Tag: ransomware malware
Oct 15, 2024Ravie LakshmananFinancial Fraud / Linux North Korean threat actors have been observed using a Linux variant of a known malware family called FASTCash to steal funds as part of a financially-motivated campaign. The malware is “installed on payment switches within compromised networks that handle card transactions for the means of facilitating the unauthorized…
Read MoreOct 15, 2024Ravie LakshmananMalware / Cybercrime Cybersecurity researchers have disclosed a new malware campaign that leverages a malware loader named PureCrypter to deliver a commodity remote access trojan (RAT) called DarkVision RAT. The activity, observed by Zscaler ThreatLabz in July 2024, involves a multi-stage process to deliver the RAT payload. “DarkVision RAT communicates with its…
Read MoreIn recent years, the number and sophistication of zero-day vulnerabilities have surged, posing a critical threat to organizations of all sizes. A zero-day vulnerability is a security flaw in software that is unknown to the vendor and remains unpatched at the time of discovery. Attackers exploit these flaws before any defensive measures can be implemented,…
Read MoreChina’s National Computer Virus Emergency Response Center (CVERC) has doubled down on claims that the threat actor known as the Volt Typhoon is a fabrication of the U.S. and its allies. The agency, in collaboration with the National Engineering Laboratory for Computer Virus Prevention Technology, went on to accuse the U.S. federal government, intelligence agencies,…
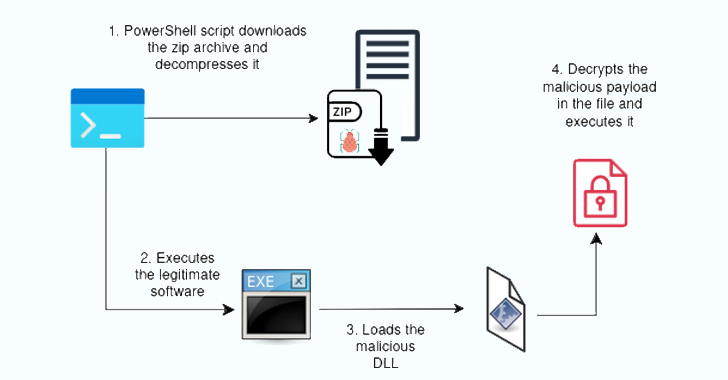
Read MoreOct 15, 2024Ravie LakshmananThreat Detection / Malware Cybersecurity researchers have disclosed a new malware campaign that delivers Hijack Loader artifacts that are signed with legitimate code-signing certificates. French cybersecurity company HarfangLab, which detected the activity at the start of the month, said the attack chains aim to deploy an information stealer known as Lumma. Hijack…
Read MoreThe maintainers of the Jetpack WordPress plugin have released a security update to remediate a critical vulnerability that could allow logged-in users to access forms submitted by others on a site. Jetpack, owned by WordPress maker Automattic, is an all-in-one plugin that offers a comprehensive suite of tools to improve site safety, performance, and traffic…
Read MoreOct 14, 2024Ravie LakshmananRecap / Cybersecurity Hey there, it’s your weekly dose of “what the heck is going on in cybersecurity land” – and trust me, you NEED to be in the loop this time. We’ve got everything from zero-day exploits and AI gone rogue to the FBI playing crypto kingpin – it’s full of…
Read MoreCybersecurity researchers have found that entry points could be abused across multiple programming ecosystems like PyPI, npm, Ruby Gems, NuGet, Dart Pub, and Rust Crates to stage software supply chain attacks. “Attackers can leverage these entry points to execute malicious code when specific commands are run, posing a widespread risk in the open-source landscape,” Checkmarx…
Read MoreOct 14, 2024The Hacker NewsCloud Security / Vulnerability The link between detection and response (DR) practices and cloud security has historically been weak. As global organizations increasingly adopt cloud environments, security strategies have largely focused on “shift-left” practices—securing code, ensuring proper cloud posture, and fixing misconfigurations. However, this approach has led to an over-reliance on…
Read MoreOct 14, 2024Ravie LakshmananNetwork Security / Vulnerability A suspected nation-state adversary has been observed weaponizing three security flaws in Ivanti Cloud Service Appliance (CSA) a zero-day to perform a series of malicious actions. That’s according to findings from Fortinet FortiGuard Labs, which said the vulnerabilities were abused to gain unauthenticated access to the CSA, enumerate…
Read MoreRecent Posts
- Microsoft rolls out Recall to Windows Insiders with Copilot+ PCs
- Five Companies That Came To Win This Week
- The 10 Hottest Semiconductor Startups Of 2024
- Cybersecurity Snapshot: Prompt Injection and Data Disclosure Top OWASP’s List of Cyber Risks for GenAI LLM Apps
- Healthcare Ransomware Attacks: How to Prevent and Respond Effectively | BlackFog