Tag: software vulnerability
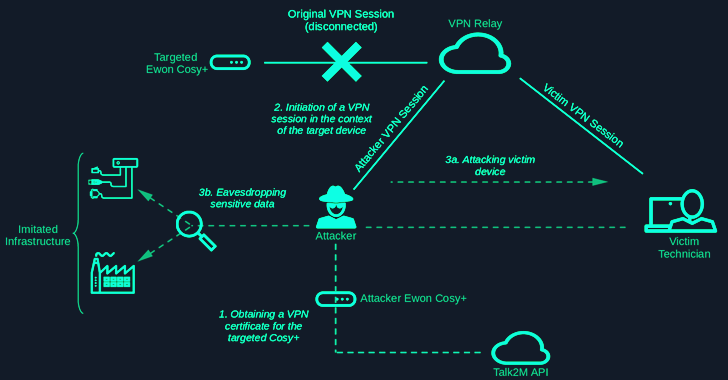
Aug 12, 2024Ravie LakshmananOperational Technology / Network Security Security vulnerabilities have been disclosed in the industrial remote access solution Ewon Cosy+ that could be abused to gain root privileges to the devices and stage follow-on attacks. The elevated access could then be weaponized to decrypt encrypted firmware files and encrypted data such as passwords in…
Read MoreAug 12, 2024Ravie LakshmananCloud Security / Malware The Russian government and IT organizations are the target of a new campaign that delivers a number of backdoors and trojans as part of a spear-phishing campaign codenamed EastWind. The attack chains are characterized by the use of RAR archive attachments containing a Windows shortcut (LNK) file that,…
Read MoreAug 11, 2024Ravie LakshmananSupply Chain / Software Security Cybersecurity researchers have discovered a new malicious package on the Python Package Index (PyPI) repository that masquerades as a library from the Solana blockchain platform but is actually designed to steal victims’ secrets. “The legitimate Solana Python API project is known as ‘solana-py’ on GitHub, but simply…
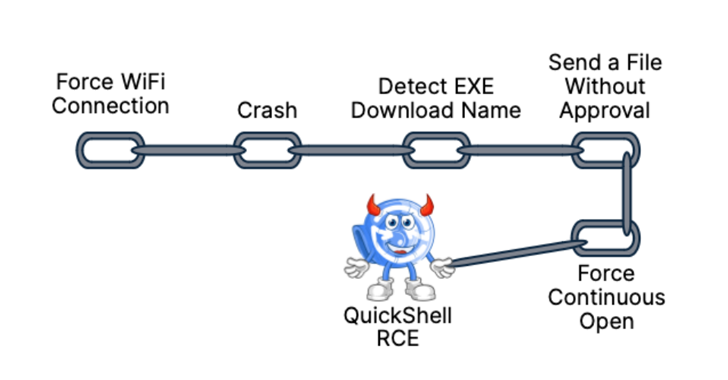
Read MoreAug 10, 2024Ravie LakshmananVulnerability / Mobile Security As many as 10 security flaws have been uncovered in Google’s Quick Share data transfer utility for Android and Windows that could be assembled to trigger remote code execution (RCE) chain on systems that have the software installed. “The Quick Share application implements its own specific application-layer communication…
Read MoreAug 10, 2024Ravie LakshmananBrowser Security / Online Fraud An ongoing, widespread malware campaign has been observed installing rogue Google Chrome and Microsoft Edge extensions via a trojan distributed via fake websites masquerading as popular software. “The trojan malware contains different deliverables ranging from simple adware extensions that hijack searches to more sophisticated malicious scripts that…
Read MoreAug 10, 2024Ravie LakshmananVulnerability / Enterprise Security Microsoft has disclosed an unpatched zero-day in Office that, if successfully exploited, could result in unauthorized disclosure of sensitive information to malicious actors. The vulnerability, tracked as CVE-2024-38200 (CVSS score: 7.5), has been described as a spoofing flaw that affects the following versions of Office – Microsoft Office…
