Tag: software vulnerability
Compliance requirements are meant to increase cybersecurity transparency and accountability. As cyber threats increase, so do the number of compliance frameworks and the specificity of the security controls, policies, and activities they include. For CISOs and their teams, that means compliance is a time-consuming, high-stakes process that demands strong organizational and communication skills on top…
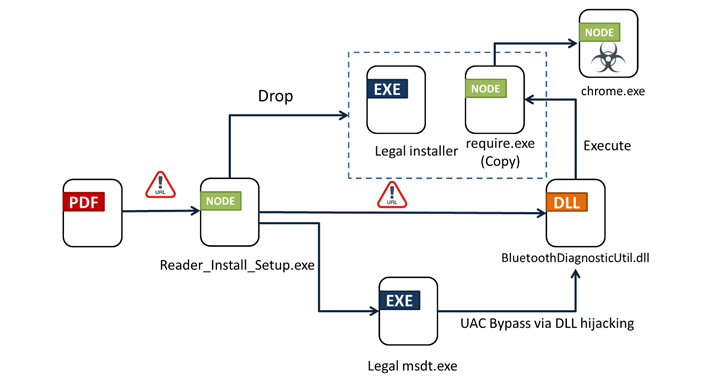
Read MoreApr 05, 2024NewsroomMalware / Endpoint Security Bogus installers for Adobe Acrobat Reader are being used to distribute a new multi-functional malware dubbed Byakugan. The starting point of the attack is a PDF file written in Portuguese that, when opened, shows a blurred image and asks the victim to click on a link to download the…
Read MoreApr 05, 2024NewsroomAdvanced Persistent Threat Multiple China-nexus threat actors have been linked to the zero-day exploitation of three security flaws impacting Ivanti appliances (CVE-2023-46805, CVE-2024-21887, and CVE-2024-21893). The clusters are being tracked by Mandiant under the monikers UNC5221, UNC5266, UNC5291, UNC5325, UNC5330, and UNC5337. Another group linked to the exploitation spree is UNC3886. The Google…
Read MoreApr 05, 2024NewsroomCyber Espionage / Cybersecurity Financial organizations in the Asia-Pacific (APAC) and Middle East and North Africa (MENA) are being targeted by a new version of an “evolving threat” called JSOutProx. “JSOutProx is a sophisticated attack framework utilizing both JavaScript and .NET,” Resecurity said in a technical report published this week. “It employs the…
Read MoreApr 04, 2024NewsroomPhishing Attack / Malware An updated version of an information-stealing malware called Rhadamanthys is being used in phishing campaigns targeting the oil and gas sector. “The phishing emails use a unique vehicle incident lure and, in later stages of the infection chain, spoof the Federal Bureau of Transportation in a PDF that mentions…
Read MoreA suspected Vietnamese-origin threat actor has been observed targeting victims in several Asian and Southeast Asian countries with malware designed to harvest valuable data since at least May 2023. Cisco Talos is tracking the cluster under the name CoralRaider, describing it as financially motivated. Targets of the campaign include India, China, South Korea, Bangladesh, Pakistan,…
Read MoreApr 04, 2024NewsroomVulnerability / Internet Protocol New research has found that the CONTINUATION frame in the HTTP/2 protocol can be exploited to conduct denial-of-service (DoS) attacks. The technique has been codenamed HTTP/2 CONTINUATION Flood by security researcher Bartek Nowotarski, who reported the issue to the CERT Coordination Center (CERT/CC) on January 25, 2024. “Many HTTP/2…
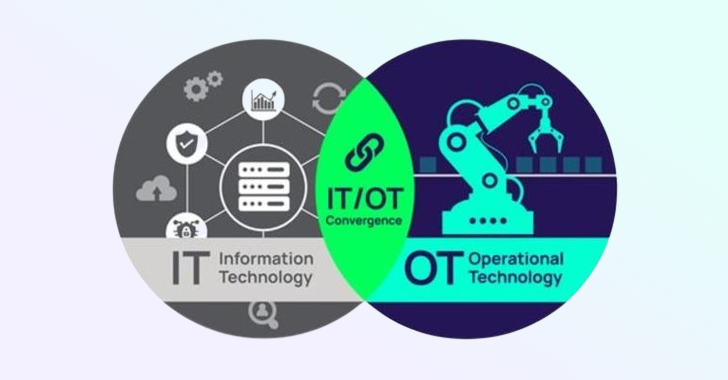
Read MoreOperational Technology (OT) refers to the hardware and software used to change, monitor, or control the enterprise’s physical devices, processes, and events. Unlike traditional Information Technology (IT) systems, OT systems directly impact the physical world. This unique characteristic of OT brings additional cybersecurity considerations not typically present in conventional IT security architectures. The convergence of…
Read MoreApr 04, 2024NewsroomNetwork Security / Vulnerability Ivanti has released security updates to address four security flaws impacting Connect Secure and Policy Secure Gateways that could result in code execution and denial-of-service (DoS). The list of flaws is as follows – CVE-2024-21894 (CVSS score: 8.2) – A heap overflow vulnerability in the IPSec component of Ivanti…
Read MoreApr 03, 2024NewsroomMobile Security / Zero Day Google has disclosed that two Android security flaws impacting its Pixel smartphones have been exploited in the wild by forensic companies. The high-severity zero-day vulnerabilities are as follows – CVE-2024-29745 – An information disclosure flaw in the bootloader component CVE-2024-29748 – A privilege escalation flaw in the firmware…
Read MoreRecent Posts
- Google Cloud Hires Tech Superstar Francis DeSouza As New COO
- AWS Invests $11B In Georgia To ‘Support The Future Of AI’ Via Data Centers
- Google’s Willow Quantum Chip and Its Potential Threat to…
- Citrix Parent Cloud Software Group Confirms Layoffs
- Nvidia Seeks To Turbocharge AI PC Development With GeForce RTX 50 GPUs