Tag: network security
The multi-cloud networking upstart is partnering with the “de facto” security leader Palo Alto Networks. The new relationship will give enterprises new approach to securing applications and workloads across multi-cloud environments, Prosimo execs told CRN. Multi-cloud networking upstart Prosimo is joining forces with security specialist Palo Alto Networks to further secure application access at a…
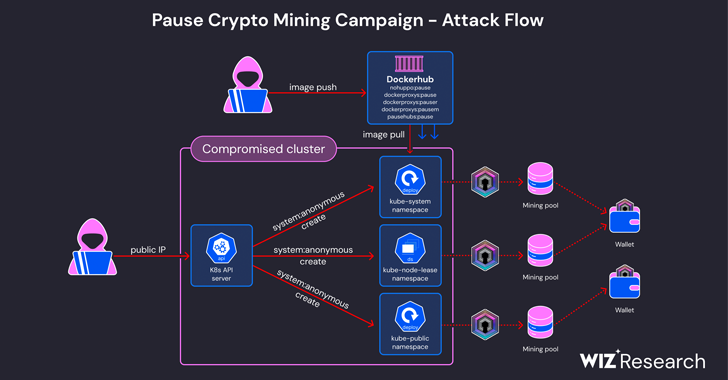
Read MoreJun 12, 2024NewsroomKubernetes / Endpoint Security Cybersecurity researchers have warned of an ongoing cryptojacking campaign targeting misconfigured Kubernetes clusters to mine Dero cryptocurrency. Cloud security firm Wiz, which shed light on the activity, said it’s an updated variant of a financially motivated operation that was first documented by CrowdStrike in March 2023. “In this incident,…
Read MoreAt Splunk .conf24, Cisco CEO Chuck Robbins and Go-to-Market President Gary Steele spoke to Splunk customers about the benefits of integrating the companies’ security and observability products and highlighted the opportunities those combinations will create for partners. Cisco Systems and Splunk executives are putting on a full-court press at Splunk .conf24 this week to tout…
Read MoreJun 12, 2024NewsroomRansomware / Endpoint Security Threat actors linked to the Black Basta ransomware may have exploited a recently disclosed privilege escalation flaw in the Microsoft Windows Error Reporting Service as zero-day, according to new findings from Symantec. The security flaw in question is CVE-2024-26169 (CVSS score: 7.8), an elevation of privilege bug in the…
Read MoreLast week, the notorious hacker gang, ShinyHunters, sent shockwaves across the globe by allegedly plundering 1.3 terabytes of data from 560 million Ticketmaster users. This colossal breach, with a price tag of $500,000, could expose the personal information of a massive swath of the live event company’s clientele, igniting a firestorm of concern and outrage.…
Read MoreJun 12, 2024Newsroom State-sponsored threat actors backed by China gained access to 20,000 Fortinet FortiGate systems worldwide by exploiting a known critical security flaw between 2022 and 2023, indicating that the operation had a broader impact than previously known. “The state actor behind this campaign was already aware of this vulnerability in FortiGate systems at…
Read MoreJun 12, 2024NewsroomCyber Attack / Malware Cybersecurity researchers have disclosed details of an ongoing phishing campaign that leverages recruiting- and job-themed lures to deliver a Windows-based backdoor named WARMCOOKIE. “WARMCOOKIE appears to be an initial backdoor tool used to scout out victim networks and deploy additional payloads,” Elastic Security Labs researcher Daniel Stepanic said in…
Read MoreJun 12, 2024NewsroomPatch Tuesday / Vulnerability Microsoft has released security updates to address 51 flaws as part of its Patch Tuesday updates for June 2024. Of the 51 vulnerabilities, one is rated Critical and 50 are rated Important. This is in addition to 17 vulnerabilities resolved in the Chromium-based Edge browser over the past month.…
Read MoreOne of the most effective ways for information technology (IT) professionals to uncover a company’s weaknesses before the bad guys do is penetration testing. By simulating real-world cyberattacks, penetration testing, sometimes called pentests, provides invaluable insights into an organization’s security posture, revealing weaknesses that could potentially lead to data breaches or other security incidents. Vonahi…
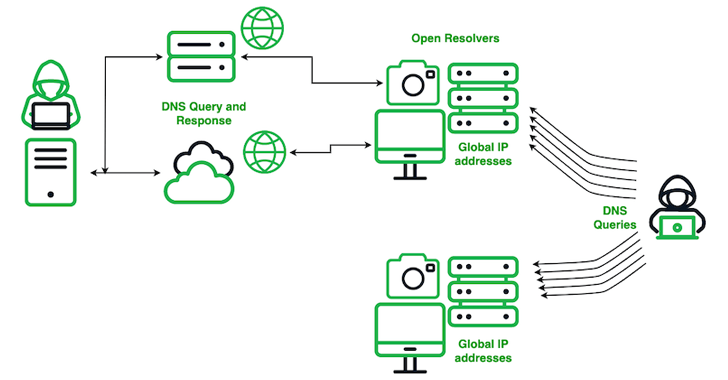
Read MoreCybersecurity researchers have shed more light on a Chinese actor codenamed SecShow that has been observed conducting Domain Name System (DNS) on a global scale since at least June 2023. The adversary, according to Infoblox security researchers Dr. Renée Burton and Dave Mitchell, operates from the China Education and Research Network (CERNET), a project funded…
Read MoreRecent Posts
- CISA Releases the Cybersecurity Performance Goals Adoption Report | CISA
- Multiple vulnerabilities in SonicWall SonicOS could allow a remote attacker to bypass authentication.
- Dell Sales Leader, Former Channel Chief John Byrne Steps Down
- The Dangers of DNS Hijacking
- CES 2025: 15 PC Chips Announced By Intel, Nvidia, AMD And Qualcomm