Tag: network security
Jun 18, 2024NewsroomNetwork Security / Vulnerability VMware has released updates to address critical flaws impacting Cloud Foundation, vCenter Server, and vSphere ESXi that could be exploited to achieve privilege escalation and remote code execution. The list of vulnerabilities is as follows – CVE-2024-37079 & CVE-2024-37080 (CVSS scores: 9.8) – Multiple heap-overflow vulnerabilities in the implementation…
Read MoreJun 18, 2024NewsroomMobile Security / Financial Fraud The Singapore Police Force (SPF) has announced the extradition of two men from Malaysia for their alleged involvement in a mobile malware campaign targeting citizens in the country since June 2023. The unnamed individuals, aged 26 and 47, engaged in scams that tricked unsuspecting users into downloading malicious…
Read MoreVirtusa, Redapt, Network Doctor, Microsoft, Amazon Web Services and Atlassian are among the companies to list open positions for channel-related roles. This month, Virtusa, Redapt and Network Doctor are among the solution providers to list open positions while Microsoft, Amazon Web Services and Atlassian are among the vendors to list open positions for channel-related roles.…
Read MoreJun 17, 2024NewsroomRouter Security / Vulnerability ASUS has shipped software updates to address a critical security flaw impacting its routers that could be exploited by malicious actors to bypass authentication. Tracked as CVE-2024-3080, the vulnerability carries a CVSS score of 9.8 out of a maximum of 10.0. “Certain ASUS router models have authentication bypass vulnerability,…
Read MoreHPE Aruba Is Recruiting Networking Data Center And Security Partners Ahead Of HPE’s $14B Acquisition of Juniper Networks
by nlqip
‘We are working closely with our distribution partners to try to recruit new partners especially in the security area and also around data center networking,’ says HPE Aruba Worldwide Channel Chief Lene Skov. With Hewlett Packard Enterprise’s blockbuster $14 billion acquisition of Juniper Networks on track to close later this year or early in 2025,…
Read MoreJun 17, 2024NewsroomCyber Espionage / Vulnerability A suspected China-nexus cyber espionage actor has been attributed as behind a prolonged attack against an unnamed organization located in East Asia for a period of about three years, with the adversary establishing persistence using legacy F5 BIG-IP appliances and using it as an internal command-and-control (C&C) for defense…
Read MoreTraditional application security practices are not effective in the modern DevOps world. When security scans are run only at the end of the software delivery lifecycle (either right before or after a service is deployed), the ensuing process of compiling and fixing vulnerabilities creates massive overhead for developers. The overhead that degrades velocity and puts…
Read MoreThe content of this post is solely the responsibility of the author. LevelBlue does not adopt or endorse any of the views, positions, or information provided by the author in this article. Summer is a time for relaxation, travel, and spending quality moments with family and friends. However, it is also peak season for cybercriminals…
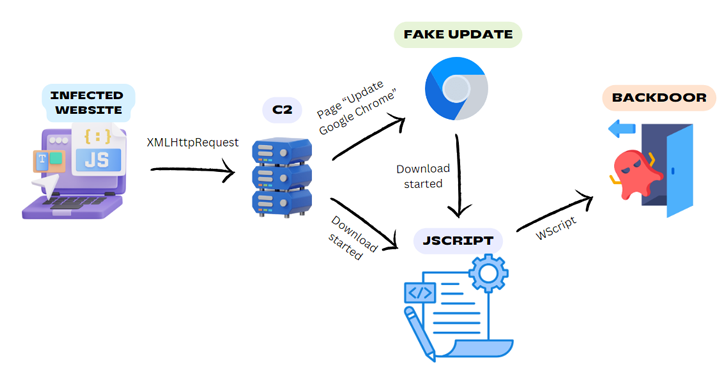
Read MoreJun 17, 2024NewsroomWeb Security / Malware Legitimate-but-compromised websites are being used as a conduit to deliver a Windows backdoor dubbed BadSpace under the guise of fake browser updates. “The threat actor employs a multi-stage attack chain involving an infected website, a command-and-control (C2) server, in some cases a fake browser update, and a JScript downloader…
Read MoreJun 17, 2024NewsroomBotnet / Cryptocurrency Threat actors have been observed deploying a malware called NiceRAT to co-opt infected devices into a botnet. The attacks, which target South Korean users, are designed to propagate the malware under the guise of cracked software, such as Microsoft Windows, or tools that purport to offer license verification for Microsoft…
Read MoreRecent Posts
- CISA Releases the Cybersecurity Performance Goals Adoption Report | CISA
- Multiple vulnerabilities in SonicWall SonicOS could allow a remote attacker to bypass authentication.
- Dell Sales Leader, Former Channel Chief John Byrne Steps Down
- The Dangers of DNS Hijacking
- CES 2025: 15 PC Chips Announced By Intel, Nvidia, AMD And Qualcomm