while still retaining Chacha20 for…
Read MoreA suspected nation-state campaign has been targeting FortiManager customers — likely including MSPs — since at least late June, according to security researchers. The attacks exploiting a critical-severity vulnerability in Fortinet FortiManager are likely targeting MSPs in a nation-state espionage campaign, according to a security researcher. In a post Tuesday, well-known researcher Kevin Beaumont noted…
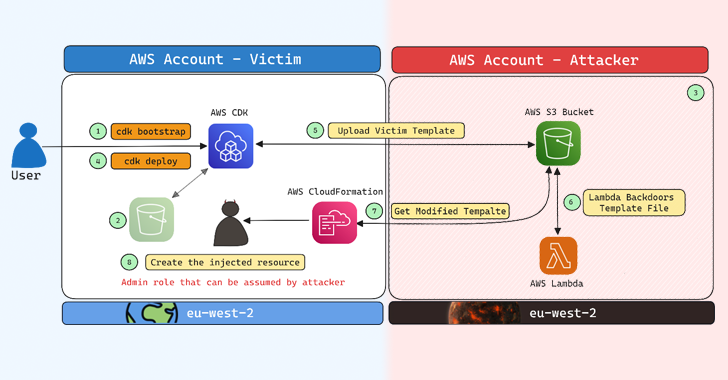
Read MoreCybersecurity researchers have disclosed a security flaw impacting Amazon Web Services (AWS) Cloud Development Kit (CDK) that could have resulted in an account takeover under specific circumstances. “The impact of this issue could, in certain scenarios, allow an attacker to gain administrative access to a target AWS account, resulting in a full account takeover,” Aqua…
Read MoreRecent Posts
- Bob Sullivan Discovers a Scam That Strikes Twice
- A Vulnerability in Apache Struts2 Could Allow for Remote Code Execution
- CISA Adds One Known Exploited Vulnerability to Catalog | CISA
- Xerox To Buy Lexmark For $1.5B In Blockbuster Print Deal
- Vulnerability Summary for the Week of December 16, 2024 | CISA