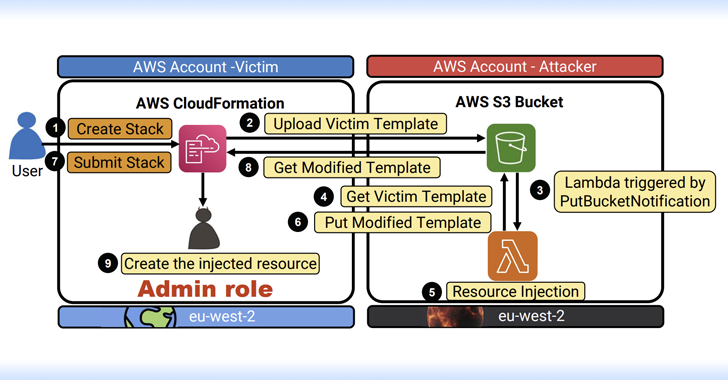
Read MoreAug 09, 2024Ravie LakshmananCloud Security / Data Protection Cybersecurity researchers have discovered multiple critical flaws in Amazon Web Services (AWS) offerings that, if successfully exploited, could result in serious consequences. “The impact of these vulnerabilities range between remote code execution (RCE), full-service user takeover (which might provide powerful administrative access), manipulation of AI modules, exposing…
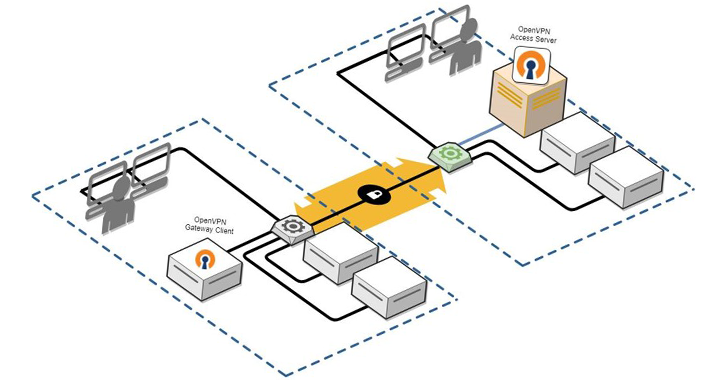
Read MoreAug 09, 2024Ravie LakshmananVulnerability / Network Security Microsoft on Thursday disclosed four medium-severity security flaws in the open-source OpenVPN software that could be chained to achieve remote code execution (RCE) and local privilege escalation (LPE). “This attack chain could enable attackers to gain full control over targeted endpoints, potentially resulting in data breaches, system compromise,…
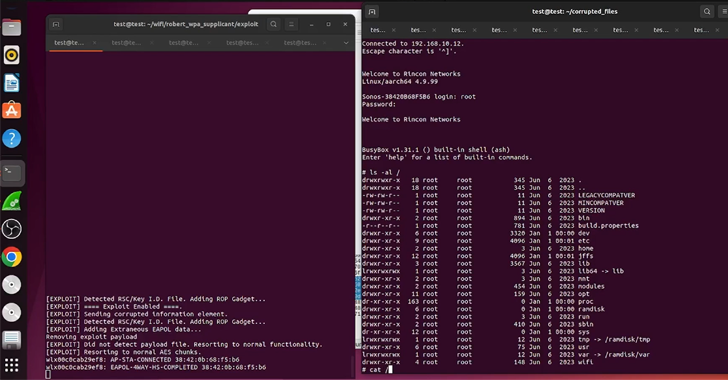
Read MoreAug 09, 2024Ravie LakshmananIoT Security / Wireless Security Cybersecurity researchers have uncovered weaknesses in Sonos smart speakers that could be exploited by malicious actors to clandestinely eavesdrop on users. The vulnerabilities “led to an entire break in the security of Sonos’s secure boot process across a wide range of devices and remotely being able to…
Read MoreAug 09, 2024Ravie LakshmananNational Security / Identity Theft The U.S. Department of Justice (DoJ) on Thursday charged a 38-year-old individual from Nashville, Tennessee, for allegedly running a “laptop farm” to help get North Koreans remote jobs with American and British companies. Matthew Isaac Knoot is charged with conspiracy to cause damage to protected computers, conspiracy…
Read MoreRecent Posts
- CISA Releases the Cybersecurity Performance Goals Adoption Report | CISA
- Multiple vulnerabilities in SonicWall SonicOS could allow a remote attacker to bypass authentication.
- Dell Sales Leader, Former Channel Chief John Byrne Steps Down
- The Dangers of DNS Hijacking
- CES 2025: 15 PC Chips Announced By Intel, Nvidia, AMD And Qualcomm