Tag: network security
Nov 07, 2024Ravie LakshmananVulnerability / Wireless Technology Cisco has released security updates to address a maximum severity security flaw impacting Ultra-Reliable Wireless Backhaul (URWB) Access Points that could permit unauthenticated, remote attackers to run commands with elevated privileges. Tracked as CVE-2024-20418 (CVS score: 10.0), the vulnerability has been described as stemming from a lack of…
Read MoreNov 07, 2024Ravie LakshmananNational Security / Social Media The Canadian government on Wednesday ordered ByteDance-owned TikTok to dissolve its operations in the country, citing national security risks, but stopped short of instituting a ban on the popular video-sharing platform. “The decision was based on the information and evidence collected over the course of the review…
Read MoreNov 06, 2024Ravie LakshmananSaaS Security / Threat Detection An ongoing threat campaign dubbed VEILDrive has been observed taking advantage of legitimate services from Microsoft, including Teams, SharePoint, Quick Assist, and OneDrive, as part of its modus operandi. “Leveraging Microsoft SaaS services — including Teams, SharePoint, Quick Assist, and OneDrive — the attacker exploited the trusted…
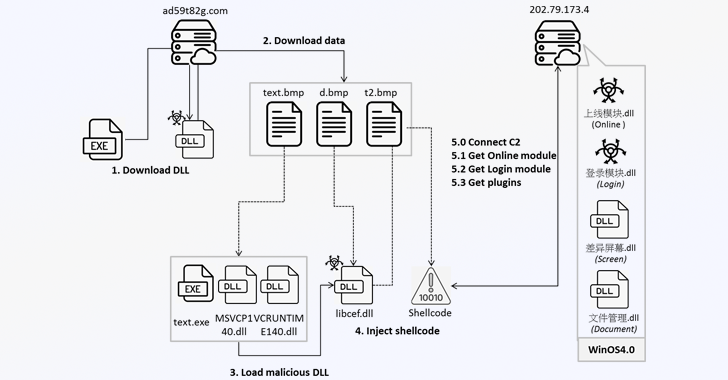
Read MoreNov 06, 2024Ravie LakshmananMalware / Online Security Cybersecurity researchers are warning that a command-and-control (C&C) framework called Winos is being distributed within gaming-related applications like installation tools, speed boosters, and optimization utilities. “Winos 4.0 is an advanced malicious framework that offers comprehensive functionality, a stable architecture, and efficient control over numerous online endpoints to execute…
Read MoreBudget season is upon us, and everyone in your organization is vying for their slice of the pie. Every year, every department has a pet project that they present as absolutely essential to profitability, business continuity, and quite possibly the future of humanity itself. And no doubt that some of these actually may be mission…
Read MoreNov 06, 2024Ravie LakshmananCyber Threat / Cybercrime INTERPOL on Tuesday said it took down more than 22,000 malicious servers linked to various cyber threats as part of a global operation. Dubbed Operation Synergia II, the coordinated effort ran from April 1 to August 31, 2024, targeting phishing, ransomware, and information stealer infrastructure. “Of the approximately…
Read MoreNov 06, 2024Ravie LakshmananData Privacy / Tech Regulation Meta has been fined 21.62 billion won ($15.67 million) by South Korea’s data privacy watchdog for illegally collecting sensitive personal information from Facebook users, including data about their political views and sexual orientation, and sharing it with advertisers without their consent. The country’s Personal Information Protection Commission…
Read More2024 Cyber Resilience Research Unveils Energy and Utilities Industry Challenges New data illuminates how energy and utilities leaders can prioritize resilience. Energy and utilities organizations find themselves at the intersection of progress and peril in the rapidly evolving digital landscape. The latest data underscores that the trade-offs are significant and pose substantial risks to utility…
Read MoreNov 06, 2024Ravie LakshmananCloud Security / Phishing Protection Google’s cloud division has announced that it will enforce mandatory multi-factor authentication (MFA) for all users by the end of 2025 as part of its efforts to improve account security. “We will be implementing mandatory MFA for Google Cloud in a phased approach that will roll out…
Read MoreCRN’s Gina Narcisi spoke about how Cisco’s new partner program, Cisco 360, will impact partners and what Cisco CEO Chuck Robbins had to tell her about the big changes – and big opportunities – for the channel at Cisco Partner Summit 2024. Jennifer Follett: I’m Jennifer Follett with CRN TV and this is CRN In…
Read MoreRecent Posts
- Bob Sullivan Discovers a Scam That Strikes Twice
- A Vulnerability in Apache Struts2 Could Allow for Remote Code Execution
- CISA Adds One Known Exploited Vulnerability to Catalog | CISA
- Xerox To Buy Lexmark For $1.5B In Blockbuster Print Deal
- Vulnerability Summary for the Week of December 16, 2024 | CISA