Tag: network security
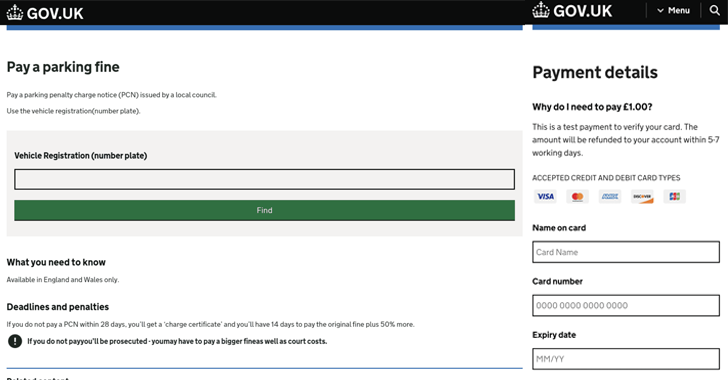
Cybersecurity researchers have disclosed a new phishing kit that has been put to use in campaigns targeting Australia, Japan, Spain, the U.K., and the U.S. since at least September 2024. Netcraft said more than 2,000 phishing websites have been identified the kit, known as Xiū gǒu, with the offering used in attacks aimed at a…
Read MoreNov 01, 2024The Hacker NewsSaaS Security / Identity Security Did you know that advanced threat actors can infiltrate the identity systems of major organizations and extract sensitive data within days? It’s a chilling reality, becoming more common and concerning by the day. These attackers exploit vulnerabilities in SaaS and cloud environments, using compromised identities to…
Read MoreCisco CEO Chuck Robbins weighed in on what the fully renovated Cisco 360 partner program means for partners, who tell CRN that the “devil will be in the details.” Cisco 360, revealed this week at Cisco Partner Summit 2024, marks the biggest overhaul to the partner program in the company’s history and partners are eager…
Read MoreOct 31, 2024Ravie LakshmananSpyware / Mobile Security Cybersecurity researchers have discovered an improved version of an Apple iOS spyware called LightSpy that not only expands on its functionality, but also incorporates destructive capabilities to prevent the compromised device from booting up. “While the iOS implant delivery method closely mirrors that of the macOS version, the…
Read MoreOct 31, 2024Ravie LakshmananCryptocurrency / Software Development LottieFiles has revealed that its npm package “lottie-player” was compromised as part of a supply chain attack, prompting it to release an updated version of the library. “On October 30th ~6:20 PM UTC – LottieFiles were notified that our popular open source npm package for the web player…
Read MoreOct 31, 2024The Hacker NewsIdentity Security / Browser Security In the modern, browser-centric workplace, the corporate identity acts as the frontline defense for organizations. Often referred to as “the new perimeter”, the identity stands between safe data management and potential breaches. However, a new report reveals how enterprises are often unaware of how their identities…
Read MoreOct 31, 2024Ravie LakshmananVulnerability / Website Security A high-severity security flaw has been disclosed in the LiteSpeed Cache plugin for WordPress that could allow an unauthenticated threat actor to elevate their privileges and perform malicious actions. The vulnerability, tracked as CVE-2024-50550 (CVSS score: 8.1), has been addressed in version 6.5.2 of the plugin. “The plugin…
Read MoreCisco’s executive leadership team this week had a lot to say about Cisco 360, the fully overhauled partner program. They also talked about the company’s transformation as it folds in Splunk. Cisco’s executive leadership team was out in full force at the tech giant’s partner summit this week in Los Angeles in a clear signal…
Read MoreOct 30, 2024Ravie LakshmananRansomware / Threat Intelligence Threat actors in North Korea have been implicated in a recent incident that deployed a known ransomware family called Play, underscoring their financial motivations. The activity, observed between May and September 2024, has been attributed to a threat actor tracked as Jumpy Pisces, which is also known as…
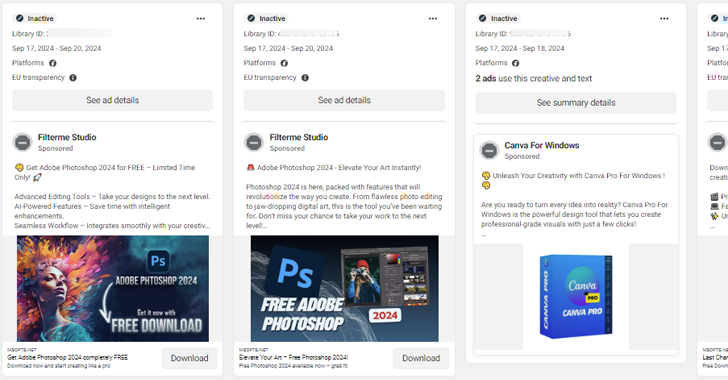
Read MoreCybersecurity researchers have uncovered an ongoing malvertising campaign that abuses Meta’s advertising platform and hijacked Facebook accounts to distribute information known as SYS01stealer. “The hackers behind the campaign use trusted brands to expand their reach,” Bitdefender Labs said in a report shared with The Hacker News. “The malvertising campaign leverages nearly a hundred malicious domains,…
Read MoreRecent Posts
- Bob Sullivan Discovers a Scam That Strikes Twice
- A Vulnerability in Apache Struts2 Could Allow for Remote Code Execution
- CISA Adds One Known Exploited Vulnerability to Catalog | CISA
- Xerox To Buy Lexmark For $1.5B In Blockbuster Print Deal
- Vulnerability Summary for the Week of December 16, 2024 | CISA