Tag: network security
Aug 15, 2024Ravie LakshmananEnterprise Security / Vulnerability SolarWinds has released patches to address a critical security vulnerability in its Web Help Desk software that could be exploited to execute arbitrary code on susceptible instances. The flaw, tracked as CVE-2024-28986 (CVSS score: 9.8), has been described as a deserialization bug. “SolarWinds Web Help Desk was found…
Read MoreAug 15, 2024Ravie LakshmananCyber Attack / Social Engineering Russian and Belarusian non-profit organizations, Russian independent media, and international non-governmental organizations active in Eastern Europe have become the target of two separate spear-phishing campaigns orchestrated by threat actors whose interests align with that of the Russian government. While one of the campaigns – dubbed River of…
Read MoreCisco CEO Chuck Robbins says his team is “shifting hundreds of millions of dollars into AI,” including AI networking for cloud, AI infrastructure, silicon and cybersecurity. Cisco Systems crossed $1 billion to date in AI orders with webscale customers and predicts another $1 billion in AI product orders this fiscal year. On the San Jose,…
Read MoreAug 15, 2024Ravie LakshmananRansomware / Cybercrime A cybercrime group with links to the RansomHub ransomware has been observed using a new tool designed to terminate endpoint detection and response (EDR) software on compromised hosts, joining the likes of other similar programs like AuKill (aka AvNeutralizer) and Terminator. The EDR-killing utility has been dubbed EDRKillShifter by…
Read MoreAug 15, 2024The Hacker NewsIdentity Security / Threat Detection The Emergence of Identity Threat Detection and Response Identity Threat Detection and Response (ITDR) has emerged as a critical component to effectively detect and respond to identity-based attacks. Threat actors have shown their ability to compromise the identity infrastructure and move laterally into IaaS, Saas, PaaS…
Read MoreAug 15, 2024Ravie LakshmananCyber Espionage / Data Theft A previously unknown threat actor has been attributed to a spate of attacks targeting Azerbaijan and Israel with an aim to steal sensitive data. The attack campaign, detected by NSFOCUS on July 1, 2024, leveraged spear-phishing emails to single out Azerbaijani and Israeli diplomats. The activity is…
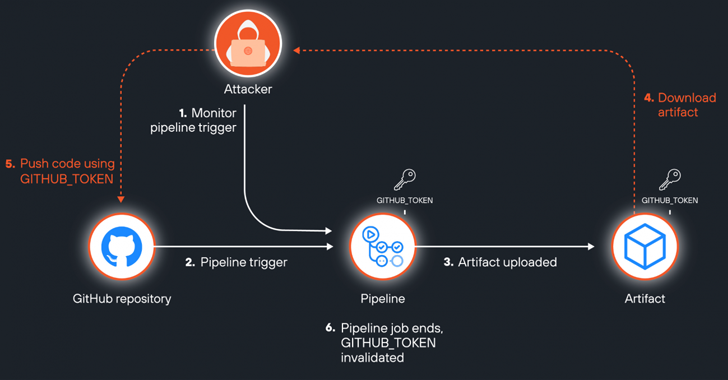
Read MoreAug 15, 2024Ravie LakshmananCloud Security / DevOps A newly discovered attack vector in GitHub Actions artifacts dubbed ArtiPACKED could be exploited to take over repositories and gain access to organizations’ cloud environments. “A combination of misconfigurations and security flaws can make artifacts leak tokens, both of third party cloud services and GitHub tokens, making them…
Read MoreAug 15, 2024Ravie LakshmananNetwork Security / Cybercrime Cybersecurity researchers have discovered a new variant of the Gafgyt botnet that’s targeting machines with weak SSH passwords to ultimately mine cryptocurrency on compromised instances using their GPU computational power. This indicates that the “IoT botnet is targeting more robust servers running on cloud native environments,” Aqua Security…
Read MoreCisco will spend between $700 million and $800 million in the first quarter of its 2025 fiscal year. Cisco Systems confirmed massive layoffs Wednesday with plans to cut about 7 percent of its global workforce, which should cost up to $1 billion. The San Jose, Calif.-based networking giant said in a regulatory filing that the…
Read MoreAug 14, 2024Ravie LakshmananMalware / Network Security An ongoing social engineering campaign with alleged links to the Black Basta ransomware group has been linked to “multiple intrusion attempts” with the goal of conducting credential theft and deploying a malware dropper called SystemBC. “The initial lure being utilized by the threat actors remains the same: an…
Read MoreRecent Posts
- CISA Releases the Cybersecurity Performance Goals Adoption Report | CISA
- Multiple vulnerabilities in SonicWall SonicOS could allow a remote attacker to bypass authentication.
- Dell Sales Leader, Former Channel Chief John Byrne Steps Down
- The Dangers of DNS Hijacking
- CES 2025: 15 PC Chips Announced By Intel, Nvidia, AMD And Qualcomm