Tag: network security
The flaws impact Cisco Adaptive Security Appliance and Firepower Threat Defense software and have been exploited in a state-sponsored campaign against global governments as far back as November, the company says. Cisco Systems disclosed two zero-day firewall vulnerabilities Wednesday that the tech giant said have been exploited by a state-sponsored attacker in an espionage campaign…
Read More‘I think we’ve known for a long time that traditional voice had a shelf life. And ultimately it was going to get replaced with integrated communication services and as-a-service capabilities that run over the top of IP. Now we’re seeing that evolution pick up with a degree of steam,’ CEO John Stankey said of business…
Read MoreApr 24, 2024NewsroomMalware / Endpoint Security Cybersecurity researchers have discovered an ongoing attack campaign that’s leveraging phishing emails to deliver malware called SSLoad. The campaign, codenamed FROZEN#SHADOW by Securonix, also involves the deployment of Cobalt Strike and the ConnectWise ScreenConnect remote desktop software. “SSLoad is designed to stealthily infiltrate systems, gather sensitive information and transmit…
Read MoreApr 24, 2024NewsroomCyber Attack / Cyber Espionage The U.S. Treasury Department’s Office of Foreign Assets Control (OFAC) on Monday sanctioned two firms and four individuals for their involvement in malicious cyber activities on behalf of the Iranian Islamic Revolutionary Guard Corps Cyber Electronic Command (IRGC-CEC) from at least 2016 to April 2021. This includes the…
Read More‘Everybody else translates to risk right now. We are, right now, the company in networking. Our vision is clear, our execution is clear. We’re not distracted with an acquisition or something else. That’s translating into a lot of interest from the broader partner space,’ Extreme Networks’ chief product and technology officer tells CRN. There’s a…
Read MoreApr 24, 2024NewsroomEncryption / Mobile Security Security vulnerabilities uncovered in cloud-based pinyin keyboard apps could be exploited to reveal users’ keystrokes to nefarious actors. The findings come from the Citizen Lab, which discovered weaknesses in eight of nine apps from vendors like Baidu, Honor, iFlytek, OPPO, Samsung, Tencent, Vivo, and Xiaomi. The only vendor whose…
Read MoreA new malware campaign has been exploiting the updating mechanism of the eScan antivirus software to distribute backdoors and cryptocurrency miners like XMRig through a long-standing threat codenamed GuptiMiner targeting large corporate networks. Cybersecurity firm Avast said the activity is the work of a threat actor with possible connections to a North Korean hacking group…
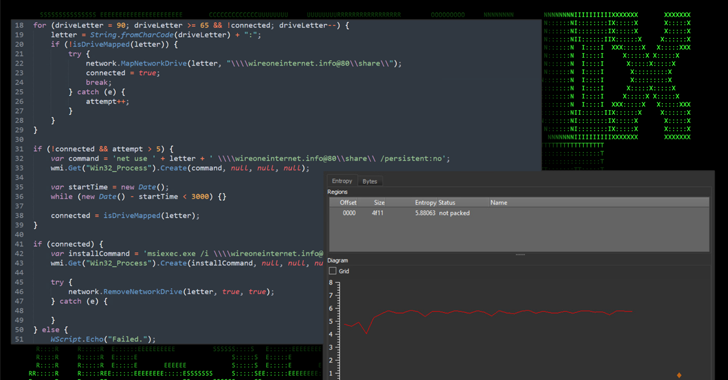
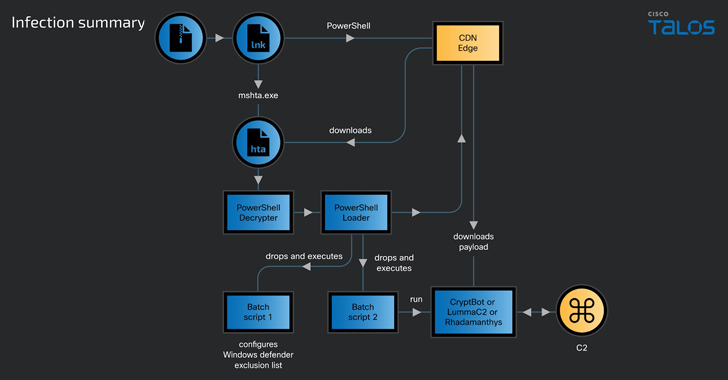
Read MoreApr 24, 2024NewsroomMalware / Data Security A new ongoing malware campaign has been observed distributing three different stealers, such as CryptBot, LummaC2, and Rhadamanthys hosted on Content Delivery Network (CDN) cache domains since at least February 2024. Cisco Talos has attributed the activity with moderate confidence to a threat actor tracked as CoralRaider, a suspected…
Read MoreApr 23, 2024NewsroomSupply Chain Attack / Application Security Researchers have identified a dependency confusion vulnerability impacting an archived Apache project called Cordova App Harness. Dependency confusion attacks take place owing to the fact that package managers check the public repositories before private registries, thus allowing a threat actor to publish a malicious package with the…
Read More“These access points have a role in not only networking for AI, but also AI for networking,” said HPE Aruba’s VP of product and community marketing Larry Lunetta, in reference to HPE Aruba’s acquisition target Juniper Networks’ CEO Rami Rahim’s own take that the industry is just scratching the surface with AI networking. HPE Aruba…
Read MoreRecent Posts
- CISA Releases the Cybersecurity Performance Goals Adoption Report | CISA
- Multiple vulnerabilities in SonicWall SonicOS could allow a remote attacker to bypass authentication.
- Dell Sales Leader, Former Channel Chief John Byrne Steps Down
- The Dangers of DNS Hijacking
- CES 2025: 15 PC Chips Announced By Intel, Nvidia, AMD And Qualcomm