Tag: software vulnerability
Oct 14, 2024Ravie LakshmananRansomware / Vulnerability Threat actors are actively attempting to exploit a now-patched security flaw in Veeam Backup & Replication to deploy Akira and Fog ransomware. Cybersecurity vendor Sophos said it has been tracking a series of attacks in the past month leveraging compromised VPN credentials and CVE-2024-40711 to create a local account…
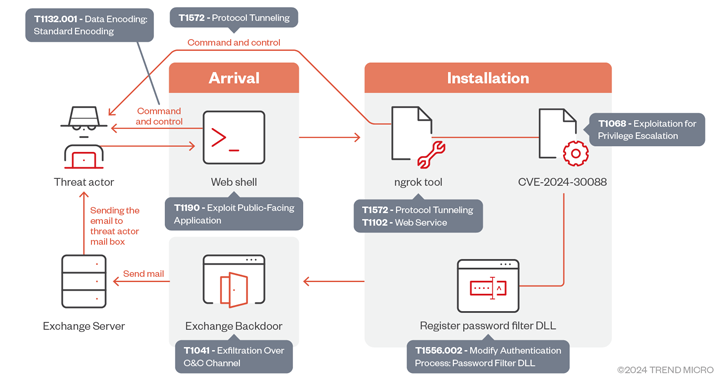
Read MoreOct 13, 2024Ravie Lakshmanan The Iranian threat actor known as OilRig has been observed exploiting a now-patched privilege escalation flaw impacting the Windows Kernel as part of a cyber espionage campaign targeting the U.A.E. and the broader Gulf region. “The group utilizes sophisticated tactics that include deploying a backdoor that leverages Microsoft Exchange servers for…
Read MoreOct 12, 2024Ravie LakshmananCryptocurrency / Cybercrime The U.S. Department of Justice (DoJ) has announced arrests and charges against several individuals and entities in connection with allegedly manipulating digital asset markets as part of a widespread fraud operation. The law enforcement action – codenamed Operation Token Mirrors – is the result of the U.S. Federal Bureau…
Read MoreA new tax-themed malware campaign targeting insurance and finance sectors has been observed leveraging GitHub links in phishing email messages as a way to bypass security measures and deliver Remcos RAT, indicating that the method is gaining traction among threat actors. “In this campaign, legitimate repositories such as the open-source tax filing software, UsTaxes, HMRC,…
Read MoreThreat actors constantly change tactics to bypass cybersecurity measures, developing innovative methods to steal user credentials. Hybrid password attacks merge multiple cracking techniques to amplify their effectiveness. These combined approaches exploit the strengths of various methods, accelerating the password-cracking process. In this post, we’ll explore hybrid attacks — what they are and the most common…
Read MoreOct 11, 2024Ravie LakshmananVulnerability / Network Security The U.S. Cybersecurity and Infrastructure Security Agency (CISA) is warning that it has observed threat actors leveraging unencrypted persistent cookies managed by the F5 BIG-IP Local Traffic Manager (LTM) module to conduct reconnaissance of target networks. It said the module is being used to enumerate other non-internet-facing devices…
Read MoreOct 11, 2024Ravie LakshmananDevOps / Vulnerability GitLab has released security updates for Community Edition (CE) and Enterprise Edition (EE) to address eight security flaws, including a critical bug that could allow running Continuous Integration and Continuous Delivery (CI/CD) pipelines on arbitrary branches. Tracked as CVE-2024-9164, the vulnerability carries a CVSS score of 9.6 out of…
Read MoreOct 11, 2024Ravie LakshmananCybercrime / Dark Web The Dutch police have announced the takedown of Bohemia and Cannabia, which has been described as the world’s largest and longest-running dark web market for illegal goods, drugs, and cybercrime services. The takedown is the result of a collaborative investigation with Ireland, the United Kingdom, and the United…
Read MoreOct 10, 2024Ravie LakshmananCybercrime / Disinformation OpenAI on Wednesday said it has disrupted more than 20 operations and deceptive networks across the world that attempted to use its platform for malicious purposes since the start of the year. This activity encompassed debugging malware, writing articles for websites, generating biographies for social media accounts, and creating…
Read MoreOct 10, 2024Ravie LakshmananVulnerability / Enterprise Security Cybersecurity security researchers are warning about an unpatched vulnerability in Nice Linear eMerge E3 access controller systems that could allow for the execution of arbitrary operating system (OS) commands. The flaw, assigned the CVE identifier CVE-2024-9441, carries a CVSS score of 9.8 out of a maximum of 10.0,…
Read More